- Learn with Cisco at Cisco Live 2025 in San Diego
- This Eufy robot vacuum has a built-in handheld vac - and just hit its lowest price
- I highly recommend this Lenovo laptop, and it's nearly 50% off
- Disney+ and Hulu now offer prizes, freebies, and other perks to keep you subscribed
- This new YouTube Shorts feature lets you circle to search videos more easily
IBM X-Force Report: Grandoreiro Malware Targets More Than 1,500 Banks in 60 Countries
A new report from IBM X-Force exposes changes in the Grandoreiro malware landscape. The banking trojan is now capable of targeting more than 1,500 global banks in more than 60 countries, and it has been updated with new features.
Also, Grandoreiro’s targeting has become wider, as it initially only targeted Spanish-speaking countries, while recent attack campaigns targeted countries in Europe, Asia and Africa. In addition, the malware is now sending phishing emails directly from the victim’s Microsoft Outlook local client to recipients’ email addresses found in the local system.
What is Grandoreiro?
According to Interpol, the Grandoreiro banking trojan has been a major threat across Spanish-speaking countries since 2017. The malware’s main functionalities allow cybercriminals to control devices on the infected computer, enable keylogging, handle windows and processes, open a browser and execute JavaScript inside it, upload or download files, and send emails, in addition to its banking trojan capabilities.
Analysis of different attack campaigns reveals that many operators are involved in Grandoreiro attacks, as stated by cybersecurity company Kaspersky, which wrote in July 2020, “It is still not possible to link this malware to any specific cybercrime group, although it is clear that the campaign is using a MaaS (Malware-as-a-Service) business model.”
SEE: Kaspersky Study: Devices Infected With Data-Stealing Malware Increased by 7 Times Since 2020
Arrests of suspected cybercriminals in relation to Grandoreiro happened in 2021, with 16 suspects being caught by the Spanish Police on charges of laundering funds stolen through two banking trojans, including Grandoreiro. More recently, Brazilian authorities arrested five programmers and administrators behind the banking malware, who were suspected to have defrauded victims of more than €3.5 million.
Yet the malware, developed in Brazil, is still active and has started expanding its target list to other countries, such as Japan, Netherlands, Italy and South Africa, as reported in the new research from IBM’s X-Force team.
How do Grandoreiro campaigns work?
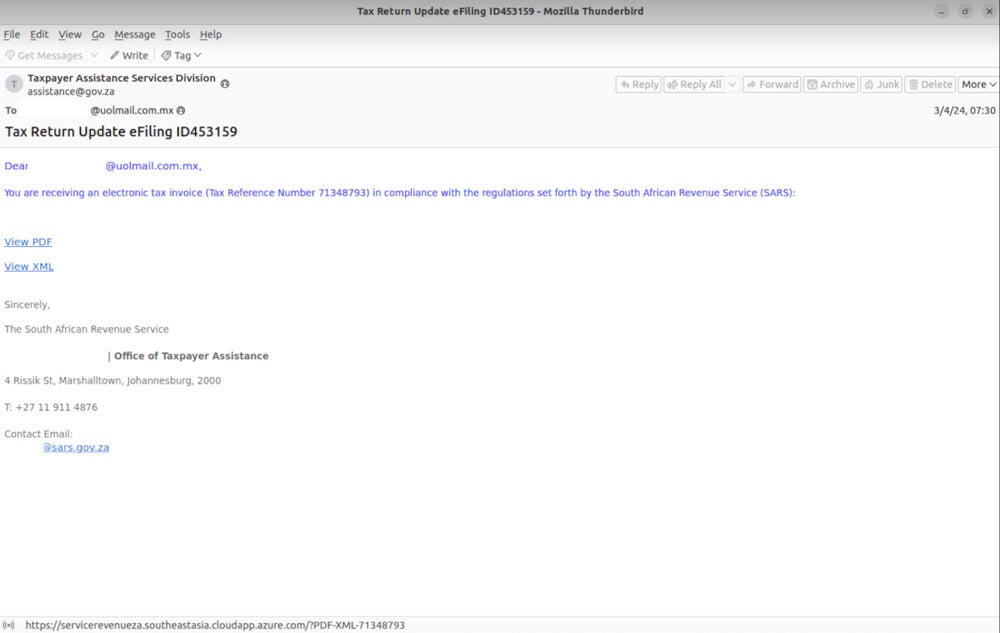
All Grandoreiro campaigns start with phishing emails
Since March 2024, several Grandoreiro phishing campaigns have impersonated entities in Mexico, such as Mexico’s Tax Administration Service, Mexico’s Federal Electricity Commission or the Revenue Service of Argentina.
Different social engineering techniques have been used since March 2024 in the emails to entice the user to click a link: a final notice to pay a debt, a reminder that one can access their account statement in PDF or XML format or a reminder to read details on a compliance notice.
In those phishing campaigns, only users originating from specific countries — Mexico, Chile, Spain, Costa Rica, Peru, Argentina — are being redirected to a payload when clicking on the link provided in the email.
Following the recent arrests involving Grandoreiro operators, researchers observed a surge in campaigns targeting countries beyond the usual Spanish-speaking ones, including Japan, the Netherlands, Italy and South Africa, with emails written in English.
Next comes the infection chain
After the user clicks the malicious link in the phishing email, a custom loader is launched, presenting a fake Adobe PDF Reader captcha, which requires a click to continue with the execution, probably to distinguish between real users and automated systems such as sandboxes.
Then, the loader collects some victim data and sends it to the command&control server using encryption based on AES and base64 algorithms. The data sent to the C2 consists of the computer and user names, the operating system version, the antivirus name, the victim’s public IP address, and a list of running processes. In addition, the loader checks for the existence of the Microsoft Outlook client as well as crypto wallets and special banking security products such as IBM Trusteer or Topaz OFD.
The loader can be configured to disallow victims from specific countries based on their IP addresses. One malware sample found by IBM X-Force stopped if the user was located in Russia, Czech Republic, Poland or Netherlands.
If all conditions are met, the Grandoreiro banking trojan is downloaded, decrypted via an RC4-based algorithm and executed.
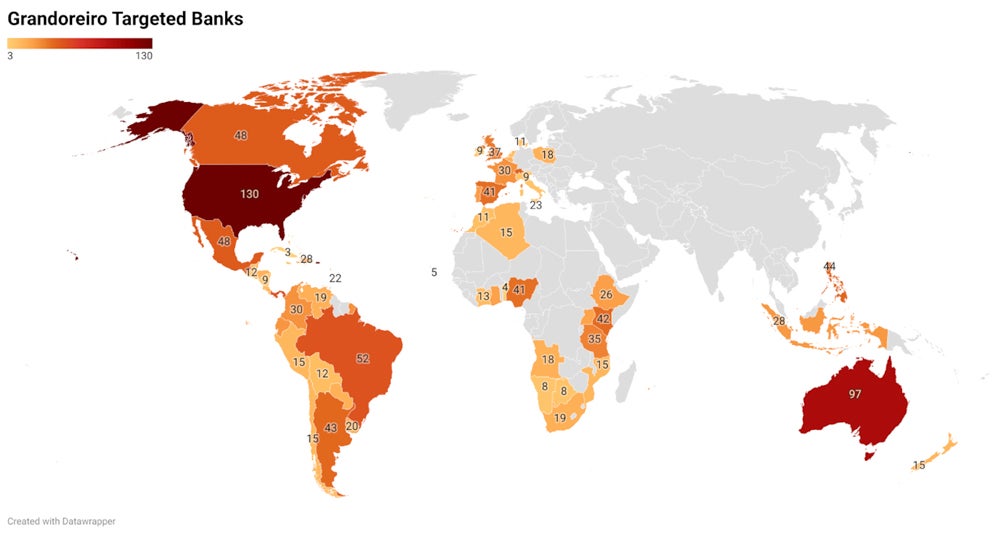
Targeting more than 1,500 banks worldwide
Grandoreiro’s list of targeted applications has increased to more than 1,500 banks worldwide, according to IBM X-Force, with bank applications also tied to regions. For example, if the victim’s country is identified as Belgium, the malware will search for all targeted banking applications associated with the European region.
In addition, 266 unique strings are used by the malware to identify cryptocurrency wallets.
Recent updates in Grandoreiro
New DGA algorithm
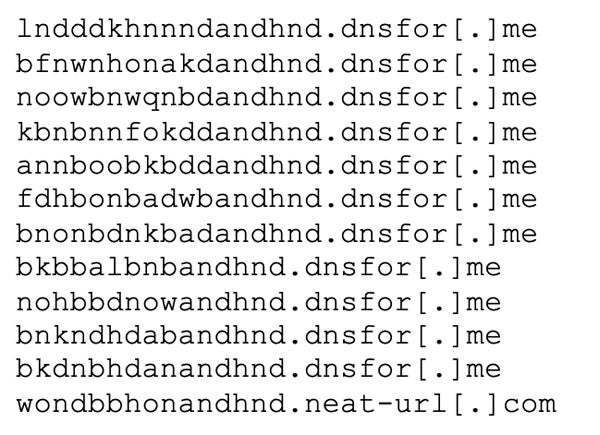
Researchers Golo Mühr and Melissa Frydrych analyzed the malware in depth and found the malware, which traditionally relied on domain generation algorithms to find its C2 server references, contained a reworked DGA.
The new algorithm introduces multiple seeds for its DGA, “used to calculate a different domain for each mode or functionality of the banking trojan, allowing separation of C2 tasks among several operators as part of their Malware-as-a-Service operation” as stated by the researchers.
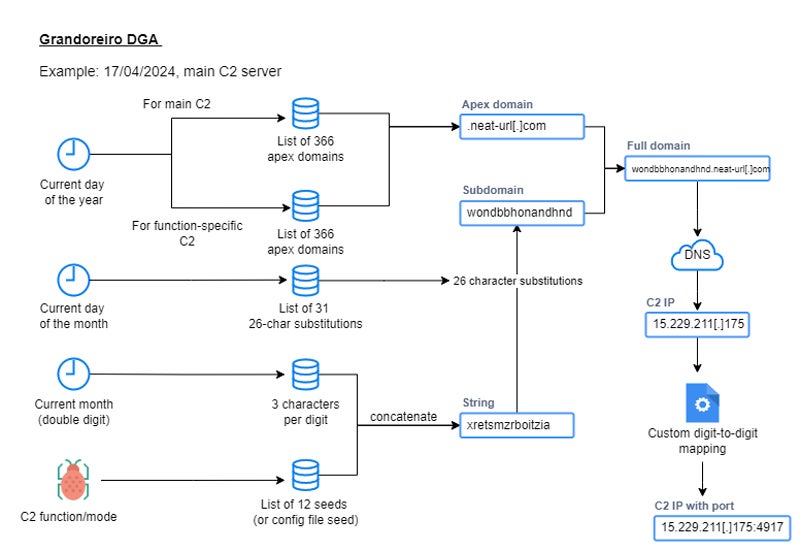
For one analyzed sample, for a given day, 12 domains could be used as C2 domains, with four of them being active on that day and leading to Brazilian-based IP addresses.
Microsoft Outlook abuse
Recent versions of Grandoreiro abuse the local Microsoft Outlook software when available on an infected computer.
The malware interacts with the Outlook Security Manager Tool, a tool designed to develop Outlook add-ins. The use of the tool allows the malware to disable alerts within Outlook before it starts harvesting all sender email addresses found in the victim’s mailbox, filtering the email addresses to avoid collecting unwanted ones such as those containing “noreply,” “feedback” or “newsletter,” to name a few from the malware’s blocklist.
In addition, the malware scans parts of the victim’s folders recursively to hunt for more email addresses, looking for files with specific extensions, including .csv, .txt, .xls and .doc.
The malware then starts sending spam based on phishing templates it received from its C2 server before deleting all the sent emails from the victim’s mailbox.
In order to avoid being caught by the user who could notice suspicious behavior from the computer, the malware only starts sending the emails when the last input on the machine is at least five minutes old or longer in some malware variants.
How to protect from this Grandoreiro malware threat
- Do careful network analysis. In particular, multiple consecutive requests to ip-api.com/json must trigger alerts and investigations, as it might be an indicator of a Grandoreiro infection.
- Monitor run keys in the Windows registry. Any addition outside of a normal software installation should be investigated closely to detect malware activity.
- Block pre-calculated DGA domains via DNS.
- Deploy endpoint security software on every computer to detect malware.
- Educate users and staff to detect phishing emails and potential fraud attempts.
- Keep all hardware and software up to date and patched in order not to be infected via a common vulnerability.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.

