- Learn with Cisco at Cisco Live 2025 in San Diego
- This Eufy robot vacuum has a built-in handheld vac - and just hit its lowest price
- I highly recommend this Lenovo laptop, and it's nearly 50% off
- Disney+ and Hulu now offer prizes, freebies, and other perks to keep you subscribed
- This new YouTube Shorts feature lets you circle to search videos more easily
Apple Vulnerability Can Expose iOS and macOS Passwords, Safari Browsing History
This Safari vulnerability has not been exploited in the wild. Apple offers a mitigation, but the fix needs to be enabled manually.
Security researchers from three universities have discovered a major vulnerability in Apple’s iOS and macOS, including the Safari browser. The vulnerability, which the researchers named iLeakage, enables threat actors to read Gmail messages, reveal passwords and uncover other personal information.
The vulnerability affects macOS or iOS devices running on Apple’s A-series or M-series CPUs, which include all modern iPhones and iPads, and laptops or desktops released since 2020. Macs can only be attacked when using Safari, but mobile devices are vulnerable when using any browser.
The researchers disclosed their findings to Apple on Sept. 12, 2022, and made the findings, as well as a research paper, public on Oct. 25, 2023. The iLeakage vulnerability has not yet been exploited in the wild as of October 27.
Jump to:
How does the iLeakage vulnerability work?
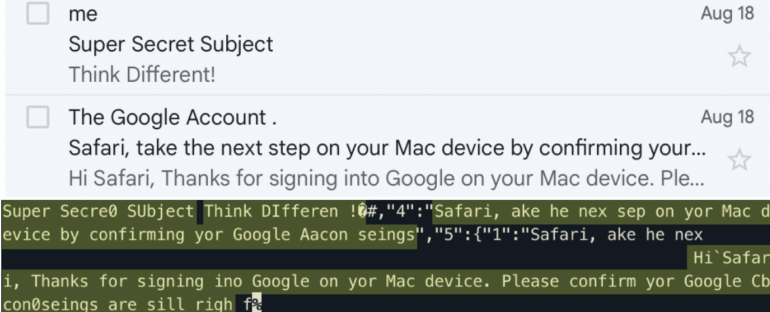
The iLeakage takes advantage of a transient execution side channel, which is a performance optimization feature of modern CPUs. The particular side channel involved here is speculative execution, which can be vulnerable to a hardware hack known as Spectre. Attackers can detect traces of speculative execution in CPUs, particularly the cache. Attackers can force the CPU to speculatively execute the wrong flow of instructions. Then, the attackers can read sensitive data contained in the resulting side channel (Figure A).
Figure A
The researchers who discovered the vulnerability are Jason Kim and Daniel Genkin of the Georgia Institute of Technology, Stephan van Schaik of the University of Michigan and Yuval Yarom of Ruhr University Bochum.
“Code running in one web browser tab should be isolated and not be able to infer anything about other tabs that a user has open,” the researchers wrote on their website about iLeakage. “However, with iLeakage, malicious JavaScript and WebAssembly can read the content of a target webpage when a target visits and clicks on an attacker’s webpage. This content includes personal information, passwords or credit card information.”
The researchers demonstrated iLeakage by setting up a website that opens up a hidden window on the target’s machine.
The researchers speculate that this vulnerability has not been found in the wild because it’s difficult to orchestrate, requiring detailed knowledge of Safari and of browser-based side channel attacks. However, iLeakage is important to know about because of its novel approach and because the number of devices potentially open to exploitation through iLeakage is so high.
TechRepublic has reached out to the researchers for more information.
SEE: Everything you need to know about Apple’s iOS 17 (TechRepublic)
How to defend against iLeakage on Apple devices
Apple has enabled a mitigation for iLeakage in macOS Ventura 13.0 and newer releases, but it takes some work to find it. To activate the mitigation, follow the instructions posted on the iLeakage site under “How can I defend against iLeakage?” to access Safari’s debugging menu. From there, you can find WebKit’s internal features and an option to disable swap processes on cross-site window openings, which prevents the iLeakage exploit from working.
Also, entering Lockdown Mode or disabling JavaScript prevents the iLeakage exploit from working, but doing so may cause some of Safari’s features not to work.
iLeakage can be hard to trace because it doesn’t appear in the system’s log files, the researchers said; instead, iLeakage resides entirely within Safari. Some evidence of the attacker website hosting iLeakage may be visible in Safari’s browser cache of recently visited pages if an attack has already taken place, the researchers said.

