- I tested a Pixel Tablet without any Google apps, and it's more private than even my iPad
- My search for the best MacBook docking station is over. This one can power it all
- This $500 Motorola proves you don't need to spend more on flagship phones
- Finally, budget wireless earbuds that I wouldn't mind putting my AirPods away for
- I replaced my Linux system with this $200 Windows mini PC - and it left me impressed
Microsoft warns of Volt Typhoon, latest salvo in global cyberwar

Microsoft’s warning on Wednesday that the China-sponsored actor Volt Typhoon attacked U.S. infrastructure put a hard emphasis on presentations by cybersecurity and international affairs experts that a global war in cyberspace is pitting authoritarian regimes against democracies.
Jump to:
China’s commitment to cyberwarfare
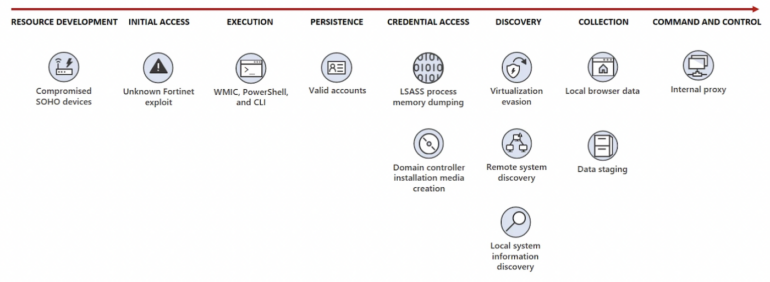
Microsoft’s notification pointed out that Volt Typhoon — which hit organizations in sectors spanning IT, communications, manufacturing, utility, transportation, construction, maritime, government and education — has been pursuing a “living off the land” strategy focused on data exfiltration since 2021. The tactic typically uses social engineering exploits like phishing to access networks invisibly by riding on legitimate software. It uses a Fortinet exploit to gain access and uses valid accounts to persist (Figure A).
Figure A
Nadir Izrael, the chief technology officer and co-founder of the Armis security firm, pointed out that China’s defense budget has been increasing over the years, reaching an estimated $178 billion in 2020. “This growing investment has enabled China to build up its cyber capabilities, with more than 50,000 cyber soldiers and an advanced cyberwarfare unit,” he said.
He added that China’s investment in offensive cyber capabilities has created “a global weapon in its arsenal to rattle critical infrastructure across nearly every sector — from communications to maritime — and interrupt U.S. citizens’ lives.” He said, “Cyberwarfare is an incredibly impactful, cost-effective tool for China to disrupt world order.”
According to Armis, he has been predicting these threats since January after finding that 33% of global organizations are not taking the threat of cyberwarfare threats seriously. He has been urging governments and businesses across sectors to start putting in place procedures to counteract these threats.
“As the world becomes increasingly digitized, cyberwarfare is modern warfare,” Armis said. “This has to be a wake-up call for the U.S. and western nations.”
At the WithSecure Sphere23 conference in Helsinki, Finland, before this security news had crossed the wires, Jessica Berlin, a Germany-based foreign policy analyst and founder of the consultancy CoStruct, said the U.S., the European Union and other democracies have not awakened to the implications of cyberwarfare by Russia, China and North Korea. She said these countries are engaged in a cybernetic world war — one that autocracies have the upper hand in because they have fully acknowledged and embraced it and have committed to waging it as such.
She told TechRepublic that tech and security companies could play a key role in awakening citizens and governments to this fact by being more transparent about attacks. She also noted the European Union’s General Data Protection Regulation, which has been in effect for five years, has been a powerful tool for oversight of digital information, data provenance and misinformation on social platforms.
Professionalization of cybercrime lowers bar to entry
Stephen Robinson, a senior threat intelligence analyst at WithSecure, said the cybercriminal ecosystem’s mirroring of legitimate business has made it easier for state actors and less sophisticated groups to buy what they can’t make. This professionalization of cybercrime has created a formal service sector. “They are outsourcing functions, hiring freelancers, subcontracting; criminal service providers have sprung up, and their existence is industrializing exploitation,” said Robinson.
The success of the criminal as-a-service model is expedited by such frameworks as Tor anonymous data transfer and cryptocurrency, noted Robinson, who delineated some dark web service verticals.
- Initial access brokers: These brokers are key because they thrive in the service-oriented model and are enablers. They use whatever method they can to gain access and then offer that access.
- Crypter as a service: Crypter is a tool to hide a malware payload. And this, said Robinson, has led to an arms race between malware and antimalware.
- Crypto jackers: These actors break into a network and drop software and are often one of the first actors to exploit a server vulnerability. They constitute a low threat yet are a very strong indicator that something has happened or will, according to Robinson.
- Malware-as-a-service: Highly technical and with advanced services like support and contracts and access to premium products.
- Nation state actors: Nation state actors use the above tools, which enable them to spin up campaigns and access new victims without being attributed.
WithSecure has a fresh report on multi-point extortion ransomware groups that employ several extortion strategies, including encryption, to pressure victims for payments.
The firm’s analysis of more than 3,000 data leaks by these groups showed that organizations in the U.S. were the most targeted victims, followed by Canada, the U.K., Germany, France and Australia.
In addition, the firm’s research showed that the construction industry accounted for 19% of the data leaks; the automotive industry accounted for only 6% of attacks.
“In pursuit of a bigger slice of the huge revenues of the ransomware industry, ransomware groups purchase capabilities from specialist e-crime suppliers in much the same way that legitimate businesses outsource functions to increase their profits,” said Robinson. “This ready supply of capabilities and information is being taken advantage of by more and more cyberthreat actors, ranging from lone, low-skilled operators right up to nation state APTs. Ransomware didn’t create the cybercrime industry, but it has really thrown fuel on the fire.”
The firm offered an example that resembled the mass looting of a department store after the door had been left ajar. One organization was victimized by five threat actors, each with different objectives and representing a different type of cybercrime service: the Monti ransomware group, Qakbot malware-as-a-service, the 8220 crypto-jacking gang, an unnamed initial access broker and a subset of Lazarus Group associated with North Korea.
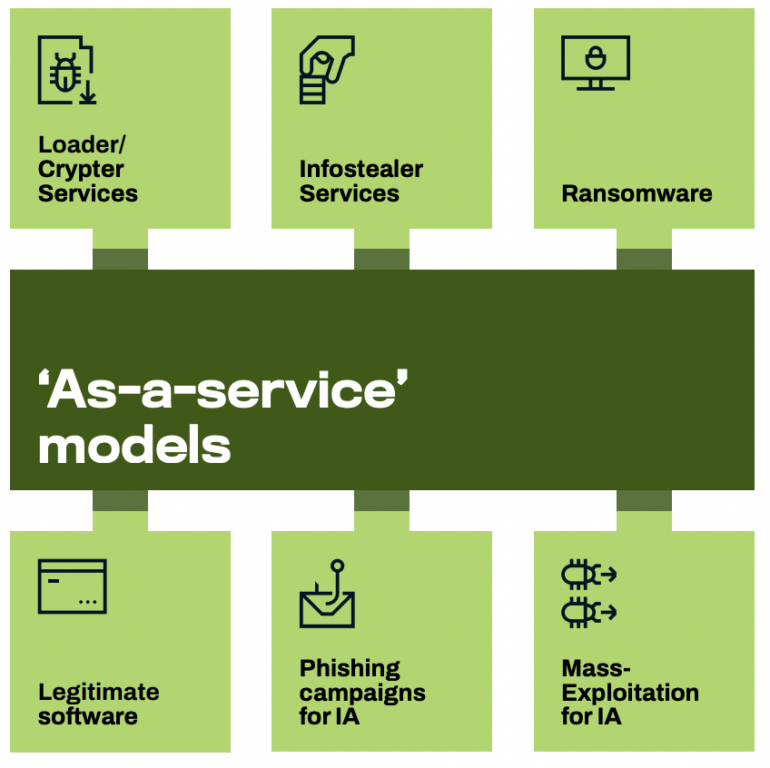
In these incidents, WithSecure threat intelligence reported encountering six distinct examples of the “as a service” model in use in the kill chains observed (Figure B).
Figure B
According to the report, this professionalization trend makes the expertise and resources to attack organizations accessible to lesser-skilled or poorly resourced threat actors. The report predicts it is likely the number of attackers and the size of the cybercrime industry will grow in the coming years.
How to mitigate Volt Typhoon
In Microsoft’s report about Volt Typhoon, the company said detecting an activity that uses normal sign-in channels and system binaries requires behavioral monitoring and remediation requires closing or changing credentials for compromised accounts. In these cases, Microsoft suggests that security operations teams should examine the activity of compromised accounts for any malicious actions or exposed data.
To preclude this variety of attacks, Microsoft suggested these tips:
- Enforce strong multifactor authentication policies by using hardware security keys, passwordless sign-in and password expiration rules and deactivating unused accounts.
- Turn on attack surface reduction rules to block or audit activities associated with this threat.
- Enable Protective Process Light for LSASS on Windows 11 devices. New enterprise-joined Windows 11 (22H2 update) installs have this feature enabled by default, per the company.
- Enable Windows Defender Credential Guard, which is turned on by default for organizations using the Enterprise edition of Windows 11.
- Turn on cloud-delivered protection in Microsoft Defender Antivirus.
- Run endpoint detection and response in block mode so Microsoft Defender for Endpoint can block malicious artifacts.

