- 실내 5G 시장, 2030년까지 연평균 22.1%씩 성장··· 생성형 AI도 성장 요인
- The Significance of Cybersecurity within AI Governance
- The Evolution of SOC: Harnessing Data, AI and Automation
- How to disable ACR on your TV (and stop companies from spying on you)
- I expected this cheap multitool to be a waste of money, but it's my new a toolbox essential
CVE-2021-44228: Proof-of-Concept for Critical Apache Log4j Remote Code Execution Vulnerability Available (Log4Shell)

Critical vulnerability in the popular logging library, Log4j 2, impacts a number of services and applications, including Minecraft, Steam and Apple iCloud. Attackers have begun actively scanning for and attempting to exploit the flaw.
Background
On December 9, researchers published proof-of-concept (PoC) exploit code for a critical vulnerability in Apache Log4j 2, a Java logging library used by a number of applications and services including but not limited to:
Dubbed Log4Shell by researchers, the origin of this vulnerability began with reports that several versions of Minecraft, the popular sandbox video game, were affected by this vulnerability.
there’s a minecraft client & server exploit open right now which abuses a vulerability in log4j versions 2.0 – 2.14.1, there are proofs of concept going around already.
— ᵃᵈᵃᵐ (@twokilohertz) December 9, 2021
Additionally, it appears that cloud services such as Steam and Apple iCloud are also affected.
This vulnerability is considered so severe that Cloudflare CEO plans to offer protections for all customers.
Analysis
CVE-2021-44228 is a remote code execution (RCE) vulnerability in Apache Log4j 2. An unauthenticated, remote attacker could exploit this flaw by sending a specially crafted request to a server running a vulnerable version of log4j. The crafted request uses a Java Naming and Directory Interface (JNDI) injection via a variety of services including:
- Lightweight Directory Access Protocol (LDAP)
- Secure LDAP (LDAPS)
- Remote Method Invocation (RMI)
- Domain Name Service (DNS)
If the vulnerable server uses log4j to log requests, the exploit will then request a malicious payload over JNDI through one of the services above from an attacker-controlled server. Successful exploitation could lead to RCE.
In the case of Minecraft, users were able to exploit this vulnerability by sending a specially crafted message through Minecraft chat.
aaaaand then code execution?? #log4j #minecraft pic.twitter.com/aSFzhsm87l
— John Hammond (@_JohnHammond) December 10, 2021
Both GreyNoise and Bad Packets have detected mass scanning activity searching for servers using Log4j.
Mass scanning activity detected from multiple hosts checking for servers using Apache Log4j (Java logging library) vulnerable to remote code execution (https://t.co/GgksMUlf94).
Query our API for “tags=CVE-2021-44228” for source IP addresses and other IOCs. #threatintel
— Bad Packets (@bad_packets) December 10, 2021
There are now reports that this vulnerability is being used to implant cryptocurrency miners.
this log4shell payload is… a coin miner
the vulnerability has arrived pic.twitter.com/XUR7I5ydpP
— Kevin Beaumont (@GossiTheDog) December 10, 2021
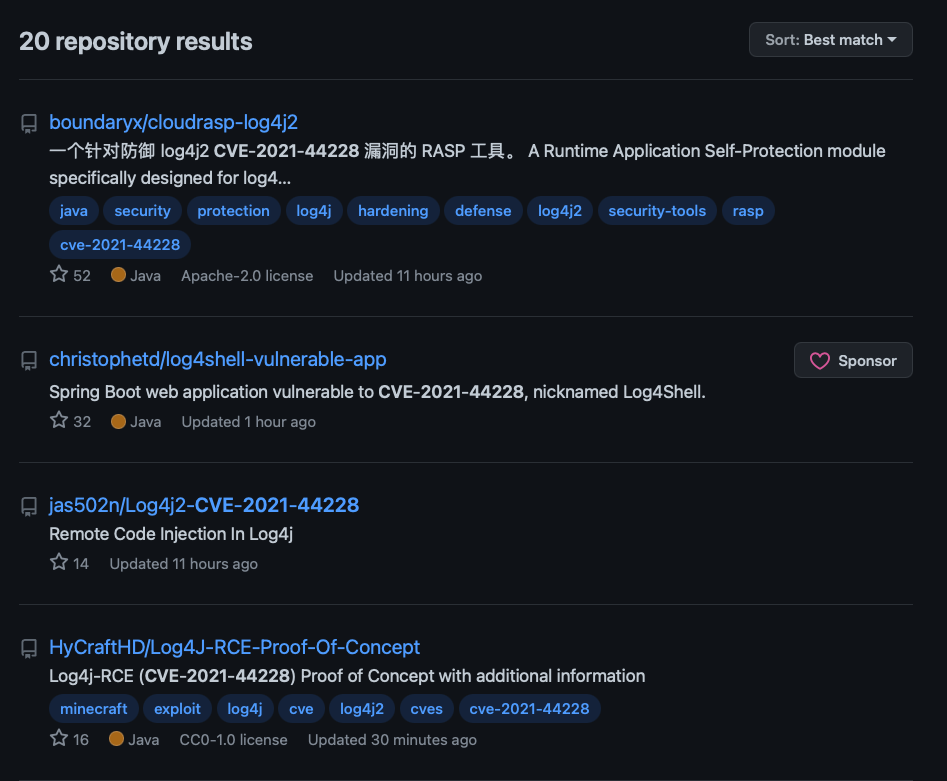
Proof of concept
The first PoC for CVE-2021-44228 was released on December 9 prior to its CVE identifier being assigned. At the time this blog post was published, there were an additional several PoCs available on GitHub.
Solution
While Apache published a release candidate on December 6 to address this vulnerability, it was incomplete. Apache released 2.15.0 on December 10.
Log4j 2.15.0 requires Java 8. Therefore, organizations that use Java 7 will need to upgrade before being able to update to the patched version of Log4j.
Apache advises that if patching is not immediately possible, there are three mitigation routes that can be taken to thwart attempts to exploit this vulnerability:
| Mitigation | Applicable Versions |
|---|---|
| Set log4j.formatMsgNoLookups or Dlog4j.formatMsgNoLookups to true | Log4j 2.10 or greater |
| Use %m{nolookups} in the PatternLayout configuration | Log4j 2.7 or greater |
| Remove JdniLookup and JdniManager classes from log4j-core.jar | All Log4j 2 versions |
Because Log4j is included in a number of web applications and used by a variety of cloud services, the full scope of this vulnerability won’t be known for some time. However, at the time this blog post was published, some products and services that were confirmed to be vulnerable include:
| Product/Service | Confirmed Affected |
|---|---|
| Minecraft | Yes |
| Steam | Yes |
| Apple iCloud | Yes |
| Tencent | Yes |
| Yes | |
| Baidu | Yes |
| Didi | Yes |
| Cloudflare | Yes |
| Amazon | Yes |
| Tesla | Yes |
| ElasticSearch | Yes |
| Ghidra | Yes |
A GitHub repository is being maintained that highlights the attack surface of this vulnerability.
Identifying affected systems
A list of Tenable plugins to identify this vulnerability will appear here as they’re released.
Tenable will be releasing scan templates for Tenable.io, Tenable.sc and Nessus Professional. Once the scan templates are available, we will update this blog post. Organizations that don’t currently have a Tenable product can sign up for a free trial of Nessus Professional to scan for this vulnerability.
Get more information
Join Tenable’s Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.

