- Google just spilled its airfare secrets: here's the cheapest day to book your next flight
- #Infosec2025: Top Six Cyber Trends CISOs Need to Know
- I tested Hisense's flagship Mini LED TV, and it left me with no OLED envy (especially at $700 off)
- Finally, an Android tablet that I wouldn't mind putting my iPad Pro away for
- 8 communication strategy tips for IT leaders
Combatting ransomware with layered Zero Trust Security

Ransomware is a growing threat to organizations, according to research independently conducted by Enterprise Strategy Group and sponsored by Zerto, a Hewlett Packard Enterprise company.
According to the report, 2023 Ransomware Preparedness: Lighting the Way to Readiness and Mitigation, 75% of organizations experienced ransomware attacks in the last 12 months, with10% facing daily attacks.[i]
46% of organizations experienced ransomware attacks at least monthly—with 11% reporting daily attacks.
“Regardless of whether the attack was successful, the reality is that it’s not a matter of if an attack will occur, but rather when it will strike,” the report stated. “Therefore, it’s crucial to acknowledge that ransomware poses a significant and immediate threat that cannot be ignored, and immediate action must be taken to combat it.”
Ransomware defense can be challenging. Sophisticated and well-funded cybercriminals often target high-profile organizations, conducting surveillance to effectively attack vulnerable users—employees and, more recently, third-party service providers with access to data from many different organizations.[ii] Social engineering and phishing emails (as well as texts and voice contacts) are the most common attack vectors for ransomware.[iii] Once the victim clicks on an infected attachment or link, malware is installed and ransomware can spread.
Defending against ransomware with Zero Trust Security
A good cybersecurity defense strategy starts with user education and threat awareness. When those measures fall short, Zero Trust Security can fill the gaps.
Zero Trust Security models support least-privilege access—restricting user and device access to just the resources needed to do their job or fulfill their function, as long as the subject meets security posture requirements and is not suspected of compromise.
Note that Zero Trust is a security paradigm—not a single product. In fact, the role-based network access controls at the core of Zero Trust are often cobbled together across multiple disparate solutions in a disjointed fashion, requiring manual effort, adding complexity, and increasing risk of inconsistencies.
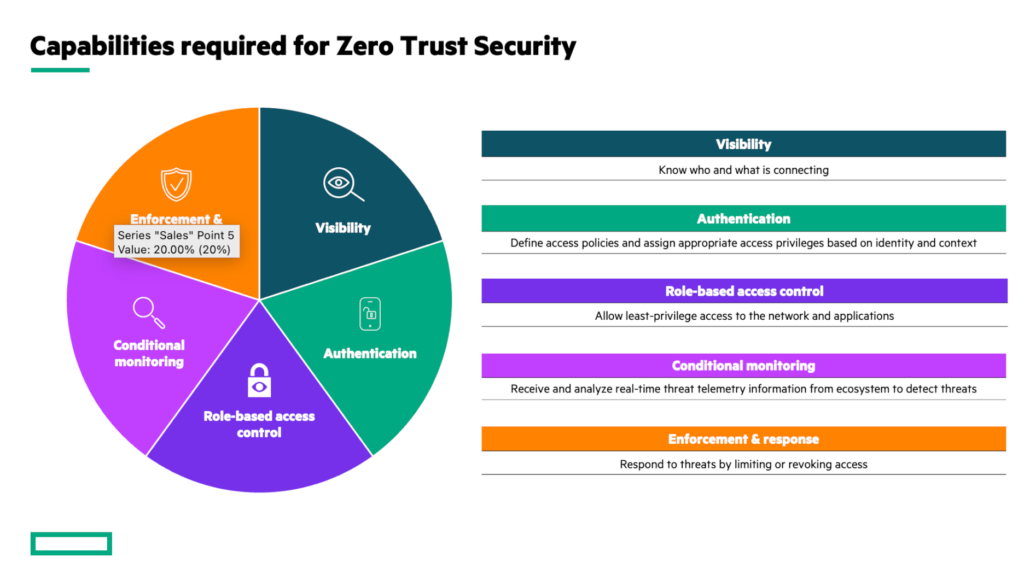
Five core capabilities form the foundation of Zero Trust Security.
The importance of layered security
A layered Zero Trust Security approach to combatting ransomware involves establishing and continuously monitoring trust across multiple layers—potential attack surfaces and propagation points—of the IT architecture. Zero Trust Security trust mechanisms can be fortified by additional defenses and security services.
As a first step, consider the role the network can play in protecting the organization against ransomware.
- Identify and destroy malware before it takes hold. An employee receives an email with malware cloaked behind a legitimate-looking attachment—the organization is now just one click away from a potentially catastrophic ransomware incident. Organizations need a way to thwart malware-based attacks before they can propagate. HPE Aruba Networking SSE can help with a sandbox feature that enables organizations to test suspicious files in a safe virtual environment and destroy malicious files before they cause damage.
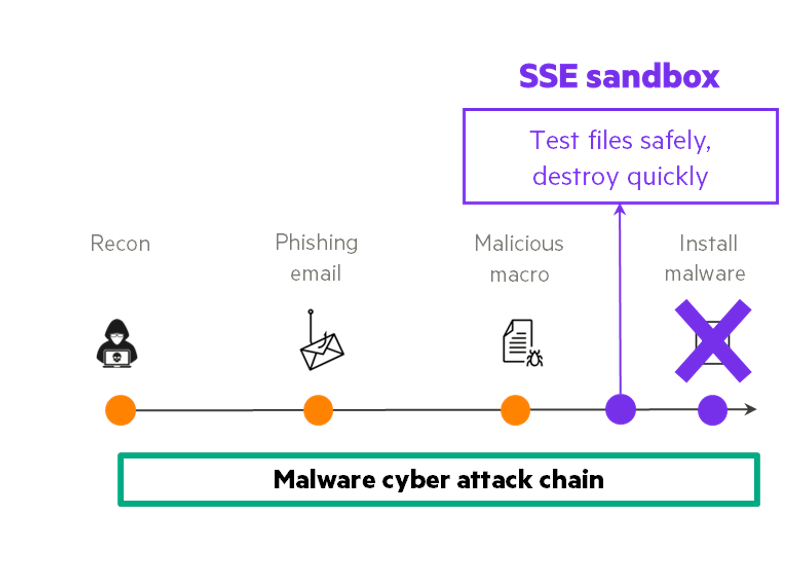
Sandbox capabilities from HPE Aruba Networking SSE thwart ransomware attacks by destroying malicious files before they cause damage.
- Prevent compromised devices from accessing the network. Should an attack originate via a corporate or BYOD endpoint device, endpoint and extended detection and response (EDR and XDR) systems can analyze and detect anomalous behavior to raise an alert. With HPE Aruba Networking ClearPass, IT teams can define policies that automate network enforcement and response based on threat telemetry data supplied by EDR/XDR solutions within the Aruba 360 Security Exchange. For example, when the EDR/XDR suspects a device is participating in an attack, ClearPass network access control can automatically limit or revoke network access pending further investigation.
- Limit lateral spread of attacks. Over-broad or poorly monitored network access policies can make it easier for attacks to expand throughout the organization. This lateral spread can lead to increased damage, more difficult remediation, and longer data breach response times. To avoid this, try a multi-pronged approach to delivering least-privilege access. For users that do not require corporate network access, HPE Aruba Networking ZTNA delivers least-privilege access to applications, providing a direct, secure path to the applications users need while restricting their access to other parts of the network, reducing potential attack surface. For users and devices on the network, Dynamic Segmentation unifies role-based access and continuous policy enforcement across network infrastructure, ensuring subjects only communicate with destinations consistent with their role, context, and security posture.—This prevents compromised devices from reaching corporate resources and external malware sites.
Given the increasing sophistication of ransomware attacks, not all attacks may be thwarted at the network level. Continuous data protection plays an important part in comprehensive ransomware protection strategies by enabling organizations to manage, protect, recover, and move data and applications across on-premises or cloud destinations. Ransomware resilience solution Zerto detects anomalous encryption activity in real-time, then allows organizations to quickly rewind to a point in time just prior to the infection and restore the unencrypted files and VMs.
As a last line of defense, the Zerto Cyber Resilience Vault—including HPE Aruba Networking switching—uses an ultra-secure Zero Trust architecture to provide an ironclad recovery solution tailored to specific regulatory and compliance requirements.
Protect your organization with Zero Trust Security
Though Cybersecurity Awareness Month may be wrapping up, it’s always a good time to explore how Zero Trust Security can protect your organization from threats like ransomware. Check out these resources to learn more.
[i] 2023 Ransomware Preparedness: Lighting the Way to Readiness and Mitigation. Enterprise Strategy Group. September 2023.
[ii] Rundle, J. “Ransomware Comes Back in Vogue for Cybercriminals.” Wall Street Journal Pro Cybersecurity. October 17, 2023.
[iii] Kelley, D. “Top 3 ransomware attack vectors and how to avoid them.” Tech Target. August 2023.
Copyright © 2023 IDG Communications, Inc.

