- From Alexander Graham Bell to an AI assistant guiding your customer journey, CX has come a long way (baby)!
- Cisco U. Spotlight: Your Best Day of Learning is Waiting
- A data-driven farming revolution: Smart Greenhouse in Greece
- さくらインターネットのCIOが語る「CIOの役割や魅力」とは
- These backyard solar panels are saving me $30 a month - Here's how
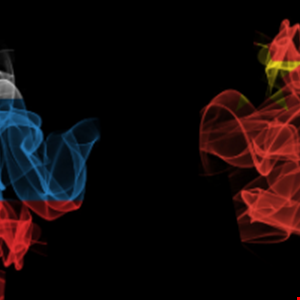
Chinese SilkLoader Malware Sold to Russian Cyber-Criminals
A piece of malware designed to load Cobalt Strike beacons onto victim machines has been traced back to both Chinese and Russian threat actors.
Finnish security vendor WithSecure claimed in a new report that it detected “SilkLoader” in several human-operated intrusions that were likely the precursor to a ransomware attack.
The malware uses DLL sideloading to load the beacons, which are commonly used in such attacks as part of command-and-control (C2) infrastructure, to download additional payloads on targeted machines.
However, the novelty about this case comes from the fact that WithSecure believes Chinese threat actors actually sold or gave their wares to Russian peers.
The firm said that before summer 2022 the loader was used exclusively by the former against targets in Hong Kong, China and elsewhere in the region. However, that activity ceased in July only for the malware to reappear a couple of months later in attacks against different targets in different countries, including Taiwan, Brazil and France.
“We believe SilkLoader is currently distributed within the Russian cybercrime ecosystem as an off-the-shelf loader through a Packer-as-a-Service program to ransomware groups, or possibly via groups offering Cobalt Strike/Infrastructure-as-a-Service to trusted affiliates,” said WithSecure Intelligence researcher Mohammad Kazem Hassan Nejad.
“Most of the affiliates appear to have been part of or have had close working relationships with the Conti group, its members and offspring after its alleged shutdown.”
The tool itself is just the latest example of threat actors innovating to stay one step ahead of network defenders. In the case of Cobalt Strike, the tool is so well known that defensive measures will usually detect and contain the threat.
“However, by adding additional layers of complexity to the file content and launching it through a known application such as VLC Media Player via sideloading, the attackers hope to evade these defense mechanisms,” explained Nejad.
The bigger picture is that cybercrime is increasingly global. Although historic language and cultural barriers have largely prevented information sharing between Chinese and Russian language cybercrime economies, that may be changing.
“In this case, it is more likely that the author was an independent coder who sold their tool on an underground forum,” the report claimed. “Such components can and are sold or handed over to other groups when the situation favors such a transaction.”

