- Why I recommend this OnePlus phone over the S25 Ultra - especially at this new low price
- I replaced my laptop with Microsoft's 12-inch Surface Pro for weeks - here's my buying advice now
- This palm recognition smart lock doubles as a video doorbell (and has no monthly fees)
- Samsung is giving these Galaxy phones a big One UI upgrade - here's which models qualify
- 7 MagSafe accessories that I recommend every iPhone user should have
CVE-2021-20123, CVE-2021-20124: DrayTek Vulnerabilities Discovered by Tenable Research Added to CISA KEV

With patches out for three years, attackers have set their sights on a pair of vulnerabilities affecting DrayTek VigorConnect.
Background
In November 2021, the Cybersecurity and Infrastructure Security Agency (CISA) launched its Known Exploited Vulnerabilities (KEV) Catalog, an effort to focus on vulnerabilities known to have been exploited and provide defenders with an actionable list of vulnerabilities to prioritize their remediation efforts. On September 3, CISA added three new vulnerabilities to the KEV, two of which were discovered and responsibly disclosed to DrayTek by security researchers from Tenable Research.
| CVE | Description | CVSSv3 | VPR |
|---|---|---|---|
| CVE-2021-20123 | DrayTek VigorConnect Unauthenticated Local File Inclusion / Path Traversal Vulnerability | 7.5 | 7.7 |
| CVE-2021-20124 | DrayTek VigorConnect Unauthenticated Local File Inclusion / Path Traversal Vulnerability | 7.5 | 7.7 |
*Please note: Tenable’s Vulnerability Priority Rating (VPR) scores are calculated nightly. This blog post was published on September 9 and reflects VPR at that time.
Analysis
CVE-2021-20123 and CVE-2021-20124 are local file inclusion vulnerabilities affecting the DownloadFileServlet and WebServlet endpoints on DrayTek VigorConnect, a network management software used to manage and configure DrayTek network devices. Using a specially crafted request with path traversal sequences, an unauthenticated attacker can download arbitrary files from the underlying operating system with root privileges. These vulnerabilities were discovered by researchers at Tenable and disclosed to DrayTek, which subsequently released a patch in October 2021.
Despite these vulnerabilities having readily available patches for three years, nefarious actors have been observed exploiting these unpatched flaws, earning their spot on the CISA KEV list. As we’ve examined in multiple reports, including our 2020, 2021 and 2022 Threat Landscape Reports, known and exploitable vulnerabilities continue to be targeted by threat actors. Simply stated, these vulnerabilities continue to be targeted because they have well-known exploit code and actors continue to find unpatched and vulnerable targets to attack.
Despite the hype, few targets appear to be publicly available
Using platforms such as Shodan.io and a basic query for “draytek” we can see that a staggering over 700,000 assets are returned. Looking closer we note that nearly 610,000 of these devices have port 1723 open, the port used for Point-to-Point Tunneling Protocol (PPTP) on DrayTek Vigor routers. Such a vast number of internet-facing DrayTek assets makes large-scale attacks tempting to threat actors.
Source: Shodan.io
Yet, if we look at the number of internet-facing assets on Shodan.io, specifically for DrayTek VigorConnect based on device title, certificate elements or the hash value of its favicon, we see that only a handful of assets are exposed.

Source: Shodan.io
Looking at other platforms like FOFA, using the VigorConnect favicon hash value as an example, we can see that while the number returned is larger than that of Shodan.io with 44 results (37 unique IPs) it is still a relatively small number.
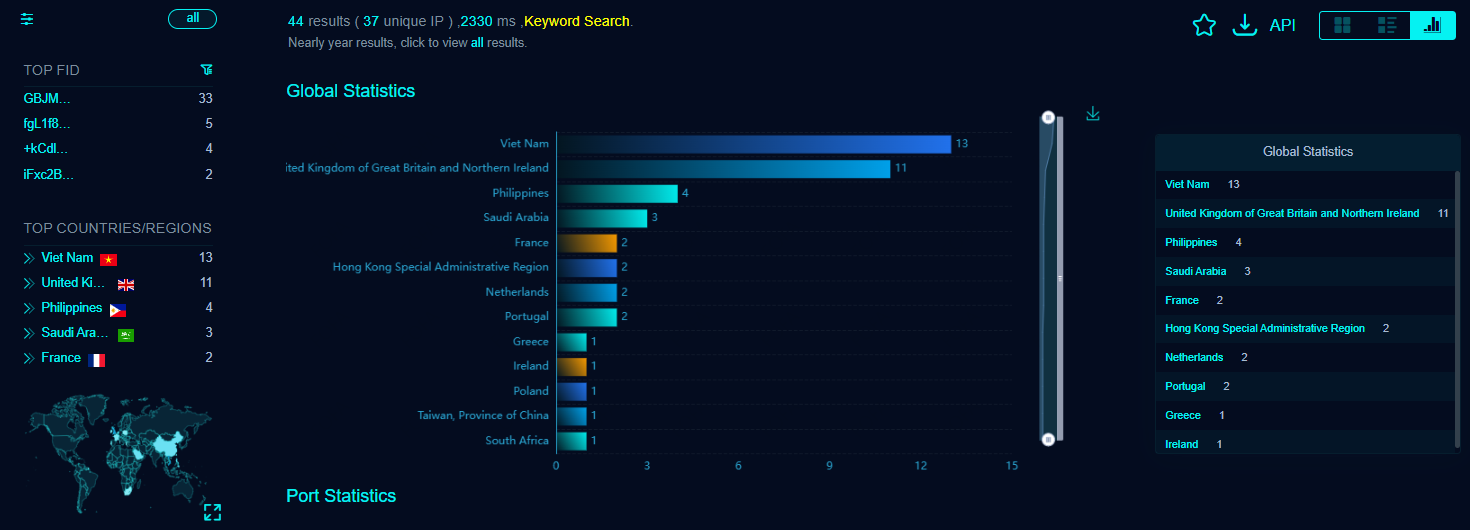
Source: FOFA
Threat actors might target DrayTek VigorConnect, despite having fewer than 50 internet-facing assets, because of the ease of exploiting a smaller number of systems, which could be automated. Despite the size of its attack surface, VigorConnect could provide access to sensitive network configurations and its reduced complexity might allow attackers to navigate and persist undetected. This makes it a strategic target for establishing access to larger networks while staying under the radar.
Attacks are on the rise
CISA has not provided evidence on the source or level of attacks observed in the wild but, looking at data from Shadowserver — which provides statistics based on server-side attacks seen by their honeypot sensor network — we get some limited insights. Looking at activity for the vendor DrayTek from September 1, 2024 to September 9, the date this blog was published, we can see an uptick in activity for connections to Shadowserver devices for CVE-2021-20123 and CVE-2021-20124. It’s worth noting that while the level of activity is not huge, this is only on Shadowserver devices, which represent a small and specific subset of exposed devices reflecting CISAs warnings regarding observed active exploitation.
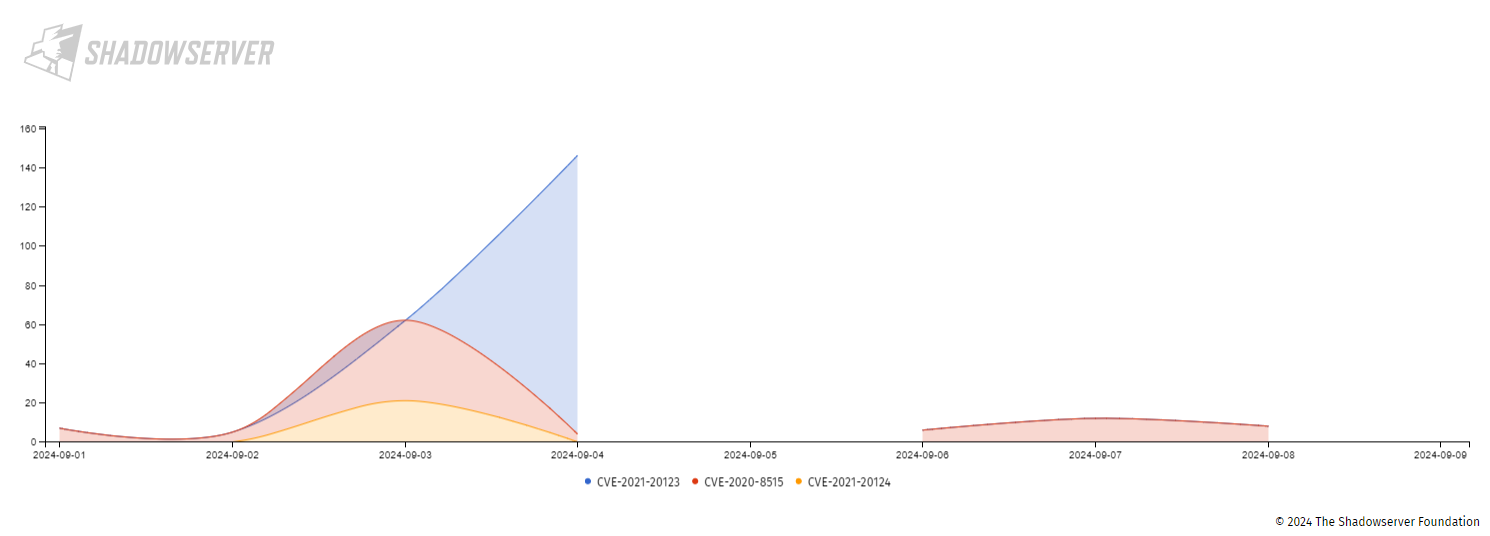
Source: Shadowserver
Proof of concept
As part of our responsible disclosure policy, Tenable regularly releases proof-of-concept (PoC) code with our Tenable Research Advisories (TRAs). In a coordinated release on October 8, 2021, Tenable released TRA-2021-42 which included PoCs for both CVE-2021-20123 and CVE-2021-20124.
Solution
DrayTek released VigorConnect version 1.6.1 on October 7, 2021, to address all of the vulnerabilities reported by Tenable Research.
Identifying affected systems
A list of Tenable plugins for this vulnerability can be found on the individual CVE pages for CVE-2021-20123 and CVE-2021-20124 as they’re released. These links will display all available plugins for these vulnerabilities, including upcoming plugins in our Plugins Pipeline.
Get more information
Join Tenable’s Security Response Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.

