- I tested a Pixel Tablet without any Google apps, and it's more private than even my iPad
- My search for the best MacBook docking station is over. This one can power it all
- This $500 Motorola proves you don't need to spend more on flagship phones
- Finally, budget wireless earbuds that I wouldn't mind putting my AirPods away for
- I replaced my Linux system with this $200 Windows mini PC - and it left me impressed
Control Across Your Hybrid Environments Using Cisco Secure Workload 3.6 – Cisco Blogs

Business needs are driving significant changes in today’s datacenters. Enterprises are not only migrating applications to the cloud from on-premises data centers, but they are developing multicloud strategies that take advantage of availability, global footprint, and cost saving structures. In fact, IDC has predicted that more than 90% of IT organizations will commit to multicloud architectures by 2022.
In addition, datacenters are running applications in a mix of heterogenous private, public and hybrid cloud computing environments, leveraging bare-metal, virtualized, and container-based workloads. Managing security control configurations for on-premises, cloud, hybrid and multicloud environments quickly becomes complex, expensive, and burdensome,
And the oldest cyber security challenge is still present in the middle of this cloud transformation journey: How to better secure applications and data without compromising agility?
Cisco Secure Workload 3.6 addresses these critical security challenges by:
- Providing comprehensive workload protection capabilities that bring security closer to applications
- Tailoring the security posture based on the application’s behavior
- Enforcing segmentation and security policies simultaneously on Cisco Secure Firewalls
The design of Secure Workload utilizes rich traffic flow telemetry (agent and agentless data collection), advanced machine learning, and behavior analysis techniques to support the major security use cases in datacenters:
- Behavioral baselining, analysis, and identifying workload anomalies
- Zero-trust model adoption allowing list based micro-segmentation
- Detecting common vulnerabilities and exposures associated with software installation on servers
- Proactively quarantining server(s) when vulnerabilities are detected and blocking communication
- Responding to cyber threats faster – elevating the organization’s security posture
Also, Cisco Secure Workload offers one-click enforcement across multicloud data centers to reduce the attack surface and enforce the security framework using application segmentation. Secure Workload normalizes policies for each server, eliminating human intervention for further policy identification.
From the user experience, Cisco Secure Workload provides an intuitive point-and-click web UI to search information using visual queries and visualize statistics using a variety of charts and tables. In addition, all the administrative functions and cluster monitoring can be done through the same web UI.
New orchestration of Amazon Web Services
The integration with Amazon Web Services (AWS) Virtual Private Cloud (VPC) harmonizes security configurations, coordinating AWS Security Groups North-South, East-West traffic and providing an agentless approach using AWS VPC flow logs for policy discovery and workload’s segmentation.
Equally important, the new coordinated orchestration provides the user with a simpler cloud onboarding workflow that accelerates secure application delivery and drives security infrastructure responsiveness as applications dynamically change. Also, as a part of the new functionality introduced in 3.6, Secure Workload supports automated instance inventory ingestion in a running or stopped state from an AWS region. This functionality makes the creation and maintenance of scopes and policies significantly easier.
Additionally, the integration reduces the burden of manual data sharing during policy implementation, simplifies administration, and mitigates the creation of security silos with disconnected controls that lead to inefficient and ineffective security operations.

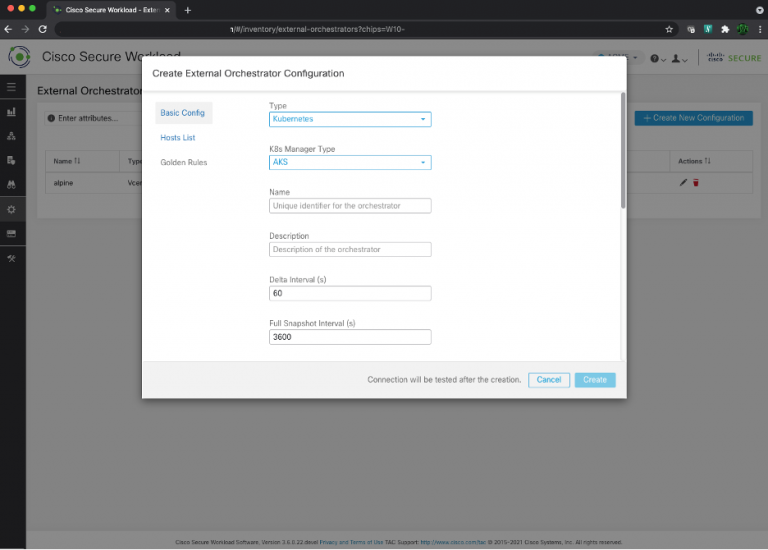
Visibility and policy discovery for Kubernetes workloads
The need for maximizing resource utilization is making Kubernetes the market standard for container management, as it permits scaling flexibility across multiple servers in a cluster, and replication of instances or pods across different nodes.
However, running different applications on the same Kubernetes cluster may create a risk of one compromised workload attacking an adjacent workload. Micro-segmentation ensures that containers can communicate only as designed. One of the top challenges in Kubernetes deployments is creating network segmentation between pods, services, and containers. This is an inherent challenge due to the dynamic nature of container network identities, and the fact that containers can communicate both inside the same node or between nodes.
The integration of Secure Firewall with Secure Workload 3.6’s new Application Dependency Mapping (ADM) mitigates Kubernetes communications security risks. Secure Workload now discovers network policies across applications, both within and external to Kubernetes deployment tiers.
Kubernetes security is improved with Cisco Secure Workload 3.6 by a:
- Simpler process for defining scopes and policies using automated ingestion of the environment inventory
- Better administration and monitoring of Kubernetes environment resources such as nodes, pods, and services
- Possibility to deploy enforcement policies in Kubernetes resources (pods, nodes) leveraging the new automated ingestion
In summary
With Cisco’s hybrid and multicloud security capabilities, you gain unique control, efficiency, and efficacy across your networks, and closer to your applications. In your application infrastructure, you advance application workload micro-segmentation, coupled with common and coordinated policies across AWS’s Security Groups plus physical and virtual Cisco Secure Firewalls.
Additional Resources
Cisco Secure Workload website
https://www.cisco.com/c/en/us/products/security/tetration/index.html
Cisco Secure Workload FAQ
Cisco Secure Workload Data Sheet
The Why, What, and How of Cisco Secure Workload Solution
Configure Secure Firewall and Secure Workload – Unified Segmentation and Policy
https://www.cisco.com/c/en/us/support/docs/security/firepower-management-center/217192-configure-secure-firewall-and-secure-wor.html
Share:

