- The augmented IT team: How AI is reshaping IT roles and skills for the future
- This beastly 500W charger replaced every other charger I had - with six ports to boot
- XDR still means so much more than some may realize
- How Cisco Supports Balancing Fatherhood and a Cybersecurity Career
- Will your old laptop still get security updates after this year? Check this chart
Fraudsters Are Using Google Forms to Evade Email Filters
Business Email Compromise (BEC)
,
Cybercrime as-a-service
,
Fraud Management & Cybercrime
Emails Are Likely a Reconnaissance Mission for Future Email Compromise
Fraudsters are using Google Forms to target retail, telecom, healthcare, energy and manufacturing companies in an apparent reconnaissance campaign to identify targets for follow-up business email compromise attack.
See Also: Rapid Digitization and Risk: A Roundtable Preview
“Unfortunately, Google services are often abused for malware distribution, credential phishing and, in this case, as part of email fraud. Google is often a trusted source in many organizations, so threat actors leverage that goodwill for their attacks,” says Sherrod DeGrippo, senior director of threat research and detection at Proofpoint.
Researchers at Proofpoint note that the attackers are leveraging Google Forms to bypass email security content filters based on keywords.
“This hybrid campaign combines the benefits of scale and legitimacy by leveraging Google services with social engineering attacks, more commonly associated with BEC. We observed thousands of messages predominantly delivered to retail, telecommunications, healthcare, energy, and manufacturing sectors,” the researchers say.
Proofpoint initially spotted the attackers using Google Forms in early December 2020, however, this tactic is not new and is routinely observed in credential phishing campaigns. Using Google Forms lets actors compose and send emails to evade ingress and egress email filters.
“We have observed the use of Google Forms in the past; however, they are usually employed by phishing emails. It’s less common in a BEC lure,” DeGrippo says.
Attack Techniques
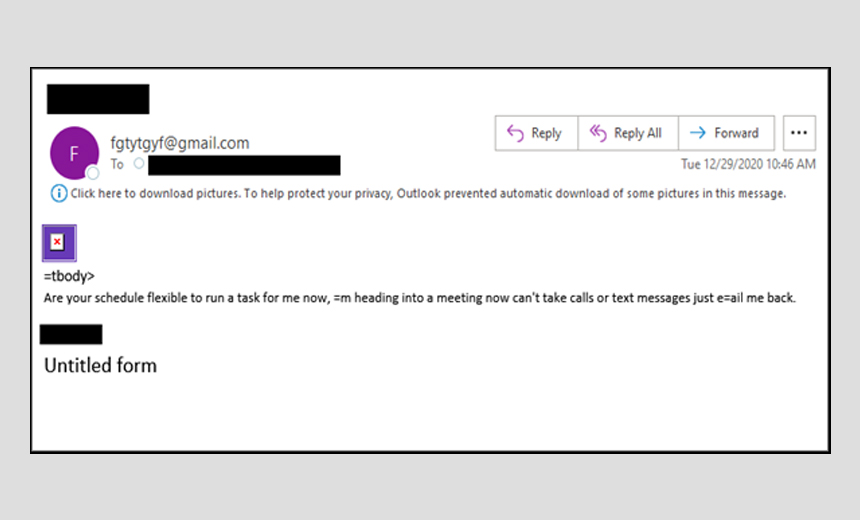
Proofpoint reports that the emails convey a sense of urgency, and the subjects are unique names of C-level executives from a specific target organization, with no attempt made to use display-name spoofing.
“They demand a ‘Quick Task’ from the user in response to the actor who claims to be heading into a meeting or too preoccupied to handle the task themselves. The actor politely asks the user if they ‘have a moment,’ a common opener in gift card fraud,” Proofpoint notes.
Once a victim clicks on the links in the email, it leads to a default, untitled form hosted on Google Forms’ infrastructure. Researchers note that the primary goal of an attacker is to elicit a reply from the victim, under the pretext that the survey is broken or not what they expected.
“As a secondary goal, the form likely serves as a sensor to simply see if anyone fills out their form, functioning as a reconnaissance technique to weed out users who may be susceptible to clicking a suspicious link found in an email,” the researchers say.
They say that these messages are a threat because either responding to or completing the benign form may lead to follow-on actions aimed at a more receptive audience.
Given the C-suite spoofing, researchers expect that this is an email reconnaissance campaign designed to enable target selection for a follow-on threat activity.
“The tone of urgency in the emails is consistent with previous BEC actors, and therefore, we want to ensure security awareness of these attempts as an indication or warning to customers and the security community,” say the researchers.
Social engineering is pervasive throughout email-borne attacks. However, it is employed differently in malware and credential phishing than in BEC campaigns.
“In a malware campaign, social engineering is used in the initial email. Conversely, in BEC, social engineering is used throughout the lifecycle of the fraud. Although it is rare to observe actors delivering malware after the exchange of benign messages,” say researchers.
Other BEC Scams
Last week, in another report, Proofpoint tracked several fraud schemes leveraging COVID-19 vaccine-themed emails.
These include business email compromise scams, messages with malicious attachments used to deliver malware and phishing emails designed to harvest credentials – including usernames and passwords for Microsoft Office 365 (see: COVID-19 Vaccine Themes Persist in Fraud Schemes).
The Proofpoint report notes social engineering attacks leveraging vaccine themes have increased over the last two months as pharmaceutical companies have ramped up production (see: COVID-19 Vaccine Documents, Personal Data Leaked).
In December 2020, Proofpoint tracked a large-scale BEC scheme that attempted to use COVID-19 vaccine news and rumors of a possible merger or acquisition as a way to target executives, including those with titles such as vice president, general manager and managing director.

