- Broadcom grows revenues by 20% following VMware purchase, as customers fume about subscription costs
- How global threat actors are weaponizing AI now, according to OpenAI
- The viral Air Purifier Table is my smart home's MVP (and it's on sale for $179)
- Grab the Galaxy S25 Edge for $170 off and get a free Amazon gift card - but act fast
- How I learned to stop worrying and love my health tracker
Cloud Security API Updates Improve User's Experience

Welcome “Investigate API” into the Cisco Cloud Security API experience
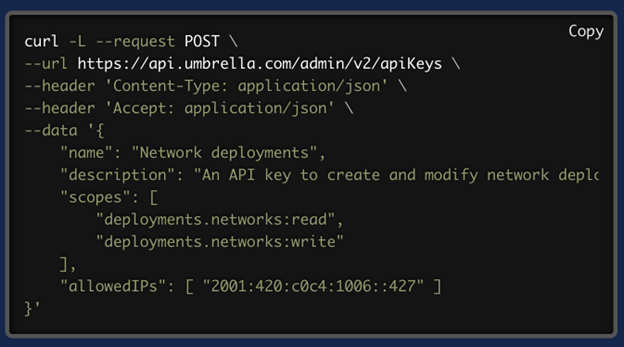
Developers and engineers can now leverage the new Umbrella API authentication to create API keys. This includes access to Investigate API alongside other Umbrella APIs, utilizing a modern OAuth2 mechanism. Previously, the process for authenticating the Investigate API involved generating a specific Investigate API token (basic authentication) via the Investigate section in the user interface.
Cisco customers and partners can also extensively utilize the Investigate API to enhance the data in their Security Information and Event Management (SIEM) systems, threat intelligence platforms, or incident management workflows. This enables them to promptly identify critical security events and provide additional information for security analysts and incident responders. The Investigate API is also a fundamental component in major integrations, such as Cisco XDR.
In the screenshot below you can see how you can now set the description for the related API Key in the Umbrella dashboard.
If we take into account cases where clients integrate Umbrella with a lot of 3d party platforms, descriptions can provide clarity as to the use of related API credentials. For example, you can add a description like “Investigate API Key with Read/Write admin scope for Splunk.”
Restrict API access from specific IPs
Limiting API access for a given API Key to a specific IP address or range of addresses is now possible. This significant security enhancement guarantees that customer API requests originate solely from secure and authorized locations. DevSecOps teams and administrators can now enforce that these requests are made exclusively from designated IP addresses or ranges and work with both IPv4 and IPv6 sources.
A few more API updates
Try these updates in the DevNet Sandbox
Give it a try! Play with these updates using the Umbrella DevNet Sandbox.
Share:

