- Learn with Cisco at Cisco Live 2025 in San Diego
- This Eufy robot vacuum has a built-in handheld vac - and just hit its lowest price
- I highly recommend this Lenovo laptop, and it's nearly 50% off
- Disney+ and Hulu now offer prizes, freebies, and other perks to keep you subscribed
- This new YouTube Shorts feature lets you circle to search videos more easily
Demystifying Multicloud Networking with Cisco Multicloud Defense

In today’s modern IT environment, most organizations leverage both the public cloud and private data center to house critical business applications. In many cases, these applications require communication with other applications to execute a particular need for the business. A common challenge among the customers I have spoken with is that they have applications in one environment that need to talk to applications in another environment, but they don’t want to send that data directly over the internet.
I don’t blame them— enterprises want to minimize their internet exposure as much as possible, hiding internal apps away from the internet.
Traditionally, organizations have leaned on dedicated connection (or cloud-native) services like AWS Direct Connect or Azure ExpressRoute to connect applications in the public cloud to the private data center. While these methods are high-speed options that facilitate connections between the public cloud and private data center, these connections are costly at scale, are not encrypted using IPsec, do not facilitate cloud-to-cloud connectivity, and require different configuration depending on the cloud environment.
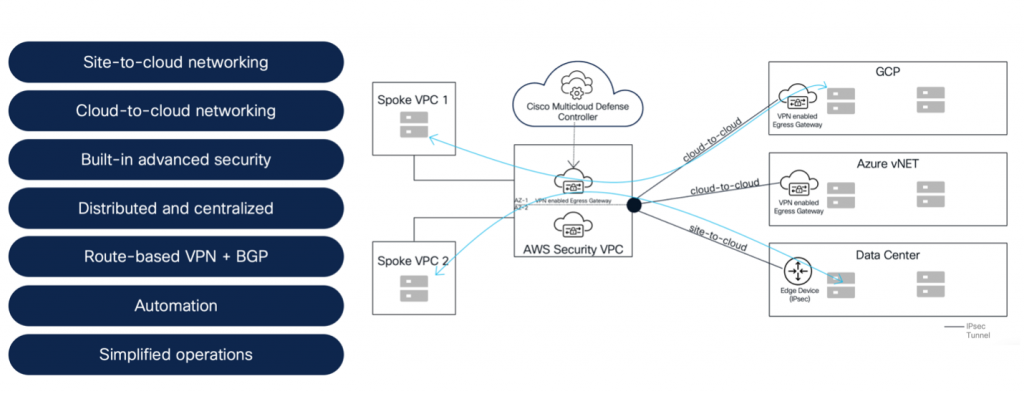
To solve these challenges, Cisco has released new multicloud networking capabilities enabling scalable, secure site-to-site and cloud-to-cloud connectivity. These features use Cisco VPN code on the Multicloud Defense Egress Gateway and BGP routing for better connectivity across your cloud environment.
Why Multicloud Networking?
Customers can leverage multicloud networking from Cisco to build highly secure connections between applications and environments using a simplified architecture and workflow. This means organizations can easily connect applications from one environment to another at scale while also keeping operations in house to reduce cost. Our multicloud networking capabilities use widely adopted route-based VPN and BGP routing for secure connections and automated network advertisements. These multicloud networking capabilities can be described as:
- Site-to-cloud networking: Secure connectivity between the data center and the cloud
- Cloud-to-cloud networking: Secure connectivity between clouds
A Closer Look
To build site-to-cloud and cloud-to-cloud connections, customers would leverage Cisco Defense Orchestrator for establishing fully orchestrated and automated IPsec tunnels between environments. The platform uses BGP for optimized, resilient routing, allowing for the secure connection between the data center and the cloud (site-to-cloud) and between clouds (cloud-to-cloud).
When building a site-to-cloud connection, customers would use Cisco Secure Firewall (either physical or virtual appliance) at the data center edge and a Multicloud Defense Gateway at the cloud edge for the beginning and the end of the connection. For multicloud deployments that require cloud-to-cloud connectivity, multiple Multicloud Defense Gateways would be used. Site-to-site and cloud-to-cloud networking capabilities can be supported in both centralized and distributed security models.
The Multicloud Defense Gateway is based on a single-pass architecture and includes VPN code embedded in the data path pipeline. This enables direct termination of route-based IPsec VPN on the egress gateway. Route-based VPN is used with BGP routing for an automated CIDR advertisement. As soon as the IPsec tunnel is terminated on the egress gateway it advertises and learns all the networks using BGP, enabling automated traffic steering.
Site-to-cloud Networking
Cisco Multicloud Defense and Cisco Defense Orchestrator provide an automated way to build highly secure, full-automated VPN tunnels between data centers and cloud environments.

Figure 3 shows that on-premises Secure Firewall appliances (physical or virtual) are managed by Cisco Defense Orchestrator and the Multicloud Defense egress gateways are managed by the Multicloud Defense Controller.
Cisco Defense Orchestrator orchestrates VPN configuration on the on-premises firewalls as well as talks to the Cisco Multicloud Defense Controller using APIs. This API communication between Cisco Defense Orchestrator and the Multicloud Defense Controller enables the orchestration of VPN configuration on the Multicloud Defense egress gateway(s). This approach provides customers with fully orchestrated secure IPsec connections, enabling secure connectivity between the data center and the cloud.
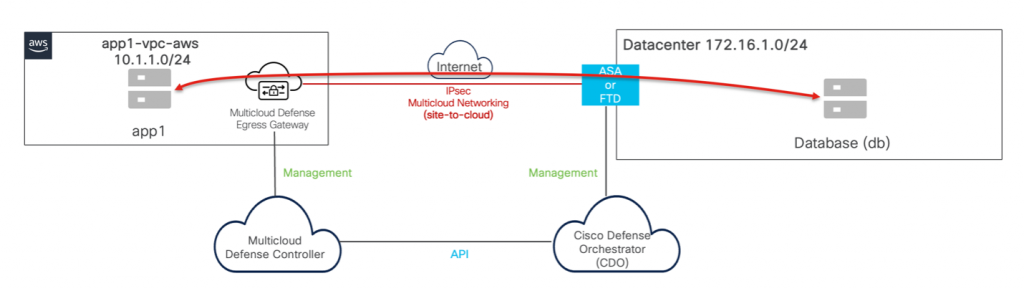
Figure 4 shows how Cisco also supports site-to-cloud networking in a distributed security model using Cisco Defense Orchestrator, Secure Firewall, the Multicloud Defense Controller, and the Multicloud Defense egress gateway.
Cloud-to-cloud Networking
Cisco Multicloud Defense provides an automated way to build highly secure, full-automated VPN tunnels between cloud environments. IPsec tunnels are terminated on the Multicloud Defense egress gateways.

Figure 5 shows the application VPC in AWS and the application VNet in Azure are protected using an egress gateway in the centralized deployment model. The Cisco Multicloud Defense Controller orchestrates IPsec VPN between egress gateways in Azure and AWS.

Figure 6 shows how Cisco also supports cloud-to-cloud networking in a distributed security model using Cisco Defense Orchestrator, the Multicloud Defense Controller, and multiple Multicloud Defense egress gateways.
The new multicloud networking capabilities add fully orchestrated VPN tunnels where IPsec tunnels are formed between networks advertised in the BGP domain. In addition to secure connectivity, customers need a way to enable threat-centric policies between source and destination subnets. To solve this challenge, Cisco is enabling common security objects across on-premises Cisco firewalls and Multicloud Defense Gateways with the new Hybrid Segmentation feature.
Hybrid Segmentation
For the site-to-cloud connectivity use case, sharing network objects between Secure Firewall, Multicloud Defense, and Cisco Defense Orchestrator simplifies the hybrid segmentation policy creation process for administrators by pooling objects across into one centralized location. This reduces complexity, minimizes human error when creating new objects, and removes duplicative processes.
Static object sharing
Now static network objects can be shared between Cisco Multicloud Defense and the Cisco Defense Orchestrator.
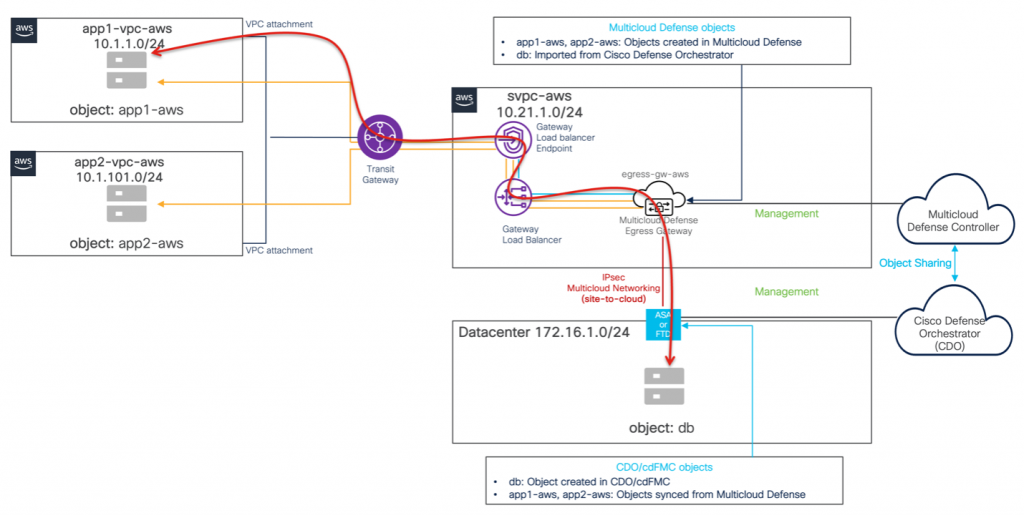
Figure 7 shows objects being shared between CDO and Multicloud Defense controller. Object “db” is imported from the CDO and objects “app1-aws” & “app2-aws” are automatically synchronized from the Cisco Multicloud Cloud Defense Controller.
Now administrator can configure the following policies in CDO and the Multicloud Defense Controller:
- Policy on CDO and Multicloud Defense Controller: Allow app1-aws, app2-aws access to db
In addition, to secure VPN connectivity features advanced threat security features can also be enabled on Multicloud Defense Egress Gateway.
Conclusion
Modern enterprises are becoming an increasingly complex spiderweb of connections between on-premises datacenters, branch locations, cloud VPCs, cloud regions, and cloud accounts. The traditional approach of doing direct connections between all the networks, or manually managing IPsec connectivity adds a lot of complexity. Cisco has brought together Cisco Defense Orchestrator, Secure Firewall, and Multicloud Defense to manage creating the connectivity across all the environments—ensuring applications can reach the destinations they require. Through these capabilities, customers achieve greater control while reducing cost by bringing operations in-house. In addition to building secure connections, these solutions together also simplify policy creation for customers by way of network object sharing between environments—reducing risk of human error when building policy and minimizing complexity across environments.
If you would like to learn more about how Cisco is driving further innovation across Cisco Defense Orchestrator, Secure Firewall, and Multicloud Defense, be sure to stop by the Innovation Zone at Cisco Live US 2024 or reach out to your Cisco sales representative!
Additional resources:
Cisco Blog on Multicloud Defense Architecture
Cisco Multicloud Defense Whitepaper
Cisco Multicloud Defense Website
See how Cisco is leveraging Cisco Defense Orchestrator, Multicloud Defense, and Secure Firewall to securely connect apps from site to cloud and between clouds.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Security on social!
Cisco Security Social Channels
Instagram
Facebook
Twitter
LinkedIn
Share:

