- I recommend the Pixel 9 to most people looking to upgrade - especially while it's $250 off
- Google's viral research assistant just got its own app - here's how it can help you
- Sony will give you a free 55-inch 4K TV right now - but this is the last day to qualify
- I've used virtually every Linux distro, but this one has a fresh perspective
- The 7 gadgets I never travel without (and why they make such a big difference)
Massive EvilProxy Phishing Attack Campaign Bypasses 2FA, Targets Top-Level Executives

This attack sent approximately 120,000 phishing emails to organizations worldwide with the goal to steal Microsoft 365 credentials.
New research from Proofpoint exposes a new massive credential phishing attack campaign aimed at top-level executives in more than 100 organizations worldwide. This cybersecurity attack leverages the EvilProxy phishing kit and bypasses two-factor authentication.
We break down the specifics of EvilProxy, including which accounts have been targeted, and provide tips on protecting your business from this threat.
Jump to:
What is EvilProxy?
EvilProxy is a phishing-as-a-service kit that was first exposed by cybersecurity company Resecurity in September 2022. This kit has the ability to run phishing attacks with reverse proxy capabilities that enable it to steal credentials and bypass 2FA by deploying adversary-in-the-middle techniques (Figure A).
Figure A
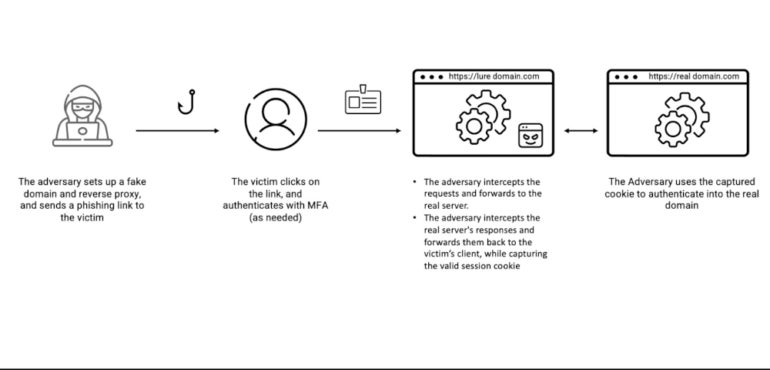
Any cybercriminal can acquire EvilProxy and start using it via a simple interface that allows the creation of phishing campaigns with customizable options. The service sets up a phishing website according to the selected options and is then ready to go. When an unsuspecting user visits the phishing page, they provide their credentials. The phishing page then asks for the 2FA code for authentication to the service. Once provided, the code is immediately used by the kit to get access to the user’s account by opening a session.
Daniel Blackford, threat researcher at Proofpoint, told TechRepublic that EvilProxy is sold in underground forums and Telegram channels, and added that “The basic version of EvilProxy costs a few hundred dollars, but it depends on many parameters like: feature set, number of targeted users, etc.”
EvilProxy attack chain
The attack campaign starts with emails pretending to come from known and trusted services or brands such as DocuSign, Adobe or Concur. The emails contain a malicious link leading the user to an open redirection at a legitimate website such as YouTube or Slickdeals (Figure B) in an attempt to avoid detections at the email level.
Figure B

A series of redirecting websites (Figure C) follow in an unpredictable way, aiming to lower the chances of discovery. The user lands on the EvilProxy phishing website, which in this campaign is a Microsoft login page functioning as a reverse proxy.
Figure C
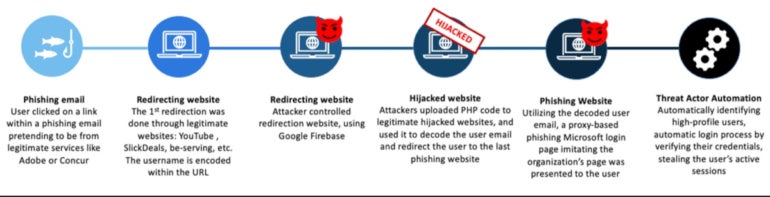
To hide the email address of the victim while doing the redirections and avoid automatic scanning tools detections, the attackers use a special encoding and only use compromised legitimate websites to upload their PHP code to decode the email address before landing on the EvilProxy phishing page.
Thousands of high-value Microsoft cloud accounts targeted
This attack campaign sent approximately 120,000 phishing emails to hundreds of targeted organizations worldwide between March and June 2023, with the goal to steal users’ Microsoft 365 cloud credentials.
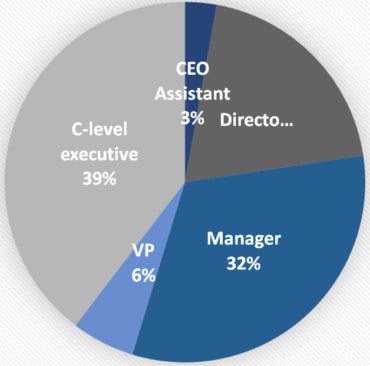
According to Proofpoint, the list of targeted users includes many high-value targets such as vice presidents and C-level executives from leading companies. The attackers ignored employees in lower positions. As stated by the researchers, it seems reasonable to think the threat actor used organizational information acquired from public sources to sort out who would be interesting.
Statistics amongst hundreds of compromised users reveal that 39% were C-level executives, of which 17% were chief financial officers and 9% were presidents and chief executive officers. Managers were 32% of the compromised users (Figure D).
Figure D
Oddly, users with a Turkish IP address were redirected to the legitimate web page, which suggests the threat actor might come from that country or is actively ignoring any Turkish user account. Numerous virtual private network IP addresses were also redirected to the legitimate website instead of the EvilProxy page.
While the goal of this attack campaign remains unknown, this kind of attack generally leads to financial fraud or sensitive data exfiltration. The threat actor might also sell access to these high-value mailboxes to other cybercriminals.
Maintaining fraudulent access to the mailboxes
Once an active session is established on a compromised account, the threat actor adds its own multifactor authentication method in the Microsoft 365 parameters, adding Authenticator App to it (Figure E).
Figure E
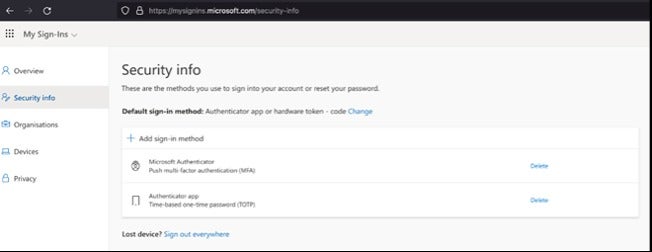
Afterward, the threat actor no longer needs EvilProxy’s reverse proxy feature to log in to the compromised account and simply logs in with the credentials and a code provided on their own Authenticator application.
How to protect from this security threat
Here are four tips for protecting against the EvilProxy threat.
- Use email security solutions to block malicious emails sent to employees.
- Train employees to detect such phishing attacks.
- Deploy network security solutions to try to detect phishing, malware or other threats.
- Run phishing attack simulations to help IT raise awareness amongst employees.
It’s also advised to use FIDO2-based physical keys when possible because that kind of hardware securely stores a private key that isn’t normally accessible to the attacker, even if the person is intercepting all communications between the user’s device and the online service.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.

