- I recommend the Pixel 9 to most people looking to upgrade - especially while it's $250 off
- Google's viral research assistant just got its own app - here's how it can help you
- Sony will give you a free 55-inch 4K TV right now - but this is the last day to qualify
- I've used virtually every Linux distro, but this one has a fresh perspective
- The 7 gadgets I never travel without (and why they make such a big difference)
Protecting Workloads Across Any Cloud and Application…Anywhere!

This blog is authored by Ed McNicholas, Cybersecurity Technical Solutions Architect for the Cisco Global Security Sales Organization
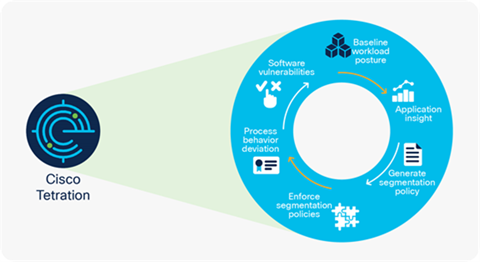
Automating and implementing a secure, zero-trust model for micro-segmentation based on application behavior and telemetry is easy to do using Cisco Secure Workload (formerly known as Tetration). See how your business can seamlessly achieve workload protection by providing:
- Reduced attack surface – Automate micro-segmentation through customized recommendations based on your environment and applications.
- Remain compliant – Granular visibility and control over application components with automatic detection and enforcement of compliance.
- Gain visibility – Track the security posture of applications across your entire environment.
- Enable Zero Trust – Implement a zero-trust model via continuous behavioral monitoring and automated enforcement of micro segmentation policies to every workload
New Cisco Secure Workload Learning Module
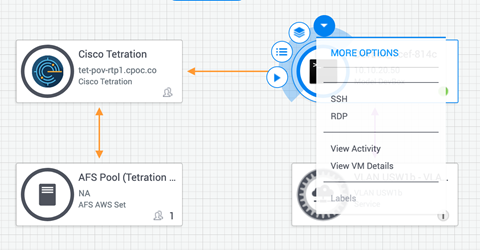
In the new Cisco Secure Workload Learning Module, we will introduce the Open API, which includes easy to use and comprehensive APIs to perform reporting, make configuration changes, export flow data, and more. We will deep dive into the API endpoints that provide visibility and compliance of workloads, application and policy modeling, and deployment of agents and segmentation. We also review how to install and utilize the Secure Workload Python SDK.
In the first lab we will:
- Reserve a sandbox environment to work with
- Clone the necessary code from GitHub
- Setup Postman and Python environments
- Explore simple API requests using Postman and the Python SDK
For the second lab we will cover:
- Query & display all sensors in an application scope
- Download the agent package and configuration files programmatically
- Download & deploy the agent ‘auto-install’ script to an agent in the Secure Workload Sandbox Environment
- Query vulnerabilities on all sensors, identify new vulnerabilities introduced with new sensor
Give the new Learning Module a Try
Learn more about Application First security
Share:

