- I tested a robot mower with no boundary wire for a month - here's my buying advice now
- US Tries to Claw Back $7m Taken by North Korean IT Workers
- The best AI for coding in 2025 (including a new winner - and what not to use)
- “통제 밖으로 번지는 생성형 AI··· CISO 대응 한계 드러나” 팔로알토네트웍스 조사
- 오디오에서 추론→음성 생성→실시간 소통···구글, “대화가 AI와 소통하는 핵심적인 방법될 것”
North Korean Hacking Group Targets Diplomats, Forgoes Malware
A North Korean cyber-operations group has increased its focus on cyber espionage and targeting diplomats and regional experts, using captured user credentials to fuel phishing attacks and only rarely using malware to persist in targeted organizations.
A new report by message-security firm Proofpoint, which focused on a single subgroup of what other security firms call Kimsuky, found that the North Korean group mainly targets individuals in the United States, Russia, and China, and usually attempts to quietly harvest credentials, siphon off information, and — like many attacks attributed to North Korea — turn compromises into financial gain.
The hacking group, which Proofpoint calls Threat Actor 406 (TA406), attempted to compromise high-level officials, law enforcement leaders, and experts in economics and finance in weekly attacks — a departure from lower-level attacks in past years.
In addition, prior to 2021, North Korean groups have not typically used national security issues as a lure, but that has changed, says Sherrod DeGrippo, vice president of threat research and detection at Proofpoint.
“The most notable aspects of TA406 are their flexibility in using any means for financial gain and their persistence in targeting the same individuals [and] organizations repeatedly,” she says. “Like with other state-aligned groups, those aligned with North Korea vary in their skillset and likely have ever-evolving objectives based on state interests.”
While cyber operations by China and Russia usually garner the most attention, experts have focused recently on activities by groups linked to Iran and North Korea. This week, the Cybersecurity and Infrastructure Security Agency (CISA) warned that attacks by Iran-linked groups are attempting to exploit known vulnerabilities in Fortinet network appliances and Microsoft’s Exchange server. North Korea’s well-known Lazarus Group has targeted supply chains, compromising a South Korean security-software vendor and a Latvian IT asset-management vendor.
More recently, North Korean has focused much of its efforts on espionage campaigns and targeting organizations for financial gain, with cryptocurrency a common target of attacks.
“In early 2021, TA406 began almost weekly campaigns featuring themes that included nuclear weapon safety, U.S. President Joe Biden, Korean foreign policy and other political themes,” the Proofpoint report stated. “The group attempted to collect credentials, such as Microsoft logins or other corporate credentials, from the targeted individuals. In some cases, the emails were benign in nature, [but] these messages may have been attempts by the attackers to engage with victims before sending them a malicious link or attachment.”
Three North Korean Groups
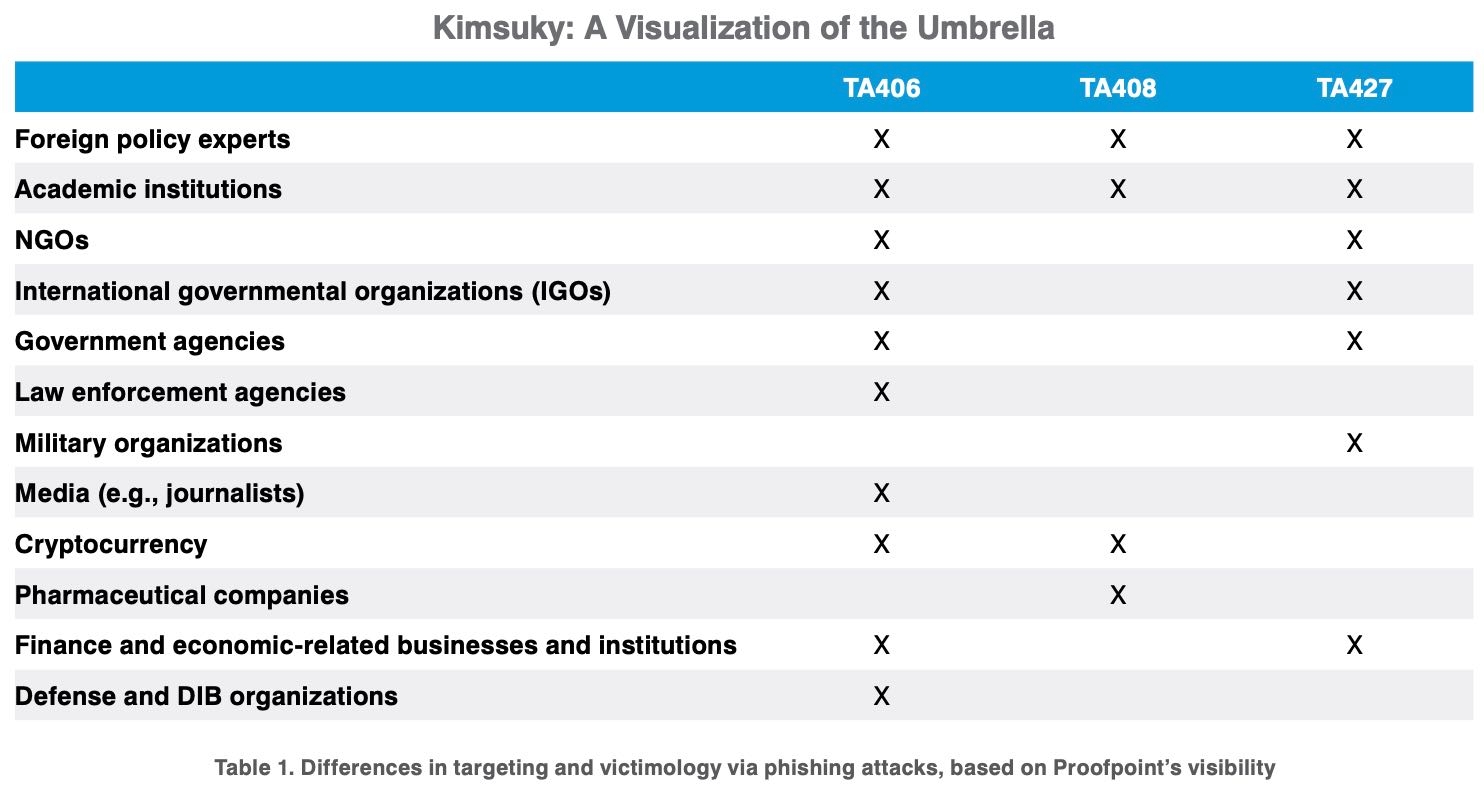
The report compared three subgroups of the sprawling North Korean cyber campaign known as Kimsuky. The effort included TA406, but Proofpoint also described how that group of operators differed from other subgroups, such as TA408 and TA427, which typically focus on a smaller subset of targets. The groups typically target government, academic, media, and organizations linked to cryptocurrency.
The groups have shifted more toward a variety of techniques for harvesting credentials, especially those usernames and passwords for political and financial targets, the report stated.
“TA406 conducts credential-phishing campaigns that target experts at political and foreign policy organizations and NGOs, especially those who are working with or are experts on activities that impact the Korean Peninsula, including nuclear nonproliferation,” Proofpoint stated.
Harvesting Credentials
The attackers use a variety of different messaging platforms, including running their own systems based on PHP servers, such as PHPMailer and Star, but also using major service providers, such as GMail or Yandex, along with stolen or synthetic identities to fool targeted individuals. In some cases, the cyber operations team also used malware to gain persistence in a particular environment.
“Credential harvesting campaigns typically targeted multiple organizations at a time while malware campaigns were deployed in limited, very targeted cases,” DeGrippo says. “In 2021, malware campaigns represented less than 10% of overall activity attributable to TA406.”
Attackers have increasingly focused on credential harvesting as more employees work from home and access cloud services and online infrastructure, often using only a username and password. Credential spraying, where attackers attempt to use stolen or common passwords to gain access to accounts, have skyrocketed in the past year, with more than 193 billion attempted logins in 2020, according to Akamai.
With cloud access becoming increasingly important, the trend has continued in 2021, with access to remote desktop protocol (RDP) servers and virtual private network (VPN) appliances among the most valuable credentials sold online, according to IBM.

