- I recommend the Pixel 9 to most people looking to upgrade - especially while it's $250 off
- Google's viral research assistant just got its own app - here's how it can help you
- Sony will give you a free 55-inch 4K TV right now - but this is the last day to qualify
- I've used virtually every Linux distro, but this one has a fresh perspective
- The 7 gadgets I never travel without (and why they make such a big difference)
Dark Pink APT Group Deploys KamiKakaBot Against South Asian Entities
The threat actor known as Dark Pink has been associated with deployments of the KamiKakaBot malware against multiple government entities in ASEAN (Association of Southeast Asian Nations) countries.
Threat researchers at EclecticIQ discussed the findings in a blog post published last week, explaining the observed attacks took place in February.
“In this new campaign, the relationship between Europe and ASEAN countries is very likely being exploited in the form of social engineering lures against military and government entities in Southeast Asian nations,” the report explained.
“Although researchers lack the conclusive proof needed to attribute the nationality of this group, the objectives of the attackers and some of the patterns suggest that the Dark Pink group could possibly be a Chinese APT group.”
The team added that the malicious campaigns were almost identical to those previously discovered by Group-IB.
“In January 2023, the threat actors used ISO images to deliver KamiKakaBot, which was executed using a DLL side-loading technique,” reads the EclecticIQ article. “The main difference in the February campaign is that the malware’s obfuscation routine has improved to better evade anti-malware measures.”
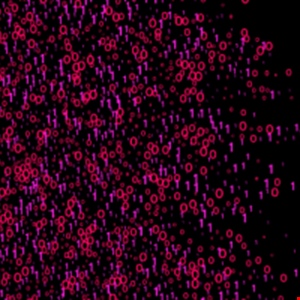
The KamiKakaBot malware, delivered via phishing emails during Dark Pink’s latest attacks, aims to steal credentials, browsing history and cookies from browsers like Chrome, Edge and Firefox. The malware also features remote code execution (RCE) capabilities.
“Developers of KamiKakaBot employ various evasion techniques to remain undetected while executing malicious actions on infected devices,” EclecticIQ wrote. “For example, they use living-off-the-land binaries (LOLBINs) […] to run the KamiKakaBot malware on victims’ devices.”
They also used legitimate web services as a Command and Control (C2) server, particularly Telegram, to further hide their malicious intentions.
To protect systems against Dark Pink and similar threats, EclecticIQ recommends companies use safe DLL search mode, disable mounting ISO images via group policy and disable browser password saving also via group policy, as well as deploy the highest level of protection on firewalls and endpoints.
The company’s advisory comes weeks after data from Proofpoint suggested phone attacks and multi-factor authentication (MFA) bypass techniques have been driving phishing attacks upward in 2022.

