- I recommend the Pixel 9 to most people looking to upgrade - especially while it's $250 off
- Google's viral research assistant just got its own app - here's how it can help you
- Sony will give you a free 55-inch 4K TV right now - but this is the last day to qualify
- I've used virtually every Linux distro, but this one has a fresh perspective
- The 7 gadgets I never travel without (and why they make such a big difference)
Office 365 phishing campaign leverages Oracle and Amazon cloud services – Cyber Defense Magazine

Experts warn of a new sophisticated phishing scheme for stealing Office 365 credentials from small and medium-sized businesses in the U.S.
The new sophisticated phishing scheme was implemented by threat actors for stealing Office 365 credentials, it leverages both cloud services from Oracle and Amazon for their infrastructure.
The campaign has been active for more than half a year and targeted small and medium-sized businesses in the U.S. and Australia.
Threat actors used to compromise legitimate websites and used them as a proxy chain, This campaign also outstands for the abuse of legitimate services and websites for data exfiltration.
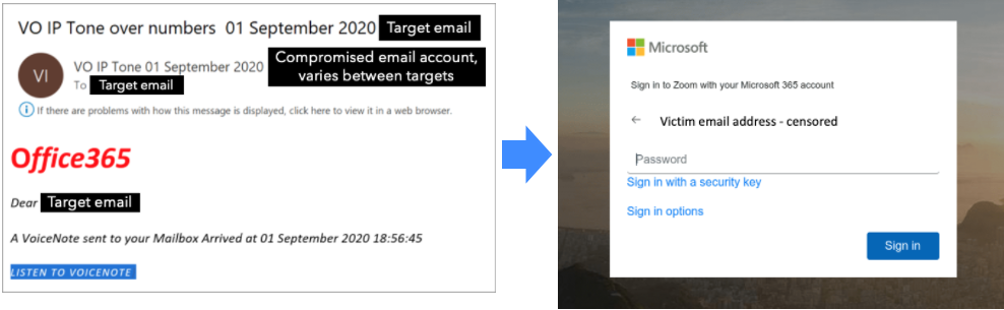
The phishing messages are fake notifications for voice messages and Zoom invitations that are created to trick victims into clicking an embedded link that finally lead the victim to the phishing page that was designed to steal login credentials.
Source Bleeping Computer
According to cybersecurity firm Mitiga, the threat actors used compromised accounts to send out phishing messages and used Amazon Web Services (AWS) and Oracle Cloud in the redirect chain.
“Once the link was clicked, the user is redirected through several proxies, including AWS load balancers, all the way to a legitimate but compromised website” Ofir Rozmann, threat intelligence at Mitiga told Bleeping Computer.
Before the victims land the final landing page, the user is redirected through several proxies, including AWS load balancers.
Most of the fake Office 365 login pages were hosted on Oracle Cloud computing service, but experts also observed the use of Amazon Simple Storage Service (Amazon S3).
Mitiga researchers discovered more than 40 compromised websites that were employed in this Office 365 phishing campaign.
The analysis of the HTML code for the fake Office 365 pages suggests that attackers opted for a phishing-as-a-service.
Based on the email addresses employed in this campaign, Mitiga researchers determined that the campaign mainly aimed at C-level executives at small and medium-sized businesses as well as major financial institutions.
Additional technical details about this campaign, along with Mitiga recommendations to avoid falling victim to these attacks are reported here.