- Why I recommend this OnePlus phone over the S25 Ultra - especially at this new low price
- I replaced my laptop with Microsoft's 12-inch Surface Pro for weeks - here's my buying advice now
- This palm recognition smart lock doubles as a video doorbell (and has no monthly fees)
- Samsung is giving these Galaxy phones a big One UI upgrade - here's which models qualify
- 7 MagSafe accessories that I recommend every iPhone user should have
2024 Exposed: The Alarming State of Australian Data Breaches

The Office of the Australian Information Commissioner’s latest Notifiable Data Breaches Report revealed a rapid rise nationwide in notifiable data breaches in the first six months of 2024 — a 9% increase when compared with the final six months of 2023 and the highest number of notifications since 2020.
The report, released in September, showed that recent data breaches, including the beach of medical prescription service MediSecure affecting 12.9 million Australians, have prompted a strong response from the OAIC. The agency warned that it is adopting a tougher stance on data privacy and breaches, emphasising that organisations must prioritise privacy in their data practices.
Which industries experienced the most data breaches?
The OAIC has published statistical information on data breach notifications since the launch of the Notifiable Data Breaches scheme in Australia in 2018. The latest report revealed:
- A total of 527 notifications occurred from January to June 2024, marking a 9% increase when compared with the 485 notifications received from July to December 2023.
- The most recent six-month period saw the highest number of notifications received since July to December 2020, during the depths of the global COVID-19 pandemic.
- The top five sectors suffering data breaches were health service providers (102 breaches), the Australian Government (63), finance (58), education (44), and retail (29).
- Malicious or criminal attacks, both external and internal, were the source of 67% of all data breaches, followed by human error (30%) and system faults (3%).
- Malicious or criminal attacks included cyber incidents (57%), social engineering/impersonation (27%), theft of paperwork or data storage (8%), and rogue employee/insider threats (8%).
- Most breaches reported (63%) involved 100 people or fewer, but there were eight large-scale breaches impacting over 100,000 people, including Australia’s “largest ever” MediSecure breach.
SEE: Australian organisations experiencing highest rate of data breaches
Cyber incidents dominate malicious and criminal attacks in Australia
Cyber incidents continue to be a prevalent cause of data breaches, representing 38% of total breaches. Cyber incidents were defined as those including phishing, ransomware, compromised or stolen credentials (method unknown), brute-force attacks, hacking, and malware — but not social engineering-style attacks.
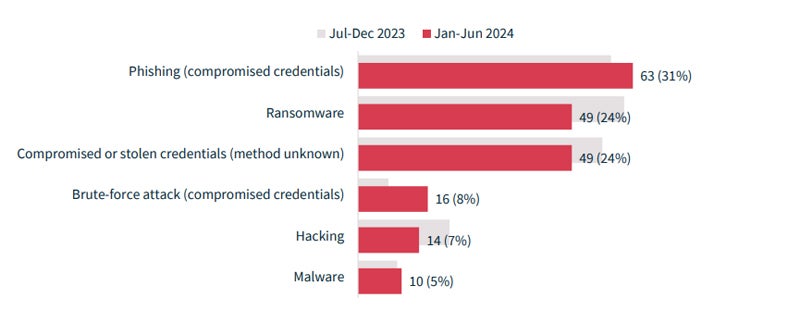
Among the various malicious or criminal attacks, cyber incidents had the greatest impact on individuals. The average of 107,123 individuals were affected by the 201 cyber incidents, while an average of 4,709 individuals were impacted by incidents caused by rogue employees or insider threats.
In the report, Australian Privacy Commissioner Carly Kind said that the continued prevalence of cyber incidents in the data breach totals reported to the OAIC came “as our increasing reliance on digital tools and online services exposes our details more frequently to malicious cyber actors.”
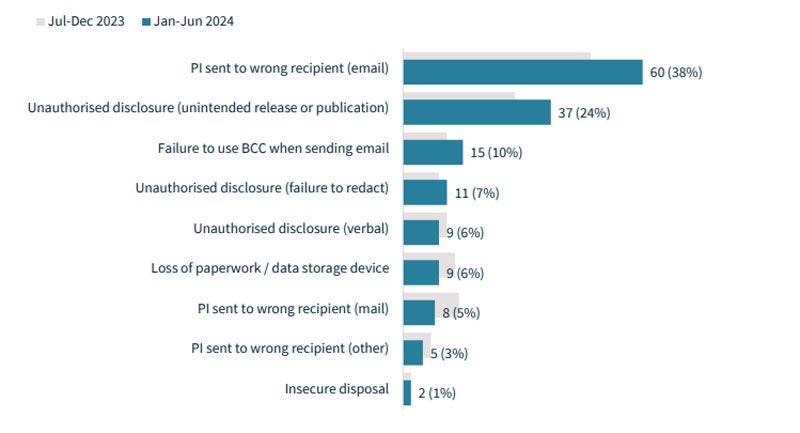
However, human error still accounts for 30% of notifiable data breaches. The top categories of human error were:
- Personally identifiable information sent to the wrong email recipient (38%).
- Unauthorised disclosure of information, or unintended release or publication (24%).
- Failure to use the Bcc (Blind copy) option when sending email (10%).
Spike in data breaches puts Australian Government agencies in spotlight
The OAIC noted that the Australian Government reported the second highest number of data breaches of all sectors, its highest position ever, though it has previously featured in the top five breached sectors. According to the report:
- Government agencies reported 63 data breaches from January to June 2024, accounting for 12% of all data breach notifications in Australia.
- The Government accounted for the highest number of social engineering or impersonation-style data breaches, making up 42% of such incidents. According to the OAIC, these breaches typically involved a threat actor impersonating a customer to gain access to an account using legitimate credentials.
- The Government is also slower to act: it had the largest proportion (87%) of notifications where the agency identified the incident over 30 days after it occurred, while 78% of Government notifications were made more than 30 days after the agency became aware of the incident.
SEE: Is Australia’s public sector ready for a major cyber security incident?
How can organisations stop data breaches?
Security experts continually remind organisations that many data breaches or cyber attacks could be prevented by implementing basic cyber security measures. The OAIC presented several recommendations based on trends in data breach data.
Mitigating cyber threats
The OAIC recommended implementing multi-factor authentication as a first priority to stop cyber threats, or strong password management policies and practices if MFA is unavailable. The agency also recommended:
- Implementing layer security controls to avoid a single point of failure.
- Enforcing levels of access to information based on roles and responsibilities.
- Leveraging security monitoring to detect, respond to, and report incidents or unusual activity.
The OAIC pointed to frameworks including Australia’s Essential Eight, the Australian Signals Directorate’s Information Security Manual, the U.S.-based National Institute of Standards and Technology’s Cyber Security Framework, as well as the International Organisation for Standardisation’s ISO 27001 and ISO 27002 information security management standards as measures to guide improvement in practices.
Extended supply chain risks
According to the OAIC, some large-scale data breaches are being caused by supply chain compromises, such as the breach impacting MediSecure and another incident involving Outabox. The agency added that outsourcing the handling of personal information to third parties remains a prevalent risk.
The agency said companies should consider the risks of outsourcing the handling of personal information at the earliest stage of procurement, including to cloud providers. It also recommended that organisations put in place a robust supplier risk-management framework, alongside more robust security measures.
Addressing the human factor
The OAIC emaphsised that individuals remain a significant threat to the strength of privacy practices. These threats include breaches due to human error or employees being tricked by phishing.
The agency urged organisations to implement technical measures to reduce errors and emphasized that educating staff is essential to ensure they understand their privacy and security obligations. It also recommended prioritising training staff in secure information handling practices.
Misconfiguration of cloud-based data holdings
Some organisations are “overlooking” cloud security as they digitally transform, the OAIC said. Various data breaches during the quarter happened when an Australian entity misconfigured security settings due to human error, leaving personal information vulnerable to unauthorised access or public disclosure.
The OAIC said organisations should not assume cloud security responsibility lies with the provider. The agency pointed out that cloud security and management should be a priority, highlighting the importance of measures such as secure access controls through MFA, IP access controls, and encryption.

