- I recommend the Pixel 9 to most people looking to upgrade - especially while it's $250 off
- Google's viral research assistant just got its own app - here's how it can help you
- Sony will give you a free 55-inch 4K TV right now - but this is the last day to qualify
- I've used virtually every Linux distro, but this one has a fresh perspective
- The 7 gadgets I never travel without (and why they make such a big difference)
LogRhythm vs. SolarWinds (2023): SIEM Tool Comparison
This is an in-depth LogRhythm vs. SolarWinds SIEM tool comparison, covering their key features, pricing, and more. Use this guide to find your best fit.
LogRhythm NextGen SIEM and SolarWinds Security Events Manager both provide security information and event management tools to users who wish to ensure the security of their organizational networks and digital devices. While both products provide security information and event management capabilities, LogRhythm’s more dynamic customization capabilities are for mature companies with deep security needs and a dedicated security operations center team. SolarWinds also offers a powerful solution, but is more accessible for smaller teams or those looking for ease of reporting.
Jump to:
LogRhythm vs. SolarWinds: Comparison table
| Features | LogRhythm | SolarWinds |
|---|---|---|
| Pricing | Contact vendor | Starts at $2,877 |
| Real-time monitoring | Yes | Yes |
| Logging | Yes | Yes |
| Analytics | Yes | Yes |
| Reporting | Yes | Yes |
| Threat management | Yes | Yes |
| Incident response | Yes | Yes |
| Customization | Yes | Yes |
| Visit LogRhythm | Visit SolarWinds |
LogRhythm and SolarWinds: Pricing
LogRhythm offers perpetual licensing and subscription-based pricing plans. The licensing allows unlimited users and log sources, and can be run via the cloud, hardware and virtual machines. To get an exact quote on pricing, contact LogRhythm.
SolarWinds pricing starts at $2,877, with an option to get a custom pricing plan. Users can choose from the perpetual licensing option, which allows for indefinite use of the license, or the subscription-based model. While the cost of subscription-based licensing is initially far less than the cost of purchasing the perpetual license, the long-term cost is higher.
LogRhythm vs. SolarWinds: Feature comparison
Threat monitoring
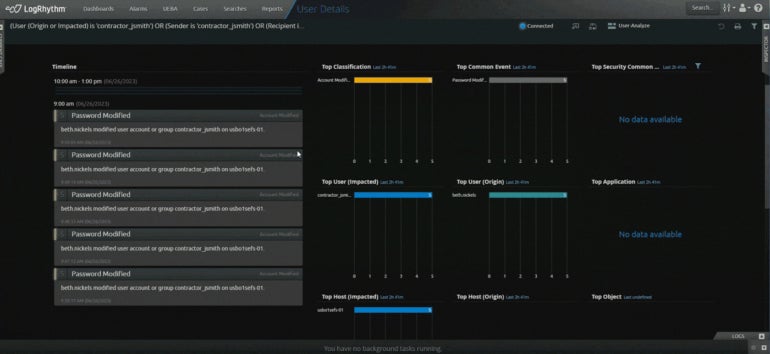
LogRhythm monitors the data and events of organizations to detect anomalies throughout their networks and endpoints. The system collects security data, log data and flow data to provide holistic real-time visibility and effective threat detection. The risk-based monitoring eliminates blind spots and identifies threats quickly, so users can respond to them before they cause severe damage. LogRhythm’s Endpoint Threat Detection Module uses threat intelligence, machine learning, and behavior analytics to find potential threats (Figure A). Methods for threat detection include identifying abnormal communication patterns, lateral movement and changes to sensitive files.
Figure A
The SolarWinds SIEM solution provides continuous threat detection and real-time monitoring across users’ devices, services, files and folders with its on-premises and multicloud deployments. Its intuitive dashboard and user interface make it easy for users to navigate the tool’s features. The centralized repository collects log data with the SIEM log collector tool, and raw network log data is organized and normalized for users in the system. Additionally, the tool’s event-time correlation and advanced search capabilities are beneficial when conducting forensic analysis and security investigation.
Threat analytics
The LogRhythm NextGen SIEM platform uses multidimensional analytics to detect and stop security threats. Data collected by the system is normalized and correlated to identify potentially dangerous activity, which provides more accuracy. Network traffic and packet data are also analyzed for patterns and behavioral outliers. The behavioral analysis features can process users’ activity within a network and identify deviations (Figure B) from normal baseline behavior. This is made possible through machine learning and can help ensure security from insider access abuse and data exfiltration. Additionally, the system allows for both contextual and unstructured searches.
Figure B
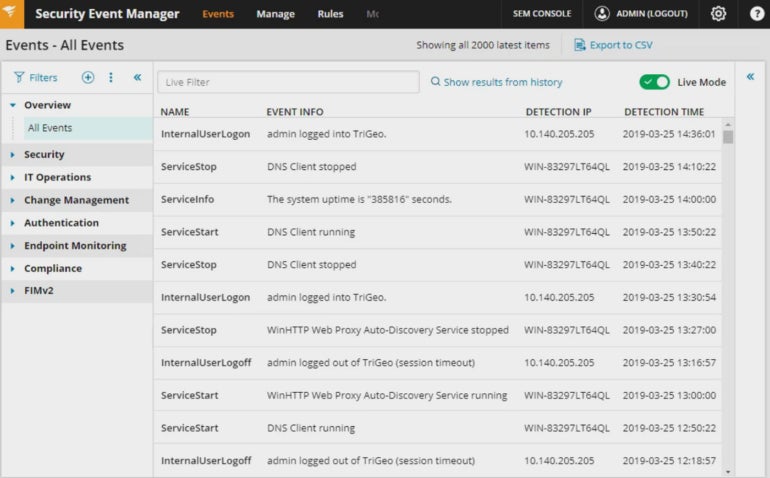
SolarWinds processes data and events for signs of security threats. The event log analyzer collects and analyzes log data, providing users insight with real-time visibility and context (Figure C). Events are also monitored to identify suspicious activity, such as permission changes and data modification. This data is then correlated through built-in and custom event correlation rules. The insights gained from these features can be beneficial in helping users and network administrators diagnose system vulnerabilities, troubleshoot network problems and improve their resource management.
Figure C
Notifications
When a threat is detected, the LogRhythm SIEM platform notifies its users based on their settings and the severity of the event. The Alarming and Response Manager can send notifications to users when threats are detected or alert them of suspicious activity. The LogRhythm DetectX solution uses analytics to determine the prioritization of threats based on their severity level. The security analytics can be customized, or entirely developed by users, to ensure that they’re notified per their needs. In addition, users can integrate their tools with open source or STIX/TAXII-compliant providers for even more alert precision.
SEE: Cyber threat intelligence software: How to choose the right CTI tools for your business (TechRepublic)
SolarWinds lets users set custom alerts or view SEM alert feeds, so they are always aware of security threats. Users can manage their systems to provide threshold-based alarms and notifications for security system event stream triggers, system errors, IDS/IPS systems with infection symptoms, crash reports, etc. Their Fine-tune File Integrity Monitoring filters can be adjusted to ensure that only high-priority, file-related events create reports. When security events occur or threats are identified, SolarWinds Log & Event Manager can send users notifications via email.
Automation and response
LogRhythm monitors organizational data and events for suspicious activity and takes actions to minimize the impact with its automated response features. Its embedded solution, RespondX, can coordinate these response actions into repeatable processes to manage events quickly and efficiently. Users can gain complete visibility into threats and concerns, as the tool has preconfigured modules and reports providing all of the information they need to respond appropriately. Additionally, the platform offers playbooks for streamlining operational workflows.
SEE: Cybersecurity incident response: Lessons learned from 2021 (TechRepublic)
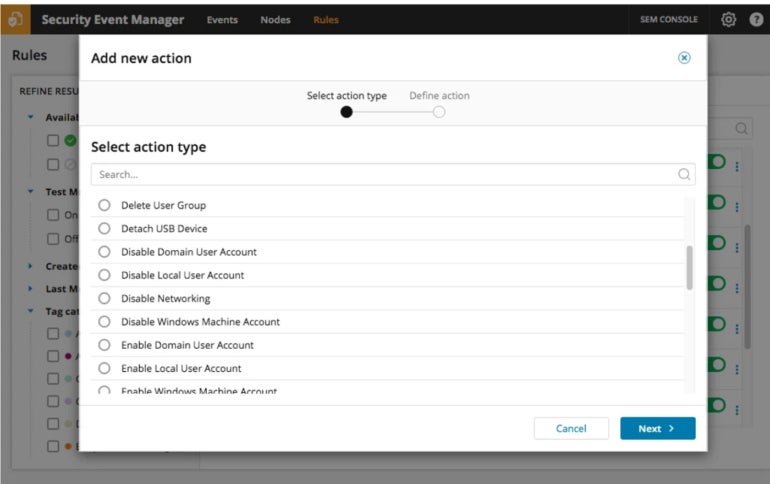
Once the SolarWinds SIEM tool identifies security incidents and threats that require action, it can respond in various ways. Through automation, users can set customized responses to flagged security events or suspicious activity. This can include blocking or quarantining infected devices, killing processes, restarting servers, logging off users and even disabling an agent’s access to the network. In addition, Active Response (Figure D) lets users mitigate risks with either customizable or preconfigured settings for a more hands-off experience. However, users can also decide to set their notification options to be alerted of the events they deem significant.
Figure D
LogRhythm pros and cons
Highlighted below are some of the pros and cons of LogRhythm.
Pros
- Allows users to match their security and IT operations with established security frameworks such as MITRE ATT&CK and NIST.
- Simplifies the process of collecting and analyzing data from various sources through a centralized log management system.
- Offers User and Entity Behavior Analytics capabilities.
- Can automate repetitive tasks with its embedded security orchestration, automation and response capabilities.
- Supplements traditional log collection with endpoint monitoring.
- Uses Machine Data Intelligence capability to help users to contextualize and simplify complex data.
Cons
- Pricing information isn’t stated.
- The customization options might be narrow when compared to other tools.
SolarWinds Pros and Cons
Below are some advantages and drawbacks of using SolarWinds.
Pros
- Supports compliance reporting and audits for HIPAA, PCI DSS, SOX and more.
- Licensing cost is based on the number of log-emitting sources, not the log volume.
- Allows users to customize actions based on threat intelligence findings.
- Can send generated raw event log data in different formats such as CSV or by using syslog protocols.
- Offers a 30-day free trial.
Cons
- Limited AI and machine learning-enhanced capabilities.
- Limited information on pricing.
Should your organization use LogRhythm or SolarWinds?
LogRhythm offers a more robust SIEM solution with its advanced AI and machine learning-backed threat detection and response capabilities. The solution makes threat detection workflows easier as its SOAR feature is integrated into the dashboard. You should go for LogRhythm if your organization has complex security needs and operates a dedicated SOC team.
On the other hand, SolarWinds offers a more basic and user-friendly interface design. Although it can help you monitor and manage security events effectively and generate compliance reports, it might lack some of the advanced features and customization options found in LogRhythm. So, if your organization is looking for a simpler, user-friendly SIEM tool, SolarWinds could be an ideal option.
Methodology
We compared both SIEM solutions by carrying out a thorough evaluation of the features, capabilities and pricing information, as well as user feedback. Each vendor’s site served as our primary source of information. We took time to study the product datasheets, infographics and demo videos provided on the sites. User feedback from other reputable review sites such as Gartner Peer Insights also helped us to understand what users like and dislike about each product.
Our final verdict is that no SIEM tool can solve all your pain points. Therefore, it’s best to check your specific needs and requirements before making a final choice.

