- This handy USB meter tells you what's actually going on with your ports - and it's only $20
- This budget Lenovo ThinkPad has no business being this good - especially for hybrid workers
- Déjà Vu: What Cloud Adoption Can Teach Us About AI in Cybersecurity
- Motorola to outfit first responders with new AI-enabled body cameras
- CIOs highlight negotiation opportunities as AWS and Google lower cloud costs
Best SIEM Tools and Software for 2023

Looking for the best SIEM tool? Check out our list and find the security information and event management solution that fits your business needs.
Security information and event management (SIEM) is a device and environmental analysis strategy intended to help secure and protect company operations, data and personnel. By providing a comprehensive analysis of security-related details and related recommendations, SIEM tools assist through ensuring compliance and remediating potential or active threats.
According to Grand View Research, the global SIEM market amounted to almost $4 billion in 2022. It is expected to continue to expand at a rate of 14.5% per year through 2030 due to growing instances of cyberattacks and breaches.
SEE: Whitepaper: Security Information and Event Management (SIEM) Orchestration | TechRepublic (TechRepublic)
Top SIEM software comparison
Those wishing to adopt SIEM or planning to upgrade a legacy SIEM tool to a modern platform should carefully evaluate the available tools. Features such as cloud and on-prem functionality, remediation capabilities and the platforms supported should be among the top areas to be considered.
| Cloud | Hosted on-prem | Remediation | Platforms | Pricing | |
|---|---|---|---|---|---|
| Y | Y | Includes some automated remediation features. | Windows, Linux and Mac. | Starts at $2,877. | |
| Y | N | Full range of remediation capabilities. | Windows, Linux, Mac and Chrome. | Starts at $925 per year. | |
| Y | N | Some remediation capabilities. | Windows, Linux and Mac. | Starts at $173 a month. | |
| Y | N | Limited remediation capabilities. | Windows, Linux and Mac. | Starts at $15 per host per month. | |
| Y | Y | Limited remediation capabilities. | Windows, Linux and Mac. | Begins at $28,000. | |
| Y | Y | Limited remediation capabilities. | Windows, Linux and Mac. | Starts at $857 per node per month. | |
| Y | Y | Limited remediation capabilities | Windows, Linux and Mac. | Starts at $595. | |
| Y | Y | Full remediation capabilities. | Windows, Linux and Mac. | Starts at $2,340 per node. | |
| Y | Y | Remediation capabilities only available with purchase of additional Trellix modules. | Windows, Linux and Mac. | $61,294.33 per VM | |
| Y | N | Remediation included | Windows, Linux and Mac. | Starts at $1,075 per month |
Jump to:
SEE: Integrating SIEM into Your Threat Hunting Strategy | TechRepublic (TechRepublic)
SolarWinds : Best for log aggregation
Figure A

SolarWinds Security Event Manager (SEM) is focused on log aggregation and threat detection. It can easily process and forward raw event log data to external applications for further analysis using syslog protocols, which is an area where it stands out from the competition.
Pricing
- SolarWinds annual SEM subscriptions start at $2,877.
- Perpetual licensing is available for around $5,000.
Features
- Automation to remediate some incidents.
- Export log data and share with other teams or vendors.
- Dashboards indicate the state of security, and reports address compliance requirements.
- Pre-built connectors pull data from numerous sources.
- A file integrity checker tracks access and changes made to files and folders to detect unauthorized or malicious activity.
Pros
- Good for network-related events and analyzing per-host activities, such as logons, privilege usage and registry alterations.
- Security features include data encryption, single sign-on and smart card authorization.
- Ability to restrict access from IPs, block applications and deny access to removable media.
Cons
- Dashboards can become cluttered and hard to understand when processing large amounts of data.
- Can struggle with the complexity of very large enterprise environments.
- Automated does not provide a full range of remediation capabilities.
Splunk Enterprise Security: Best for cloud native environments
Figure B
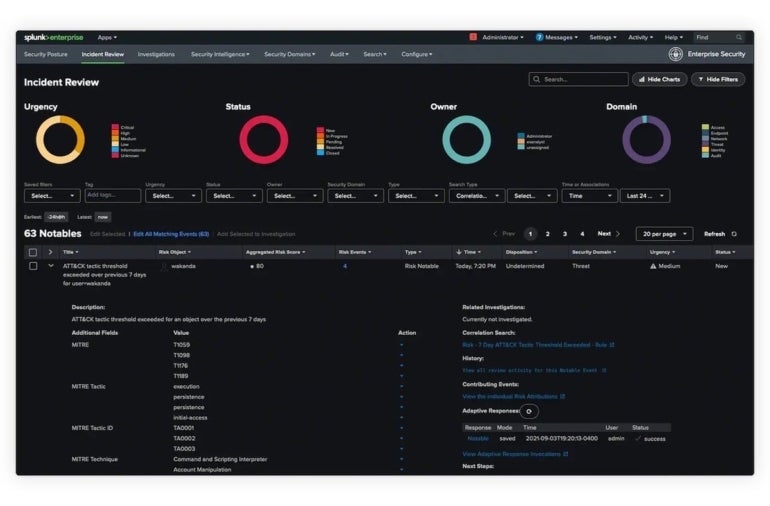

Splunk Enterprise Security offers cloud-based security-related event notifications and log monitoring. It can identify resource bottlenecks, failing hardware, capacity issues and other potential issues. As it evolved in the era of the cloud, it is particularly well suited to cloud-native environments. Splunk Incident Review dashboard Image: Splunk
Pricing
- Splunk’s complex pricing structure is split into entity, activity, workload and ingest categories.
- Splunk does not publish exact prices, but user reports place them anywhere from $173 per month up to $1,800 per GB.
Features
- Threat detection with machine learning, including 1,400 detections for frameworks such as MITRE and others.
- Ingest and monitor tens of terabytes of data per day from any source, structured or unstructured.
- Attribute risk to users and systems, map alerts to cybersecurity frameworks and trigger alerts when risk exceeds thresholds.
- Investigate security events or suspicious activity rapidly.
Pros
- Triggers that respond to logged situations with customized response patterns.
- Analytics capabilities are built in, which can produce long-term graphs.
- View a wide range of logs and drill down into specific times or data sources.
- Ability to solve problems across multiple platforms.
Cons
- Some users consider Splunk to be expensive when monitoring large amounts of data in major enterprise environments.
- The company’s recently announced acquisition by Cisco may lead to long integration delays and lack of progress on its innovation roadmap.
Datadog Security Monitoring: Best for customization
Figure C
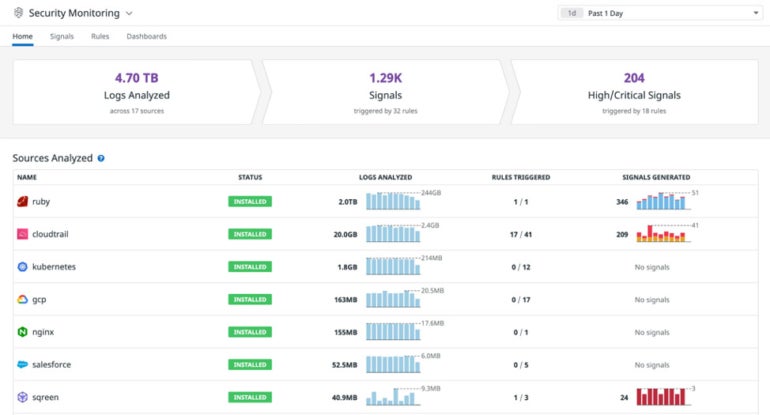

Datadog has designed its platform to be highly customizable to user needs. Datadog Security Monitoring makes it relatively easy to see at a glance what’s happening with all sources being analyzed.
Pricing
- The pro version costs $15 per host per month, and the enterprise version is $23 per host per month.
Features
- Over 350 detection rules and more than 500 integrations with log sources provide full visibility into security operations.
- Ability to see inside any stack or application at any scale and anywhere.
- Infrastructure monitoring, APM, log management, device monitoring, cloud workload monitoring, server monitoring and database monitoring, all included.
- Assemble data from logs and other metrics to provide context and minimize incident response time.
Pros
- Datadog takes a monitoring approach geared toward analytics and is favored by DevOps and IT to address cloud and infrastructure performance.
- Datadog installation is straightforward, courtesy of agent deployment.
- Dashboards and interfaces are easy to customize.
Cons
- Datadog stops short of calling itself a complete SIEM platform, as it is more focused on cloud monitoring and security but has been expanding its cloud SIEM capabilities.
- Datadog lacks some of the log monitoring capabilities of full-featured SIEM platforms.
LogRhythm SIEM: Best for on-premises.
Figure D

LogRhythm’s SIEM software is designed to be hosted on-premises. It has built AI and automation features into its platform. Reporting based on queries is easy to configure. The system integrates well with an array of security and technological solutions..
Pricing
- Begins at $28,000.
- A variety of pricing options are available, such as perpetual or subscription software licenses, an unlimited data plan and a high-performance plan.
Features
- Heightens the detection of security and potential threats.
- LogRhythm provides an integrated user experience.
- Combines enterprise log management, security analytics, user entity and behavioral analytics (UEBA), network traffic and behavioral analytics (NTBA) and security automation and orchestration.
- As well as an on-prem version, it also offers a cloud-based SIEM.
Pros
- Built on a machine analytics/data lake technology foundation that’s designed to scale easily.
- Open platform allows for integration with enterprise security and IT infrastructure.
- Embedded modules, dashboards and rules deliver threat monitoring, threat hunting, threat investigation and incident response.
- Integration with many third-party platforms.
- User comments are favorable about the speed and responsiveness of the support team.
Cons
- Large upfront investment often needed for the on-prem version.
RSA NetWitness: Best for large enterprises
Figure E
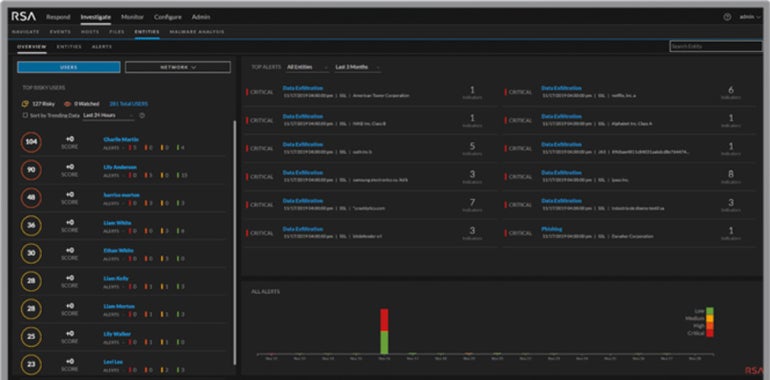

RSA, well known for its multifactor soft and hard token authentication products, has a strong footprint in the overall security community. Its NetWitness SIEM is geared more toward large businesses, with versions that work both on-premises and via cloud.
Pricing
- Pricing starts at $857 per node per month.
Features
- NetWitness monitors for actionable events.
- Behavior analytics observe hacker activity and recreate full sessions to observe the precise anatomy of an attack.
- Intelligence feeds based on customizable information track and remain key operations.
- Visibility into log data spread across the IT environment
Pros
- Simplifies threat detection, reduces dwell time and supports compliance.
- Centralized log management and log monitoring for logs generated by public clouds and SaaS applications.
- Identification of suspicious activity that evades signature-based security tools.
Cons
- The learning curve and implementation efforts can be steep.
- Some users require a large amount of rack space.
ManageEngine Log360: Best for small businesses

ManageEngine Log360 is a SIEM that serves businesses of all sizes but is especially suited to small business deployments. It also integrates well with a series of other security and monitoring products that the company offers.
Pricing
Features
- Detect internal threats, such as data exfiltration and user account compromise, by recognizing subtle changes in user activity.
- Identify suspicious or blocklisted IPs, URLs and domains intruding into your network by correlating your log data with reputed threat feeds.
- Automate responses to events with configurable workflows.
- Monitor active VPN connections and receive alerts on unusual VPN activities and VPN access from malicious sources.
Pro
- Migrate SharePoint environments to Microsoft 365 by selecting the required SharePoint site users, groups and permission levels.
- Audit changes in Active Directory infrastructure and Azure AD in real time.
- Discover and classify sensitive files, audit users’ file activities and analyze file permissions.
- Detect, disrupt and prevent sensitive data leaks via endpoints, like USBs and printers, email and web applications with real-time security monitoring.
Cons
- Some users complain of poor support.
- May struggle to scale well enough in large, complex environments.
IBM Security QRadar SIEM: Best for IBM shops
Figure F
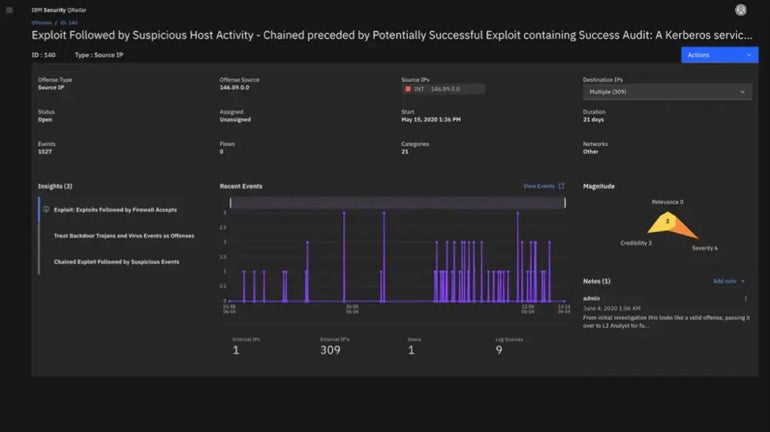

IBM QRadar is a threat detection and response solution that includes an SIEM module. As such, IBM Security QRadar SIEM is especially suited to enterprises that are heavily invested in IBM tools and systems, as well as large enterprise deployments.
Pricing
- Per node monthly cost starts at $2,340.
Features
- Accelerated threat response by dashboards that highlight alerts that matter.
- Uses near real-time analytics to intelligently investigate and prioritize high-fidelity alerts based on severity of risk.
- Identifies insider threats and risky user behavior.
- Part of IBM Cloud Pak for Security which uses AI to provide risk assessments as well as analytics.
Pros
- Machine learning-based analytics to identify anomalies as potential threat actors.
- QRadar SIEM augments traditional log data by monitoring key network flow data.
Cons
- Lack of integration with other SIEM tools.
- Those not using IBM platforms may find it difficult to deploy.
Trellix Security Operations and Analytics: Best for Windows shops

Trellix Security Operations and Analytics contains the bones of the old McAfee Enterprise Security Manager SIEM platform and is now a module known as Trellix Enterprise Security Manager. That SIEM offering was Active Directory-based and well suited to Windows environments. But Trellix has expanded it to offer strong cloud support.
Pricing
- Trellix Virtual ESM is priced at $61,294.33 per VM.
Features
- The Trellix Helix SecOps platform is part of a suite that includes SIEM to help IT take control from incident to detection to response.
- Trellix Insights provides threat intelligence to predict and prioritize threats and prescribe countermeasures.
- Trellix ePO security management platform helps IT control and administer all endpoints from a single console.
Pros
- A central view of potential threats with built-in workflows removes complexity.
- Get greater transparency monitoring users, applications, networks and devices.
- Real-time threat identification and response reduces lead time to protect against threats.
- Can integrate products from 650+ third-party vendors.
Cons
- The full Trellix suite is needed to provide complete remediation capabilities.
- Some users complain that it can be slow to respond.
AT&T USM Anywhere: Best for asset discovery

AlienVault Unified Security Management platform (USM) is now AT&T USM Anywhere. It discovers assets and gathers data about running services, users, operating systems and hardware information. This asset focus means it can pick up any devices in the environment that it protects.
Pricing
- The essentials version starts at $1,075 per month. The standard starts at $1,695 per month and the premium at $2,595.
Features
- Automatically collects and analyzes data across the attack surface.
- Threat intelligence provided by AT&T Alien Labs.
- Supports an ecosystem of AlienApps to orchestrate and automate actions towards other security technologies and respond to incidents.
Pros
- Good for those who want their cybersecurity and SIEM services managed by someone else.
Cons
- Not suitable for organizations that need to maintain tight control over their own assets for sensitivity or compliance reasons.
Key features of SIEM software
All SIEM software tools take care of log monitoring and management. Further important features include whether the tool is cloud-based, whether it can be hosted on-prem, whether it includes remediation capabilities and what platforms it runs on.
Cloud
These days, most SIEM software is based in the cloud. Cloud-based products are easier to deploy, easier to manage and simpler to run. And with so many enterprises operating in one or more clouds, SIEM tools in the cloud are a must-have. Some vendors provide SIEM on a Software-as-a-Service (SaaS) basis, and others offer it as a fully managed service.
Hosted On-prem
Some enterprises are averse to operating in the cloud due to privacy, security or compliance reasons. They need to load SIEM on their own internal servers. Some vendors offer this option, while others don’t.
Remediation
SIEM originated as a way to simplify the compilation and analysis of security logs. It provided enterprises with a way to evaluate huge numbers of log entries and alerts and detect potential issues or intrusions. More recently, however, SIEM platforms have begun to add remediation capabilities. Some offer ways to automate a limited number of remediation actions. But a few tools provide access to a wide range of security remediations, either within the SIEM itself or via integrated or associated tools provided by the same vendor.
Platforms
The SIEM market is highly competitive. Most vendors have to provide tools that operate on all major operating systems and cloud environments. But there can be a few holes. Those with an extensive Google Chrome presence, for example, may find their SIEM options limited. It is vital, therefore, to verify that your potential vendor of choice is fully set up to run their systems in your environment.
How do I choose the best SIEM software for my business?
Every one of the products outlined here offers quality security protection and would be of value to any organization — and every organization needs some level of log-based real-time security analysis to help prevent and detect threats.
Making the right choice when selecting SIEM software is going to depend on company priorities, requirements, budget, level of IT expertise and level of IT availability to assess and handle threats. If money is no object and tech staff isn’t able or willing to roll up its sleeves and tackle security risks, a managed SIEM like USM Anywhere may be the way to go. If company budgets are less robust and in-house talent and time are copious, SolarWinds SEM, Datadog or AlienVault would be among the candidates. Otherwise, options such as LogRhythm, CrowdSrike, Splunk, RSA , IBM QRadar and ManageEngine should be high on the list of those to consider.
Methodology
The SIEM tools covered here were selected based on their prominence in analyst reports as well as user reviews.

