- US companies are helping Saudi Arabia to build an AI powerhouse
- US companies are helping Saudi Arabia to build an AI powerhouse
- My favorite Garmin feature comes to its new Forerunner watch
- Trade in your phone to Verizon and get almost any new phone for free - here's how
- Beyond Recognition: Celebrating Cisco's Women Channel Leaders in 2025
Aviation Attacks Tied To Single APT – TA2541

Fraud Management & Cybercrime
,
Next-Generation Technologies & Secure Development
,
Threat Intelligence
Group Uses Variety of RATs to Target Its Victims But Its TTPs Remain Constant
Cyberattacks in the aviation sector over the past several years have been tied to a single advanced persistent threat group named TA2541, which – since at least 2017 – has used more than a dozen remote access Trojans to control compromised machines, according to a report from cybersecurity firm Proofpoint.
See Also: Live Discussion | Level Up Your Data Security Posture to Accelerate Ransomware Recoveries
Since at least 2017, the APT has consistently used more than a dozen remote access Trojans to control and carry out malicious activities, such as cyberespionage, the researchers say.
Multiple researchers – including Cisco Talos, Morphisec, Microsoft, Mandiant and several other independent researchers – have observed the activities of this threat actor since 2019. Proofpoint’s researchers confirm that all these activities are linked to the same APT, which it has named TA2541 for ease of tracking.
Other sectors on the APT group’s radar include transportation, aerospace, manufacturing and defense industries, the researchers say.
The Campaign
The main modus operandi of TA2541 is to send bulk emails – nearly tens of thousands in a single instance – to potential victims in North America, Europe and the Middle East. These regions have been recurring targets for this APT and have been lured using themes that include keywords such as flight, aircraft, fuel, yacht, charter, etc., rather than the latest or trending topics, the researchers say.
With the onset of the COVID-19 pandemic, the APT group temporarily used COVID-19-related lures, the researchers say, but it returned to its original email themes after a few days.
The Attack Chain
TA2541 leverages several RATs for targeting victims. Its tactics, techniques and procedures have remained consistent over the years, barring the initial days in 2017 when the group sent malicious Microsoft Word attachments with macros that downloaded the RAT payload, the researchers say.
Since then, they say, the APT group has been sending messages with links to cloud services, such as Google Drive and One Drive, where the payload is hosted in a VBS file. The researchers say that the group has a set attack chain that needs to be studied to avoid future compromises.
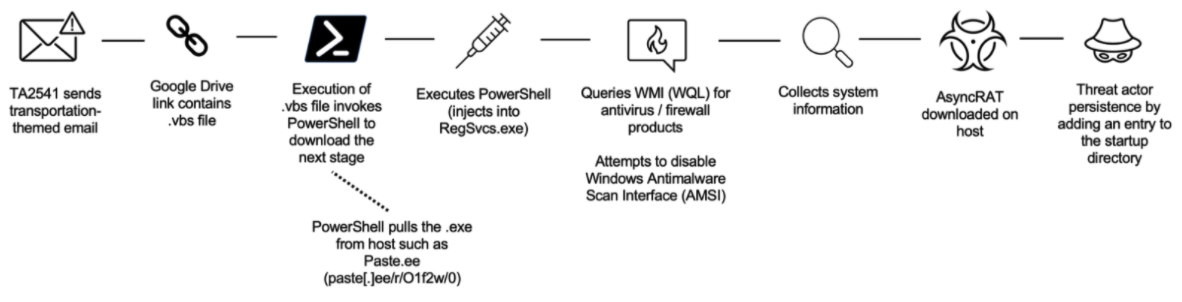
The group then conducts reconnaissance by executing several PowerShells that are loaded into the VBS file in various Windows processes. These PowerShells also query the Windows Management Instrumentation and collect information on the security products, such as antivirus and firewall software-implemented in the targeted system, and it attempts to disable these built-in security protections.
Once this has been completed, in the last stage of the attack chain, the group uses AsyncRAT payload which, when executed, establishes persistence with the compromised system.
But this not the only RAT that the group deploys as a payload. It has at least a dozen more, the researchers say. “The threat actor uses commodity malware available for purchase on criminal forums or available in open-source repositories. Currently, TA2541 prefers AsyncRAT, but other popular RATs include NetWire, WSH RAT and Parallax,” according to the researchers.
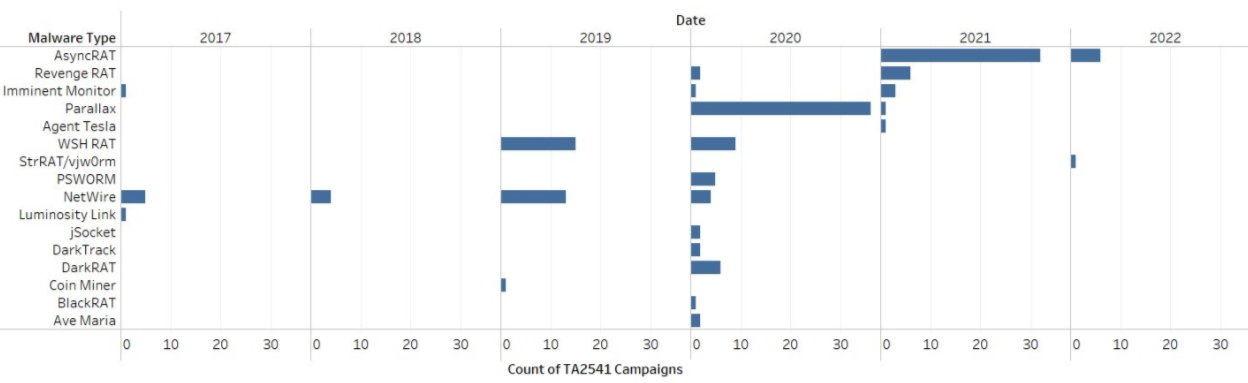
Since late 2021, Proofpoint researchers have observed the group using DiscordApp URLs that link to a compressed file that loads either AgentTesla or Imminent Monitor payload.
The C2 Infrastructure
TA2541 uses virtual private servers to deliver bulk emails and frequently uses dynamic domain name service – or DDNS – for command-and-control infrastructure, the researchers say.
The C2 infrastructure and the message artifacts are closely linked to each other and have several common patterns, the researchers say. “For example, historic campaigns have included the term ‘kimjoy’ in the C2 domain name as well as in the threat actor reply-to address.”
Other common patterns observed with TA2541’s C2 domains and payload staging URLs are that they contain the keywords ‘kimjoy,’ ‘h0pe,’ and ‘grace.’ The group is also known to regularly use the same domain registrars – Netdorm and No-IP DDNS – and hosting providers – xTom GmbH and Danilenko, Artyom, the researchers say.
Researchers have also included other indicators of compromise, such as C2 domains, VBA SHA256 hashes and ET signatures in their report, so that SOCs can integrate those in their daily scanning.
The researchers say they are confident that TA2541 will continue its modus operandi using the same TTPs with minimal changes to its lure themes, delivery and installation methods. They warn that the APT group will continue using AsyncRAT and vjw0rm in future campaigns, as well as other commodity malwares, to attain its objectives.
Tim Erlin, vice president, of strategy at Tripwire tells ISMG that commercial threat actors such as TA2541 often develop expertise in selling to a specific industry because it’s more effective for their business. Cybercriminals are also running a business, albeit an illegal one, he says, so we should expect similar techniques to be used.
“By focusing on specific industries, these attackers can craft more effective attacks. That expertise is especially useful for spear-phishing and social engineering campaigns, where the ability to deliver a convincing message is key to success. We need to take these TTPs into consideration and arm up against these operations that have malicious intent,” Erlin says.
State-sponsored actors are also targeting the aviation sector. In a recent campaign, an Iranian state-sponsored threat group was found abusing free workspaces on the Slack messaging platform to deploy a backdoor in an Asian airline’s system (see: Iranian Threat Actor Uses Slack API to Target Asian Airline).
The backdoor was used to send system information, files and screenshots of the data on the victim systems to its C2 server, according to the commands received. Slack shut down those workspaces when it discovered the abuse, it told Information Security Media Group at the time.

