- 2025 Cyber Security Predictions: Navigating the Ever-Evolving Threat Landscape
- Not Just Another List of Top 10 Metrics You Should Measure
- My new favorite headphones for swimming come bundled in a unique charging accessory
- Why I recommend this Windows laptop to creatives and professionals - even if it's meant for gamers
- This HP laptop may be the closest thing to a MacBook Pro for Windows users - and I don't mind it
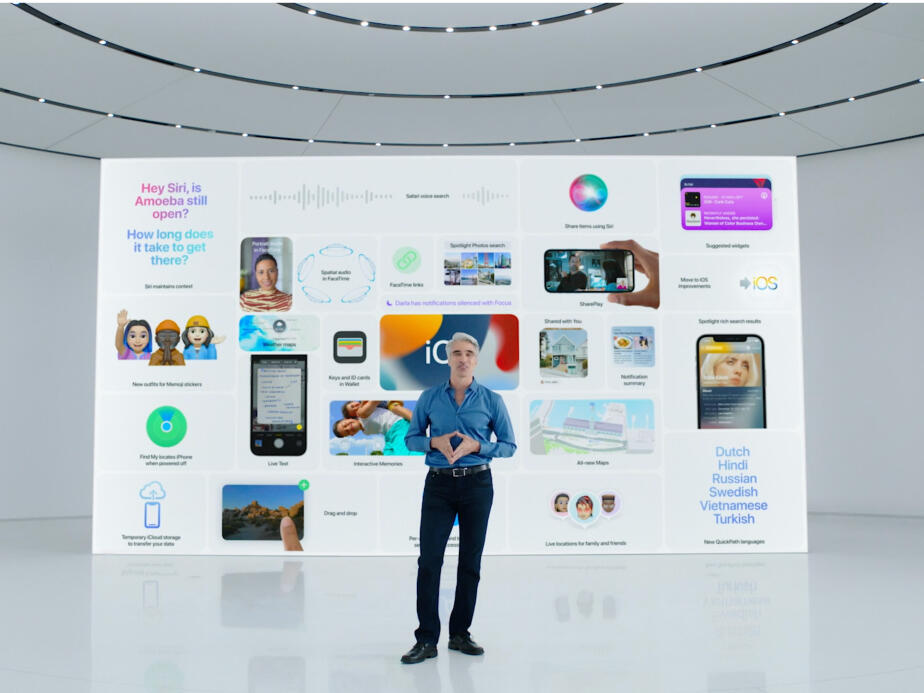
How Our Pharmacy Group Has Readied Secure HIPAA-Compliant WFH Policies
If anticipating a hybrid or remote workforce in the post-pandemic era, here are three best practices to ensure security By Marshall Frost, VP of Corporate Systems, Avita Pharmacy At our business and certainly across countless others, the COVID-19 pandemic forcibly accelerated work-from-home policies that were already very much on the roadmap. Any forward-looking organization had anticipated future expansion of remote work practices in some capacity. The pandemic demanded implementing such practices – and compressing the…
Read More