- Want to ditch Windows? This Linux distro makes that transition easy
- Chained Flaws in Enterprise CMS Provider Sitecore Could Allow RCE
- I recommend OnePlus' lateset flagship phone over the S25 Ultra - here's why
- 8 signs that outdated IT systems are killing your business
- Did Samsung's fitness coach just outpace Apple's Workout Buddy?
Oracle July 2021 Critical Patch Update Addresses 231 CVEs
Oracle addresses 231 CVEs in its third quarterly update of 2021 with 342 patches, including 49 critical updates.
Background
On July 20, Oracle released its Critical Patch Update (CPU) for July 2021, the third quarterly update of the year. This CPU update contains fixes for 231 CVEs in 342 security updates across 26 Oracle product families. Out of the 342 security updates published this quarter, 13% of patches were assigned a critical severity. Medium severity patches accounted for the bulk of security patches at 45.5%, followed by high severity patches at 36.8%.
This quarter’s update includes fixes for 49 critical issues across 30 CVEs.
| Severity | Issued Patched | CVEs |
|---|---|---|
| Critical | 49 | 30 |
| High | 158 | 85 |
| Medium | 123 | 105 |
| Low | 12 | 11 |
| Total | 342 | 231 |
Analysis
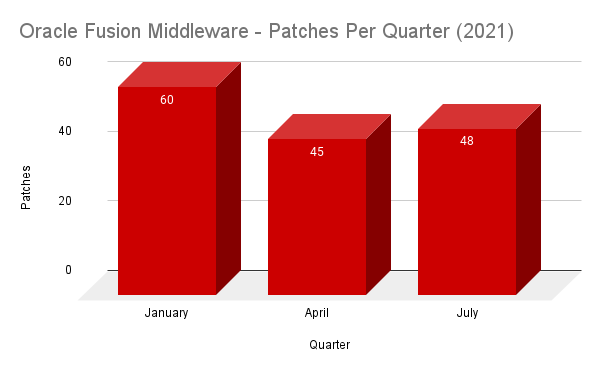
This quarter, the Oracle Fusion Middleware product family contained the highest number of patches at 48, which accounts for 14% of the total patches. It is unsurprising, considering that Oracle Fusion Middleware is one of the most consistently patched pieces of software that Oracle produces. So far in 2021, Fusion Middleware has received 153 patches.
Of the 48 Fusion Middleware patches this quarter, 35 are remotely exploitable without authentication.
A full breakdown of the patches for this quarter can be seen in the following table:
| Oracle Product Family | Number of Patches | Remote Exploit without Auth |
|---|---|---|
| Oracle Fusion Middleware | 48 | 35 |
| Oracle MySQL | 41 | 10 |
| Oracle Communications Applications | 33 | 22 |
| Oracle Communications | 26 | 23 |
| Oracle Retail Applications | 23 | 15 |
| Oracle Financial Services Applications | 22 | 17 |
| Oracle E-Business Suite | 17 | 3 |
| Oracle Database Server | 16 | 1 |
| Oracle PeopleSoft | 14 | 8 |
| Oracle Commerce | 11 | 8 |
| Oracle Systems | 11 | 9 |
| Oracle Construction and Engineering | 10 | 5 |
| Oracle Essbase | 9 | 8 |
| Oracle JD Edwards | 9 | 8 |
| Oracle Enterprise Manager | 8 | 8 |
| Oracle Food and Beverage Applications | 6 | 0 |
| Oracle Hyperion | 6 | 4 |
| Oracle Java SE | 6 | 5 |
| Oracle Siebel CRM | 6 | 4 |
| Oracle Virtualization | 6 | 1 |
| Oracle Supply Chain | 5 | 5 |
| Oracle Insurance Applications | 4 | 3 |
| Oracle Big Data Graph | 2 | 2 |
| Oracle Hospitality Applications | 1 | 0 |
| Oracle Policy Automation | 1 | 1 |
| Oracle Support Tools | 1 | 1 |
Oracle Patches CVE-2019-2729 in Hyperion Infrastructure Technology
As part of the July 2021 CPU, Oracle released a patch for CVE-2019-2729, a critical deserialization vulnerability in Oracle WebLogic Server that was originally patched in an out-of-band update in June 2019. The vulnerability in Hyperion Infrastructure Technology exists within the Installation and Configuration component. Organizations that use the Hyperion Infrastructure Technology should apply the available patch as soon as possible.
Additional WebLogic Server vulnerabilities patched this quarter
Because WebLogic has previously been a favorite initial access vector for attackers, including ransomware groups like REvil (also known as Sodinokbi), we parse Oracle’s CPUs with a focus on WebLogic vulnerabilities. This quarter, there were six vulnerabilities patched within Oracle WebLogic Server (not including those in third party libraries).
| CVE | Component | CVSSv3 | Remotely Exploitable without Auth |
|---|---|---|---|
| CVE-2021-2382 | Security | 9.8 | Yes |
| CVE-2021-2394 | Core | 9.8 | Yes |
| CVE-2021-2397 | Core | 9.8 | Yes |
| CVE-2021-2376 | Web Services | 7.5 | Yes |
| CVE-2021-2378 | Core | 7.5 | Yes |
| CVE-2021-2403 | Core | 5.3 | Yes |
Three of the six vulnerabilities in WebLogic Server were assigned a CVSSv3 score of 9.8 out of 10, which classifies them as critical. According to its advisory, Oracle says that CVE-2021-2397 also addresses CVE-2020-14756, which was another critical WebLogic Server vulnerability that was originally patched as part of the January 2021 Critical Patch Update.
Proof of concept
At the time this blog post was published, there were no proof-of-concept (PoC) exploits for any of the new WebLogic server vulnerabilities, though we anticipate that researchers may share details in the future. However, there are six PoCs for CVE-2019-2729.
Solution
Customers are advised to apply all relevant patches in this quarter’s CPU. Please refer to the July 2021 advisory for full details.
Identifying affected systems
A list of Tenable plugins to identify these vulnerabilities will appear here as they’re released.
Get more information
Join Tenable’s Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.


