Visualize and validate policy, increase remote worker telemetry, and embrace zero trust with Network Analytics Release 7.3.1

We have heard it before. Securing your organization isn’t getting any easier. The remote workforce is expanding the attack surface. We need context from users and endpoints to control proper access, and IT teams need to ensure our data stores are resilient and always available to gain the telemetry they need to reduce risk. Yes, zero trust is a great approach, but network segmentation in the workplace is hard, and it can shut down critical business functions if not deployed correctly.
To answer these challenges, we are excited to announce new features in Cisco Secure Network Analytics (formerly Stealthwatch). In 7.3.1, we are introducing TrustSec-based visualizations that allow network operations and security teams to instantly validate the intent of policies. This is a big jump that provides organizations the visibility required to confidently embrace network segmentation, a critical component of the zero-trust workplace.
To answer the remote work challenge, the Cisco Secure Network Analytics team has simplified how customers obtain user and endpoint context from AnyConnect. And to ensure the expanded attack surface doesn’t increase risk, Secure Network Analytics has advanced its integration with Cisco Talos, one of the largest threat intelligence teams in the world. But there is more; read on to learn how we virtualized the Data Store to simplify how organizations big and small ensure resiliency and manage the growing volumes of data required to stay a step ahead in the arms race that is network security.
TrustSec Analytics reports offer new ways to visualize group communications between SGTs
Secure Network Analytics’ TrustSec Analytics reporting capability leverages the Report Builder application and its integration with Cisco Identity Services Engine (ISE) to automatically generate reports that map communications between Security Group Tags (SGTs) to provide users with unprecedented visibility into all communications across different groups within their environment. For security teams that want to adopt a group-based policy management program to build network segmentation but lack the resources to pursue one, TrustSec Analytics reporting lowers the entry point to doing so. Now any Secure Network Analytics user can effortlessly visualize, analyze, drill down into any inter-group communication, adopt the right policies, and adapt them to their environment’s needs.
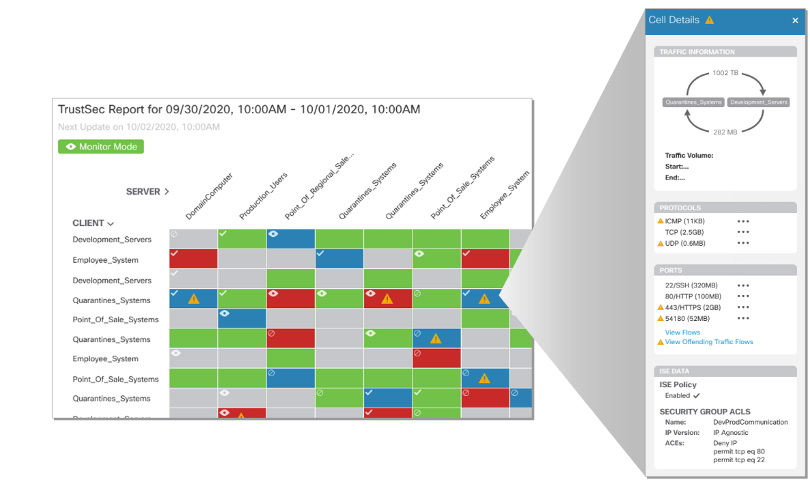
Streamline policy violation investigations with TrustSec Policy Analytics reports
TrustSec Policy Analytics reports can also be generated to assess whether policies are being violated. By clicking on any cell in the report, users can gain insights into the volume of data being sent between any two groups, how that data is being distributed, the protocols being used, what ports they are operating on, and more.
Additionally, when it comes to the typically lengthy processes associated with determining a policy violation’s root cause, the capabilities offered by the TrustSec Policy Analytics report quite literally enable users to find the proverbial ‘offending-flow needles’ in their vast ‘network haystacks’. Rather than performing hours of cumbersome tasks such as conducting manual searches and cross-references across different datasets, users can get granular by drilling down into policy violations to view all associated IPs and related flows, associated endpoints, ISE-registered usernames, and events with timestamps on single pane. This effectively enables users to streamline their root cause analysis efforts and expedite their ability to diagnose why a policy violation occurred.
Increased Remote Worker Telemetry
Amidst the recent explosion of people working from home, organizations face new challenges related to monitoring and securing their remote workforces as they connect back to the network from anywhere and on anything.
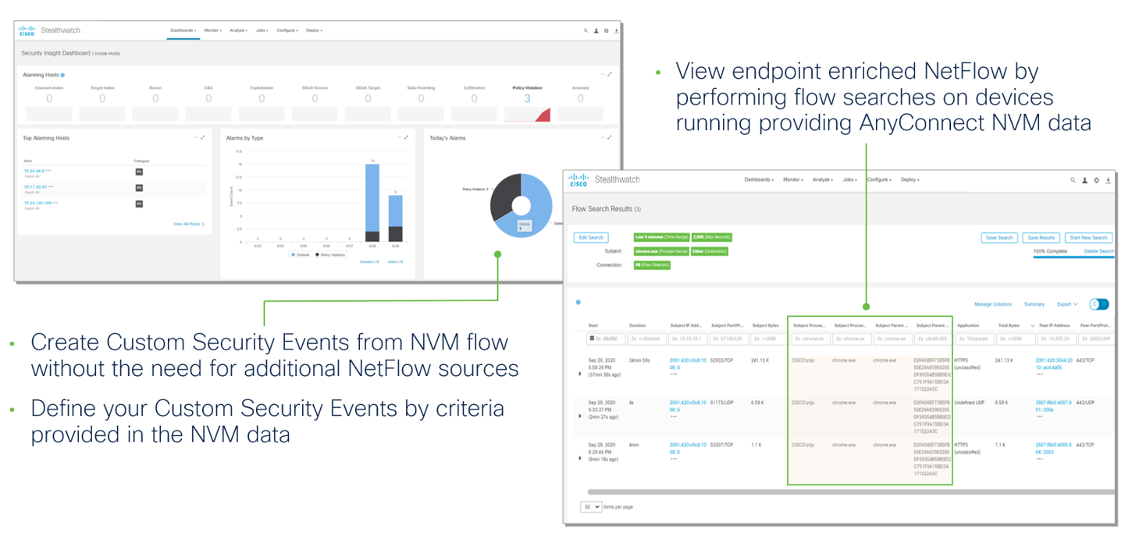
Secure Network Analytics has made endpoint Network Visibility Module (NVM) data the primary telemetry source to meet these challenges, effectively eliminating the need for NetFlow to gain user and device context. Customers are gaining the following benefits:
- Simplified remote worker monitoring with endpoint NVM data becoming a primary telemetry source
- More efficient remote worker telemetry monitoring by collecting and storing on-network NVM endpoint records without the need for NetFlow
- Increased Endpoint Concentrator ingestion bandwidth to support up to 60K FPS
- NVM driven custom alerting and endpoint flow context
Introducing the Secure Network Analytics Virtual Data Store!
The Secure Network Analytics Data Store is now supported as a virtual appliance offering. Similar to the Data Store that was introduced in 7.3.0, the virtual Data Store offers a new and improved database architecture design for Secure Network Analytics that enables new ways of storing and interacting with data more efficiently. A virtual Data Store supports a 3-node database cluster with flow ingest from virtual Flow Collectors. This new architecture decouples ingest from data storage to offer the following benefits:
- Query and reporting response times improved by a significant (10x faster!) magnitude
- Scalable and long-term telemetry storage capabilities with no need for additional Flow Collectors
- Enterprise-class data resiliency to allow for seamless data availability during virtual machine failures
- Increased data ingest capacity of up to 220K flows per second (FPS)
- Flexible deployment options – as a fully virtualized appliance, the Virtual Data Store does not require additional rack space and can be rapidly deployed using your existing infrastructure
Enhanced security analytics
As threats continue to evolve, so do the analytical capabilities of Secure Network Analytics to deliver fast and high-fidelity threat detections. The cloud-based machine learning engine has been updated to include:
- System alarms have been ported to appear as notifications in the Web UI
- Brand new confirmed threat detections related to ransomware, remote access trojans (RAT) and malware distribution

To learn more about this release, check out the Release 7.3.1 Release Notes.
Don’t have Secure Network Analytics? Learn more by visiting https://www.cisco.com/go/secure-network-analytics or try the solution out for yourself today with a free visibility assessment.
Share:

