- NotebookLM now lets you share your notebooks with anyone with a single link. Here's how
- Cornelis Networks offers alternative to Infiniband or Ethernet for HPC and AI networks
- Skip the iPad Pro and save $50 on Apple's newest 11th Gen iPad right now
- Claude Pro's two new features make this AI subscription even more enticing
- This Android smartwatch from 2024 still outperforms the competition - and it's on sale
CVE-2020-14871: Critical Buffer Overflow in Oracle Solaris Exploited in the Wild as Zero-Day

Researchers disclose critical zero-day vulnerability in Oracle Solaris that was exploited in the wild by an uncategorized threat actor.
Background
On November 2, researchers at FireEye published a blog post detailing findings from a Mandiant incident response investigation that led to the discovery of an uncharacterized (UNC) group they refer to as UNC1945. As part of this investigation, they discovered that UNC1945 was leveraging a critical Oracle Solaris zero-day vulnerability to install a backdoor as part of their attacks.
Image Source: Twitter
On November 4, FireEye published a follow-up blog post providing additional details about the vulnerability.
Analysis
CVE-2020-14871 is a critical pre-authentication stack-based buffer overflow vulnerability in the Pluggable Authentication Module (PAM) in Oracle Solaris. PAM is a dynamic authentication component that was integrated into Solaris back in 1997 as part of Solaris 2.6. The vulnerability received a CVSSv3 score of 10.0, the maximum possible score. The Tenable VPR score for this vulnerability is also 10.0 at the time of publication.
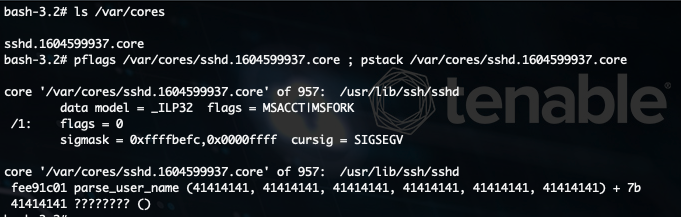
The vulnerability exists in the PAM library’s parse_user_name function due to the improper input validation of a username that exceeds a certain length (512 bytes). An unauthenticated, remote attacker could exploit the vulnerability by attempting to log in to a vulnerable Solaris server via Secure Shell (SSH) keyboard-interactive authentication, a passthrough authentication method that has support for PAM. Using a specially crafted request containing a username that exceeds 512 bytes, the attacker could pass limitless input to the PAM parse_user_name function after forcing the keyboard-interactive authentication to prompt for a username.
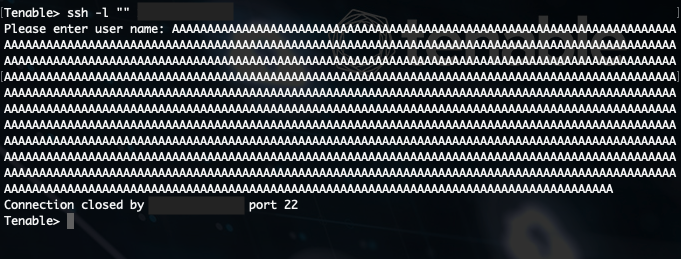
Determining whether or not the remote server is vulnerable is as simple as looking at the server’s response to this request. If the server returns an “Authentication failed” message, the server is vulnerable. If the server continues to provide the username prompt, the server is not vulnerable.
Exploitation via SSH not possible on Oracle Solaris 11.1 and higher
The researchers note that in Oracle Solaris versions 11.1 and higher, the vulnerability still persists in the parse_user_name function. However, they determined that an unintentional change made to the PAM library negates the exploitation vector via SSH as a result of the username being truncated prior to being passed to the parse_user_name function.
Zero-day exploit reportedly acquired for $3,000 dollars
In their initial blog post regarding UNC1945, the researchers say they identified an advertisement for an “Oracle Solaris SSHD Remote Root Exploit” in the underground market that was being sold for $3,000 dollars. They believe that this is likely where the UNC1945 attackers obtained the exploit tool, which they refer to as EVILSUN.
Vulnerability has persisted in PAM library for many years
The researchers also point out that this vulnerability has likely persisted in PAM “for decades” because most applications may already perform input validation on the username before it gets passed to the PAM library. However, SSH is not one of them, which is how the attackers managed to exploit this flaw.
On October 22, a commit was pushed to the Illumos PAM library to address the parse_user_name function, which was called “sloppy” as part of the commit message. This means that other technologies implementing PAM are also likely to be vulnerable and this issue may not be unique to Solaris.
Attackers used BlueKeep vulnerability for additional reconnaissance
While CVE-2020-14871 was used to gain initial access to victim networks, the researchers also discovered the use of a variety of tools, including the use of the BKScan toolkit, which contains an exploit for CVE-2019-0708, a critical remote code execution vulnerability in Microsoft’s Remote Desktop Protocol. Dubbed “BlueKeep” by security researcher Kevin Beaumont, the vulnerability was patched in May 2019 as part of Microsoft’s Patch Tuesday.
Proof of concept
A security researcher that goes by the pseudonym Hacker Fantastic has published a proof-of-concept (PoC) exploit for CVE-2020-14871 to their GitHub page.
On x86 and Intel architecture, CVE-2020-14871 is so trivial to exploit. It’s literally 512 bytes+ebp+eip and straight forward control of the program counter, you just need to ROP your shellcode in. pic.twitter.com/K0pklCNt0a
— Hacker Fantastic (@hackerfantastic) November 3, 2020
Solution
CVE-2020-14871 was addressed in Oracle’s quarterly Critical Patch Update (CPU) in October. The following table lists the affected versions and availability of security updates.
| Affected Version | Availability of Security Updates |
|---|---|
| Oracle Solaris 11 | Yes |
| Oracle Solaris 10 | Yes |
| Oracle Solaris 9 | No |
Since October 2014, Oracle Solaris 9 is no longer receiving extended support. Oracle Solaris 9 customers are encouraged to upgrade to a supported version as soon as possible.
If upgrading is not feasible at this time, FireEye recommends modifying the sshd_config file and configuring the ChallengeResponseAuthentication and KbdInteractiveAuthentication options to no. This will limit the current attack vector that UNC1945 and others have attempted to exploit, but there may be other ways to trigger the exploit. This mitigation should only be applied on a temporary basis until upgrading is feasible.
Identifying affected systems
A list of Tenable plugins to identify this vulnerability can be found here.
Additionally, a compliance audit file, available here, can be used to ensure that the ChallengeResponseAuthentication and KbdInteractiveAuthentication configuration options are set to no.
Get more information
Join Tenable’s Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.

