For cybercriminal mischief, it’s dark web vs deep web

Threat actors are consolidating their use of encrypted messaging platforms, initial access brokers and generative AI models, according to security firm Cybersixgill’s new report, The State of the Cybercrime Underground 2023. This report notes this is lowering the barriers to entry into cybercrime and “streamlining the weaponization and execution of ransomware attacks.”
The study is built upon 10 million posts on encrypted platforms and other kinds of data dredged up from the deep, dark and clear web. Brad Liggett, director of threat intel, North America, at Cybersixgill, defined those terms:
- Clear web: Any site that is accessible via a regular browser and not needing special encryption to access (e.g., CNN.com, ESPN.com, WhiteHouse.gov).
- Deep web: Sites that are unindexed by search engines, or sites that are gated and have restricted access.
- Dark web: Sites that are only accessible using encrypted tunneling protocols such as Tor (the onion router browser), ZeroNet and I2P.
“What we’re collecting in the channels across these platforms are messages,” he said. “Much like if you are in a group text with friends/family, these channels are live chat groups.”
Tor is popular among malefactors for the same reason: It gives people trapped in repressive regimes a way to get information to the outside world, said Daniel Thanos, vice president and head of Arctic Wolf Labs.
“Because it’s a federated, peer-to-peer routing system, fully encrypted, you can have hidden websites, and unless you know the address, you’re not going to get access,” he said. “And the way it’s routed, it’s virtually impossible to track someone.”
Jump to:
After massive increase in messaging by cybercriminals, slight drop last year
Cybercriminals use encrypted messaging platforms to collaborate, communicate and trade tools, stolen data and services partly because they offer automated functionalities that make them an ideal launchpad for cyberattacks. However, the Cybersixgill study suggests the number of threat actors is decreasing and concentrating on a handful of platforms.
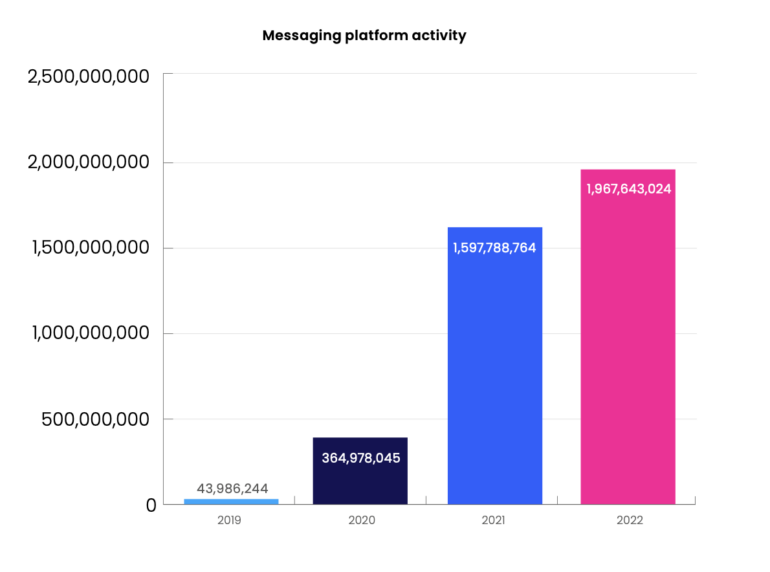
Between 2019 and 2020, data that Cybersixgill collected reflected a massive surge in use of encrypted messaging platforms, with the total number of collected items increasing by 730%. In the firm’s 2020-2021 analysis, this number increased by 338%, and then just 23% in 2022 to some 1.9 billion items collected from messaging platforms (Figure A).
Figure A
“When considering workflow activity, it’s quicker and easier to browse through channels on the messaging platforms rather than needing to log in to various forums, and read through posts, etc.,” said Liggett.
From the dark to deep web: Fewer onions, more apps
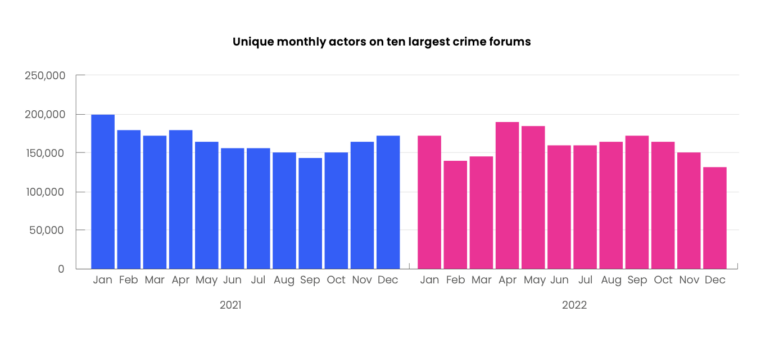
Across the dark web onion sites, the total number of forum posts and replies decreased by 13% between 2021 and 2022, dropping from over 91.7 million to around 79.1 million. The number of threat actors actively participating in top forums also declined slightly, according to the report.
The 10 largest cybercrime forums averaged 165,390 monthly users in 2021, which dropped by 4% to 158,813 in 2022. However, posts on those 10 sites grew by nearly 28%, meaning the forums’ participants became more active.
The study said that, in the past, most threat actors conducted their operations on the dark web alone, while in recent years there’s been migration to deep-web encrypted messaging platforms.
Ease of use favors deep web platforms
Cybercriminals favor deep web platforms because of their relative ease of use versus Tor, which requires more technical skills. “Across easily-accessible platforms, chats and channels, threat actors collaborate and communicate, trading tools, stolen data and services in an illicit network that operates in parallel to its dark web equivalent,” said the study.
“People tend to communicate in real-time across these platforms,” said Liggett. “Forums and marketplaces in the dark web are notorious for not always having a high level of uptime. They sometimes end up going offline after a period of time, or as we’ve seen recently have been seized by law enforcement and government agencies,” he said, noting that one such platform, RaidForums, was taken down in 2022, and BreachedForums just a couple weeks ago (Figure B).
Figure B
Cybercriminals congregate at these deep web channels
Liggett said Telegram is the most popular messaging platform for threat actors. Others, he said, include:
- Discord is a messaging platform favored by gamers.
- ICQ was first introduced in the 1990s and purchased by a Russian company in 2010.
- QQ is a popular communication platform in China.
- Wickr is a New York-based unit of Amazon Web Services.
- Signal is a free and open source, encrypted service.
- Tox is also a FOSS, peer-to-peer system.
Initial access brokers are booming business
The ecosystem of initial access brokers has grown, along with dark markets like Genesis Market, which was seized and shut down by the FBI in a multinational sting operation. These hubs facilitate transactions between IABs and threat actors seeking credentials, tokens, compromised endpoints, corporate logins, web shells, cPanels or other filched access points to enterprise networks.
The study pointed to two broad market categories of access-for-sale on the cybercriminal underground:
- IABs auctioning access to enterprise networks for hundreds to thousands of dollars.
- Wholesale access markets selling access to compromised endpoints for around $10.
Over 4.5 million access vectors were sold in 2021, followed by 10.3 million in a single market in 2022, the study revealed.
Thanos said IABs discern which credentials will work in a certain environment, and then they sell them in blocks.
“They say to the ransomware operators, ‘Look, we have access to organization X, Y and Z, and we think they will pay between X and Y dollars.’ And they know this because they also do reconnaissance, so they know the business – they know the expected payout for a ransomware attack,” he explained. “And all they do is provide the credentials and take a cut.”
What they provide could be passwords, API keys, tokens, Thanos said, “Or anything that is going to grant you the access. Sometimes it’s just that they know that there’s a certain vulnerability in the environment, and they sell that.”
Poor digital hygiene gives threat actors access to larger payouts
Thanos pointed out that a lot of credentials sold on the dark web, while from individual consumer accounts, can constitute access points to organizations thanks to poor digital hygiene: People using the same login information for enterprises as they do for personal accounts, allowing entry and lateral movement through organizations.
“They are often using the same passwords for their corporate access, so unfortunately, the personal and the enterprise worlds are intertwined. Bad guys then go out to social media – Linkedin, for example – to get names, and then apply automation to match names to IDs and then try the stolen password.”
Often this is done by credential stuffing where combolists, which are combined text files of leaked usernames and passwords, obtained from previous breaches are used to take over accounts on other web or mobile applications through brute force attacks.

