- The Significance of Cybersecurity within AI Governance
- How to disable ACR on your TV (and stop companies from spying on you)
- I expected this cheap multitool to be a waste of money, but it's my new a toolbox essential
- Have The Last Word Against Ransomware with Immutable Backup
- Multi-channel Secure Communication
NIST Confusion Continues as Cyber Pros Complain CVE Uploads Stopped

Read more analysis about the NVD vulnerability backlog:
A recent rise in software vulnerability exploits has come as the US National Vulnerability Database (NVD), the world’s most comprehensive vulnerability database, experiences its most significant crisis in history.
After experiencing a vulnerability enrichment slowdown in mid-February 2024, experts working in software security have told Infosecurity that the database run by the US National Institute of Standards and Technology (NIST) stopped showing new vulnerabilities since May 9.
Cybersecurity professionals from the public and private sectors are trying their best to document the three-month-long vulnerability backlog and fill the gaps where they can.
Three Months of Vulnerability Backlog
Since issues with vulnerability enrichments first emerged on February 12, NIST has analyzed only 4524 of the 14,286 common vulnerabilities and exposures (CVEs) received so far this year.
Having so many unanalyzed vulnerabilities means attackers have an opportunity to exploit them.
Speaking to Infosecurity at the RSA Conference, Immanuel Chavoya, CEO and Founder of RiskHorizon.ai, said he observed that vulnerabilities that have not yet been fully processed by the NVD were being actively exploited in the wild.
Many companies rely on the NVD to perform update and patch cycles.
Missing New CVEs
Infosecurity has spoken to many experts who noticed that no new vulnerabilities have been uploaded on the NVD for a few days.
Software security professionals shared internal Slack conversations from within their community with Infosecurity. The Slack messages between these cybersecurity specialists, including some from within government agencies, show discussions confirming that no new CVEs have been added through the NVD application programmable interface (API) since May 9.
Andrey Lukashenkov is head of revenue at Vulners, a website that provides information on security vulnerabilities and exploits. He told Infosecurity that the Vulners website shows that the last fully formed CVE was added by the NVD processing robot on May 9.
The issue is also shown on the website of CVE.ICU, a research project that provides a deeper understanding of software vulnerability disclosures. CVE.ICU is run by Jerry Gamblin, a principal engineer at Cisco Threat Detection & Response.
The CVE program, run by MITRE, is still running.
Format Migration Led to Technical Issues
Infosecurity has contacted NIST about the alleged CVE uploading halt. A NIST spokesperson denied any disruption in vulnerability processing. The issues were due to the NVD migrating to the new CVE JSON format.
“We had not stopped processing CVEs. However, we were updating our system to support the new CVE list data specification. Public posting was put on hold while the update was in progress and has resumed as of this morning [May 14, 2024],” the NIST spokesperson told Infosecurity.
“At least they could have told all the users what they are up to,” Lukashenkov commented on social media.
Private Firms Fill the NVD Backlog Gap
In March, the NVD program manager, Tanya Brewer, announced at VulnCon that NIST would establish a consortium to address challenges in the NVD program.
However, Brewer and the NVD have remained vague about the cause of the disruption.
At the time of writing, the consortium has not been officially launched, and its mention has been removed from the NVD website.
In the meantime, many software security professionals, including Garrity and Chavoya, have been trying to keep track of the vulnerability backlog by publishing regular updates on the number of unanalyzed vulnerabilities.
Others are also attempting to fill the vulnerability analysis gap.
RiskHorizon.ai, for instance, launched the NVD Backlog Tracker, a free visibility platform covering the vulnerabilities unprocessed by the NVD.
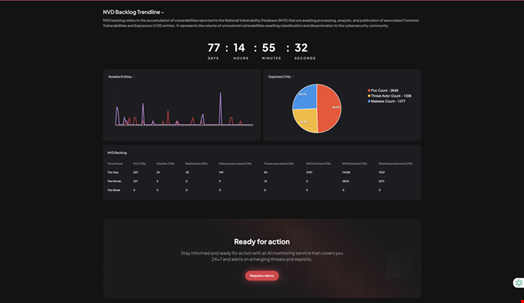
Chavoya, the company’s CEO, explained it to Infosecurity during the RSA Conference: “With our data fabric ingesting threat telemetry from the deep and dark web and our AI-powered solution analyzing them, we were able to take all the backlog vulnerabilities and inform our users about critical metadata, including the severity of the vulnerabilities, whether they available proof-of-concept exploits, whether they are being actively exploited and by which threat actors.”
Chavoya claimed his company now covers 85% of the backlog vulnerabilities.
Other security researchers from the private sector have increased their efforts in publishing new CVEs.
Read more: Cybersecurity Pros Urge US Congress to Help NIST Restore NVD Operation
The Trend Micro Zero Day Initiative published 709 unique CVEs on May 5, the most by a single CVE Numbering Authority (CNA) in a day.
Finally, VulnCheck recently released VulnCheck NVD++, a free alternative to the NVD API, another element of the NVD program that has been facing technical issues.
CISA to the NVD’s Rescue
On May 8, the US Cybersecurity and Infrastructure Security Agency (CISA) announced that it was starting a new software vulnerability enrichment program called ‘Vulnrichment.’
It will focus on adding metadata to CVEs, including Common Platform Enumeration (CPE) numbers, Common Vulnerability Scoring System (CVSS) scores, Common Weakness Enumeration (CWE) nametags, and Known Exploited Vulnerabilities (KEV) entries.
CISA said it recently enriched 1300 CVEs and continues to diligently work to ensure all submitted CVEs are enriched.
The Agency has asked all CVE Numbering Authorities (CNAs) to provide complete CVEs when making their initial submission to CVE.org.
Read more: Navigating the Vulnerability Maze: Understanding CVE, CWE, and CVSS
That same day, the MITRE-run CVE Program announced that new CNA Operational Rules had been approved. They will be effective from August 8, 2024.
These efforts to fill the NVD backlog gap have been welcomed by the cybersecurity community.
However, RiskHorizon.ai’s Chavoya told Infosecurity that they are short-term fixes rather than sustainable initiatives.
He believes the entire vulnerability disclosure process must be updated and that automated reporting should prevail.
Garrity agreed: “I think automation is the way forward. However, I think work should be done directly at the CVE level rather than at the NVD level.”
Read more: How to Disclose, Report and Patch a Software Vulnerability
Image credits: Patrick Garrity, grandbrothers/Shutterstock

