- Better Together: How MFA and Strong Password Practices Can Help Bolster Security
- “美 CISO 평균 연봉 6억,상위 1%는 60억원 넘어···보안 예산은 여전히 부족” IANS 설문조사
- 아웃시스템즈, 매출 5억 유로 돌파 및 신임 CEO 선임 발표
- 정철환 칼럼 | 변화의 바람에 맞설 것인가? 따를 것인가?
- Best home automation systems 2025: I'm a smart home reviewer and these are the top ones
Comply to Connect: The Bridge to Zero Trust

Guest Author:
Chris Crider
Security Systems Engineering Leader for Cisco US Public Sector
When it comes to Zero Trust frameworks and principles, few organizations are as comprehensive as the US Department of Defense (DoD). In 2022, the DoD released their seven-pillar strategy to articulate their critical cyber capabilities and activities associated with Zero Trust principles (Figure 1), while also aligning the functional rollout of those capabilities with a targeted timeline of execution of the basics through 2027.
Figure 1: DoD seven pillars of Zero Trust

What is Comply to Connect?
One of the capabilities in the Devices pillar of the DoD Zero Trust Strategy is Comply to Connect (C2C), an NDAA mandate and a Defense Information Systems Agency (DISA) program setup to monitor and manage government endpoints and their health, plus to affect their authorization into the environment based on an ongoing set of endpoint criteria. The scope of the C2C program is a tremendous undertaking by itself. However, the program’s extent does not account for user and device attribution to sessions or behavior within each session, which can also be made through a common set of tools in the journey to Zero Trust maturity.
The Comply to Connect program is a bridge to Zero Trust access. So, device authentication and authorization need to account for not only user devices but also non-user devices. This is especially true since the vast worlds of the Internet of Things (IoT) and Industrial Internet of Things (IIoT) have entered the spotlight due to cyber-attacks and a lack of emphasis on non-user devices like SCADA systems, traffic sensors, and security cameras.
Comply to Connect and device behavior
Since the IoT and IIoT have now become key gateways for intrusion, device health and least-privilege authorization must now be complemented with an understanding of device behavior and activity. For example:
- Can an organization identify a device (like a camera)?
- Does a device exhibit unusual activity for its role (like trying to connect to an adversarial network)?
- Or even more simply, from an operational perspective, is an authorized endpoint on one network attempting to connect to a different network classification?
Applying Zero Trust principles like these to government networks helps agencies properly identify and authorize (or deny) any user and device trying to access their network. Just as importantly, it enables your agency to continuously monitor and attribute the behavior of an entity on your network. This lets you quickly and accurately take appropriate actions to stay secure.
Cisco’s security portfolio helps government organizations increase their Zero Trust maturity by facilitating secure communications from endpoint to application. This includes authenticating and authorizing a user and device per session. Plus, our comprehensive security portfolio also evaluates endpoint health, facilitates remediation, and attributes all data accessed and exchanged throughout the session with the originating entity.
Comply to Connect and Cisco ISE
For most government organizations, complexity often surfaces from deploying a large patchwork of tools to mitigate various threats. The result is a security environment with too many tools and not enough experts on staff. This means your missions and programs face an uphill battle to effectively combat threats from numerous attack vectors simultaneously.
That’s where Cisco Identity Services Engine (ISE) can add tremendous value for government networks. Cisco ISE is our Zero Trust policy engine and policy decision point (PDP). It’s a foundational component of Zero Trust and an exceptionally versatile component of a comprehensive strategy when paired with other tools, making contextual access decisions and enforcing policy continuously throughout each session.
Cisco ISE integrates with leading third-party identity platforms, endpoint solutions, and other various data sources to provide contextual and risk-based access to operational environments for both users and devices. It can also make decisions whether the session originates over traditional wired and wireless networks, P5G, VPN, or ZTNA use cases.
In a world where most organizations are understaffed, it’s critical that programs simplify their toolset to create maximum effectiveness. Automation and orchestration can also create their own operational challenges if there are too many moving parts among vendors. That’s why we’ve also equipped Cisco ISE is with rich APIs to help automate dynamic policy and facilitate simplified policy enforcement across security solutions and network environments.
An integrated toolset for Comply to Connect
When not using phishing mechanisms, today’s attackers rely on misconfigurations and user error for entry points. To achieve the desired outcomes and the promises of Zero Trust principles, the government must work to streamline their toolsets to ones that integrate effectively. This will help them achieve visibility and enforcement consistently end-to-end. Security architectures must also be able to assert both least-privilege access at the onset of the connection and risk-based updates to the session in the event of abnormal activity.
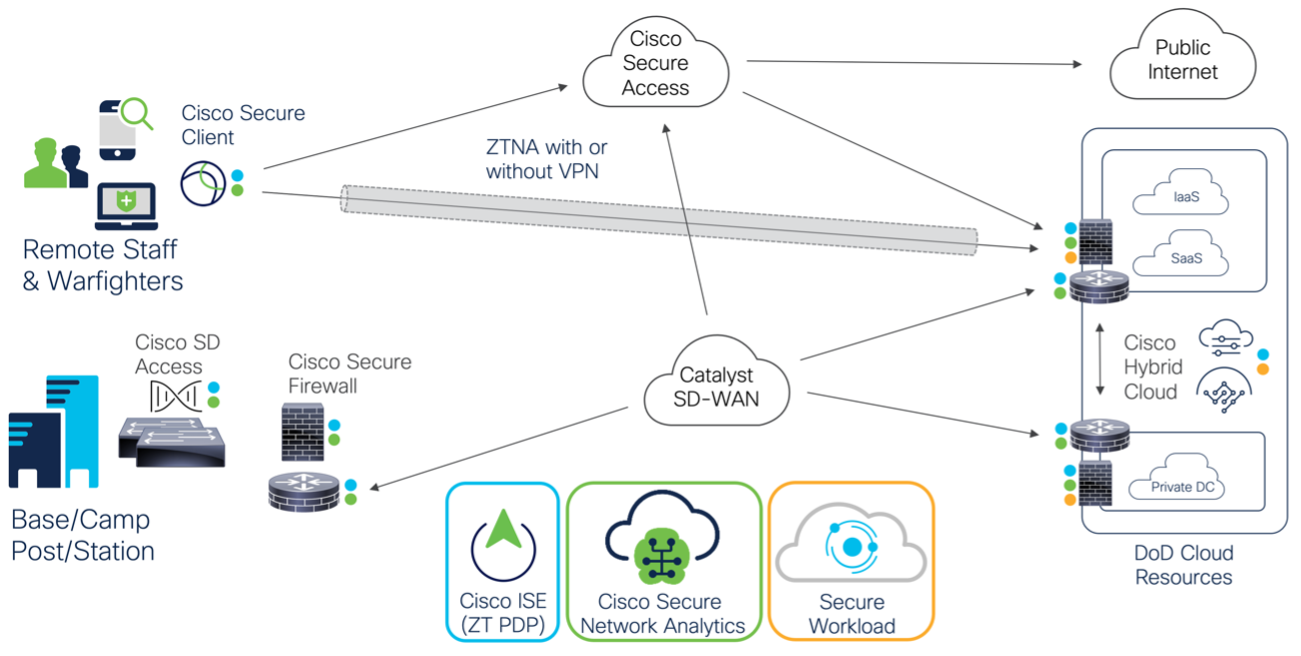
That’s the great thing about the Cisco Security portfolio. As a critical part of an integrated toolset, it creates a system to identify users and assets before it authorizes them for access into your network environment. The same capabilities can also monitor user and device behavior for abnormalities as they access data (in conjunction with other tools), across any connection medium, and ultimately update controls if risk-based updates must be applied to the session (Figure 2). This includes:
- Cisco Identity Services Engine (ISE), Secure Firewall, Secure Network Analytics, and Secure Client combining to provide visibility and enforcement for any connection attempt. This creates a unified and secure platform, especially when paired with Cisco’s industry-leading network and threat intelligence capabilities.
- Cisco ISE acting as a Zero Trust policy decision point (PDP) and integration point via APIs, to incorporate third-party capabilities in a multi-vendor Zero Trust ecosystem.
- Cisco Secure Access integrating with our Secure Client to provide end-to-end encryption or protect endpoints from the cloud when they are not connected to the enterprise.
Figure 2: Cisco Security portfolio architecture
Getting the right tools for C2C
As always, it’s important to select the right tool for the job. This is especially true when it comes to cybersecurity. Deploying the proper mission-aligned tools helps your organization achieve the desired return on investment (ROI) while increasing your security operation center (SOC) efficiency. This is a great benefit of adopting Zero Trust principles.
The capabilities of Cisco’s security portfolio (through our technical alliance partners) also integrate with several leading industry vendors who provide deep endpoint inspection, identity lifecycle, hybrid workload and container environments, event correlation, and more. This provides your agency with maximum effectiveness.
Remember, when it comes to Zero Trust it’s important to look at where to begin each organization’s journey to maturity. For the DoD, building on a long-standing history of RMF, Defense in depth, and NIST 800-53, Zero Trust maturity can help facilitate collaboration between siloed organizations. The good news is that the Comply to Connect program can be used as a starting catalyst, with the basics of inventory and endpoint health creating an opportunity to enforce policy and attribute behavior to users and devices consistently.
Moving forward, using tools that effectively perform these functions for the scope of Comply to Connect, and inform other programs, is key to turning the tide against the growing pressures of defensive cyber operations (DCO). Cisco’s Security portfolio, in conjunction with a consolidated set of vendors, can help the government do so and streamline your efforts toward a more secure operational environment.
More resources
Share: