- Broadcom grows revenues by 20% following VMware purchase, as customers fume about subscription costs
- How global threat actors are weaponizing AI now, according to OpenAI
- The viral Air Purifier Table is my smart home's MVP (and it's on sale for $179)
- Grab the Galaxy S25 Edge for $170 off and get a free Amazon gift card - but act fast
- How I learned to stop worrying and love my health tracker
CVE-2021-30116: Multiple Zero-Day Vulnerabilities in Kaseya VSA Exploited to Distribute REvil Ransomware

Zero-day vulnerabilities in popular remote monitoring and management software targeted by threat actors to distribute ransomware to reportedly over one million systems.
Background
On July 2, reports emerged that a number of companies whose networks are administered by managed service providers (MSPs) using Kaseya Virtual System Administrator (VSA), a remote monitoring and management (RMM) software from Kaseya Limited, became the victims of a large-scale ransomware attack.
The attacks have been attributed to REvil, also known as Sodinokibi, one of the most active ransomware groups today. REvil operates as a ransomware-as-a-service (RaaS), whereby they develop the ransomware payload itself and provide the infrastructure for managing victim communications for negotiating payment and distribution of decryption tools for victims post payment.
Image Source: Mark Loman (Twitter)
REvil does not attack organizations directly, rather they rely on affiliates, who do the dirty work to break into networks and deploy the ransomware. Affiliates receive a large portion of the ransom payment, while REvil takes a percentage for providing the ransomware and supporting infrastructure.
Similar to many other ransomware groups, REvil operates a leak website, where they publish the names of their victims along with a sampling of files they exfiltrated from the victim’s network. This is part of a tactic known as double extortion, which was pioneered by the Maze ransomware group in late 2019. Through double extortion, ransomware groups have seen their profits skyrocket, which has led to more activity in the space, and subsequently fueled the number of attacks.
Analysis
On July 5, Kaseya confirmed that multiple zero-day vulnerabilities were used to target vulnerable VSA server instances, including an authentication bypass flaw and an arbitrary command execution vulnerability. No specific details about the vulnerabilities were shared at the time and no additional CVEs have been reported.
Separately, researchers at Huntress Labs and TrueSec have identified potentially three zero-day vulnerabilities used as part of investigations into attacks against their clients, including:
- Authentication Bypass Vulnerability
- Arbitrary File Upload Vulnerability
- Code Injection Vulnerability
Huntress Labs, for example, believes the attackers were able to gain access to VSA servers through the use of the authentication bypass flaw.
“[…] we have high confidence that the threat actor used an authentication bypass in the web interface of Kaseya VSA to gain an authenticated session, upload the original payload, and then execute commands via code injection.”
In a later update from Huntress Labs, new evidence suggests that SQL injection may not have been the complete attack vector leading to code execution and another injection attack may be part of the attack chain.
Coordinated disclosure of zero-day vulnerabilities
On July 4, researchers at the Dutch Institute for Vulnerability Disclosure (DIVD) Computer Security Incident Response Team (CSIRT) published a blog post saying they’ve been working with Kaseya to coordinate the disclosure of “a number of zero-day vulnerabilities” in Kaseya VSA. They highlighted CVE-2021-30116, a vulnerability that they say is being used in these ransomware attacks, though they did not provide any further details about the other vulnerabilities. We suspect that these include the arbitrary file upload and code injection flaws.
While there has not been a direct confirmation, we assume that CVE-2021-30116 may be the authentication bypass vulnerability called out by Huntress Labs and TrueSec.
REvil publishes notice on their leak website
On July 4, REvil published a post to their leak website, confirming that they were behind the attack against Kaseya.
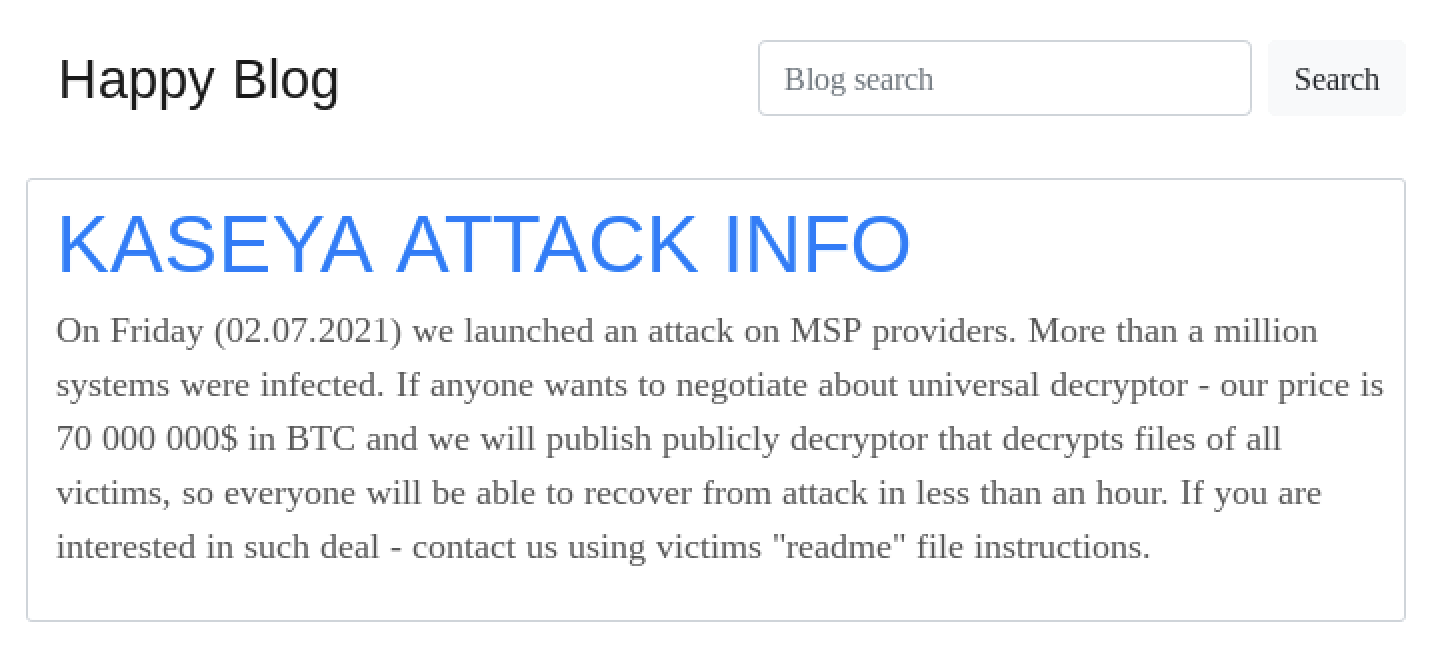
In the posting, REvil claims they have infected “more than a million systems” through this campaign and that they are willing to offer a universal decryptor tool for $70 million in Bitcoin, which could be used by any organization to decrypt files on systems that were struck by the REvil ransomware. If the number of systems infected is confirmed to be true, this attack would be considered the largest ransomware attacks ever conducted since the WannaCry ransomware attack in 2017.
Not the first time RMM tools have been targeted by ransomware groups
Over the last few years, threat actors have identified MSPs and RMMs as valuable targets for distributing ransomware to an MSP’s downstream customers. In February 2019, the GandCrab ransomware group exploited a two-year old vulnerability in the ConnectWise plugin for Kaseya VSA, which affected 126 Kaseya customers.
In December 2019, threat actors targeted an MSP and used the ConnectWise Control RMM software to distribute the Zeppelin Ransomware to the MSP’s downstream customers.
Because many organizations rely on MSPs to remotely monitor and manage their IT systems, and with the impact the attack against Kaseya VSA has had, we believe other ransomware groups will continue to look for flaws in other RMM software.
Proof of concept
At the time this blog post was published, there was no public proof-of-concept exploit for the vulnerability in Kaseya VSA.
Vendor response
Following the discovery of the vulnerability, Kaseya has been sharing updates for customers and other interested parties on their website. Kaseya proactively shut down their software-as-a-service (SaaS) servers while they investigated the attack, though they do not believe the attackers targeted SaaS customers. It appears the impacted organizations used Kaseya VSA on-premises.
Solution
Kaseya has stated that a patch has been developed and is undergoing “testing and validation” prior to being released to customers. SaaS servers are expected to be brought back online on July 6th between 2:00 PM – 5:00 PM EDT and the patch for on-premise customers is expected to be released within 24 hours after their SaaS servers are online.
Because the attack appears to have impacted Kaseya VSA on-premise customers, Kaseya has instructed those customers to shut down their VSA servers until a patch is available.
Identifying affected systems
Tenable has released a local Windows detection for Kaseya agents as well as a remote detection plugin for Kaseya VSA. When patches are available, we will update this blog with links to our version check plugin.
Get more information
Join Tenable’s Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.


