- Nvidia aims to bring AI to wireless
- Anthropic's new AI models for classified info are already in use by US gov
- My cat loves this automatic wet food feeder, and it's on sale
- Certified and Unstoppable: Recertify with Rev Up
- Walmart's drone delivery spreads its wings to 100 more stores - is yours one?
Accelerate XDR Outcomes with NDR and EDR

Cybersecurity attacks complication and damaging impact are always keeping SOC analyst at their edge. Extended Detection and Response (XDR) solutions tend to simplify for Sam, a SOC analyst, his job by simplifying the workflow and process that involve the lifecycle of a threat investigation from detection to response. In this post we will explore how SecureX, Secure Cloud Analytics (NDR), Secure Endpoint (EDR) with their seamless integration accelerate the ability to achieve XDR outcomes.
Meaningful incidents
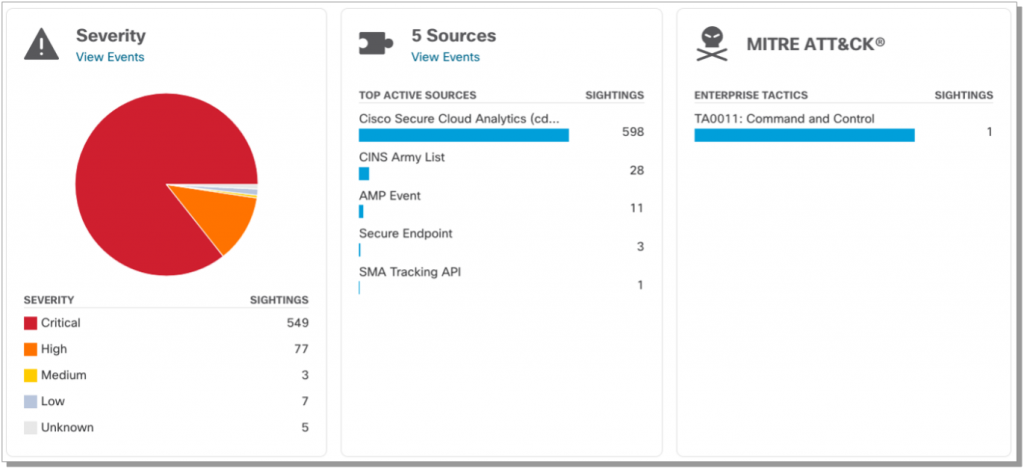
One of the first challenges for Sam is alert fatigue. With the overwhelming number of alerts coming from multiple sources and the lack of relevance or correlation, decreases the value of these alerts to the point that they become as meaningless as having none. To counter this effect, Cisco Secure Cloud Analytics and Cisco Secure Endpoint limit alert promotion to SecureX to only include high fidelity alerts with critical severity and marking them as High Impact incidents within SecureX Incident manager.
This capability reduces the noise coming from the source, while keeping the other alerts available for investigation, putting impactful incidents at the top of Sam’s to do list. Now, Sam is confident that his time is spent in a prioritized manner and helps ensure he is tackling the most important threats first. Automatic incident provisioning accelerates incident response by bringing focus on the most impactful incidents.
Valuable enrichment
Understanding the mechanics and data around a specific incident is a key factor for Remi, an incident responder, in his day-to-day work. Achieving his tasks accurately is tightly coupled with his ability to scope and understand the impact of an incident and to gather all possible data from the environment which can be associated with an incident including devices, users, files hashes, email ids, domains IPs and others. SecureX Incident Manager’s automatic enrichment capability completes this data collection for high impact incidents automatically. The data is then classified into targets, observables, and indicators and added to the incident to help the analyst better understand the incident’s scope and potential impact.

The Incident Manager and automatic enrichment provides Remi with crucial information such as the associated MITRE Tactics and Techniques applied during this incident, the contributing threat vectors, and security solutions. In addition, the Incident Manager aggregates events from multiple sources into the same high impact incident that the enrichment was triggered on future providing Remi with more vital context.
This automatic enrichment for high impact incidents is essential to Remi’s understanding as much as possible about an incident as it occurs and significantly accelerates him identifying the proper response for the threat. This brings us to the next step in our incident detection to response workflow.
Faster response and investigations
It is important for an XDR to correlate the right information for the Security Analyst and incident responder to understand an attack but it is equally important to provide an effective response mechanism. This is exactly what SecureX provides with the ability to apply a response to an observable with a simple a single click or through automation.
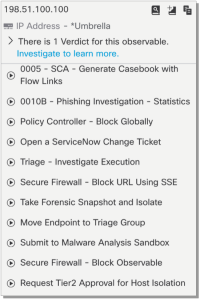
These workflows can be invoked to block a domain, IP or URL across a full environment with a simple click, leveraging existing integrations such as firewalls or umbrella and others. Workflows can be made available to the threat response pivot menu where they are useful for performing specific host specific actions, such as isolate a host, take a host snapshot, and more.
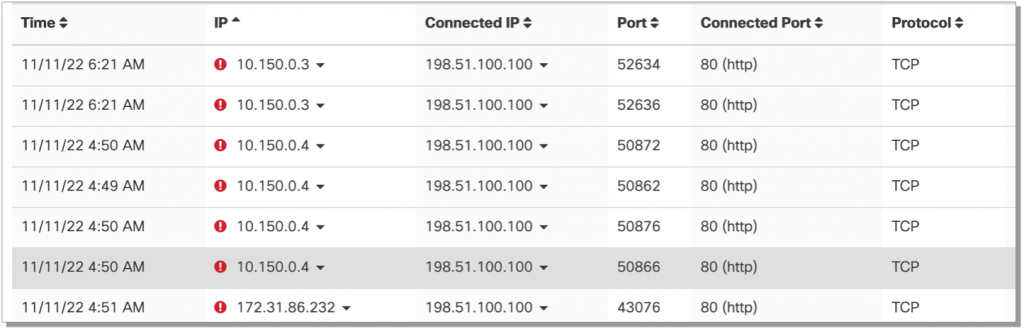
In addition to response workflows, the pivot menu provides the ability to leverage Secure Cloud Analytics (SCA) telemetry by generating a case book linking back to telemetry searches within SCA. This automation is critical to understanding the spread of a threat across an environment. A good example on this, is identifying all hosts communicating to a command-and-control destination before this destination was identified as malicious. This is a pre-existing SecureX workflow which can be taken advantage of today see workflow 0005 – SCA – Generate Case book with Flow Links.

Automating responses
Reducing time to remediation is a key aspect of keeping a business secure, SecureX orchestration automates responses with various solutions specially with NDR detections from SCA and use observables from these alerts to isolate hosts leveraging Secure Endpoint. SCA can send alerts via Webhooks and SecureX Orchestration receive them as triggers to launch an NDR- EDR workflow to isolate hosts automatically. (0014-SCA-Isolate endpoints from alerts)
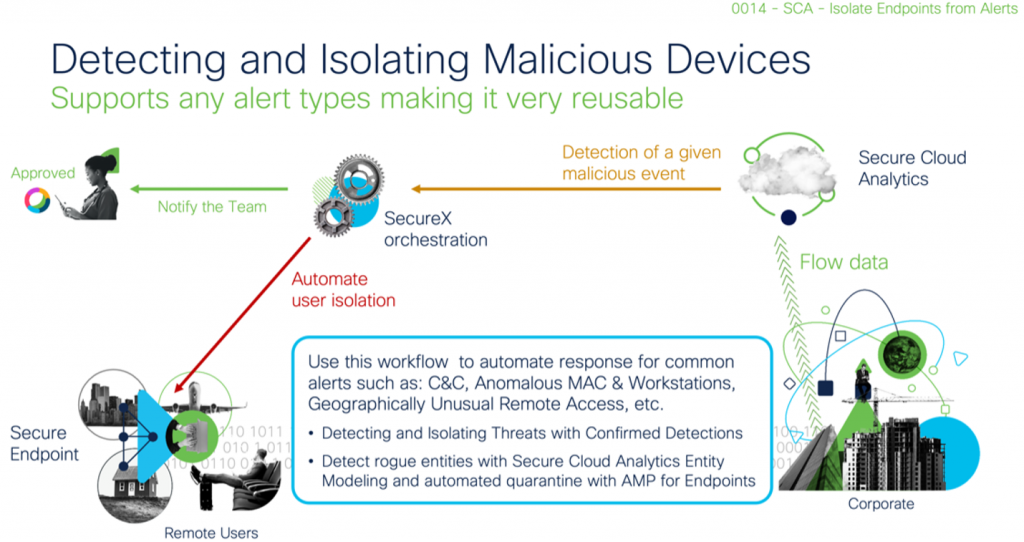
This orchestration workflow automatically isolates rogue devices in a network or contain confirmed threat alerts received from Cisco’s Machine learning threat detection cloud and can be used for multiple different response scenarios.
The power of automation brought by SecureX, Secure Cloud Analytics and Secure Endpoint accelerates XDR outcomes drastically which simplifies Security Analyst (Sam) and Incident Responder (Remi) jobs and make it more efficient with accurate incident prioritization, automatic investigation/enrichment and most importantly automating responses.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Instagram
Facebook
Twitter
LinkedIn
Share:

