- Intel appears stuck between ‘a rock and a hard place’
- “언론은 몰려오고, 내부는 혼돈에 빠지고”···CISO가 직접 겪고 깨달은 보안 사고 교훈 8가지
- AI의 상상과 실사 영화의 콜라보···구글, 단편 영화 앤세스트라 제작 과정 공개
- Select Prime members can get Kindle Unlimited for 3 months at no cost - here's how
- Modernization means putting developers in the driver’s seat
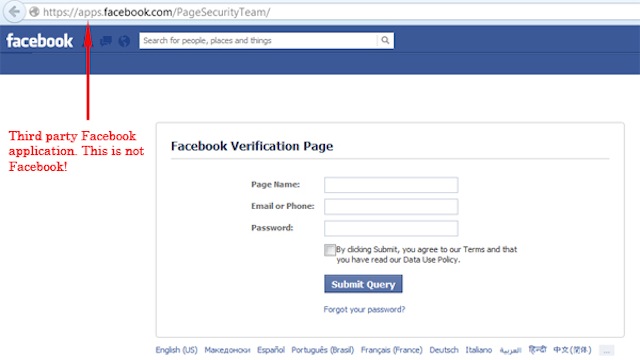
How to Protect Your Social Media Passwords with Multi-factor Verification | McAfee Blog
Two-step verification, two-factor authentication, multi-factor authentication…whatever your social media platform calls it, it’s an excellent way to protect your accounts. There’s a good chance you’re already using multi-factor verification with your other accounts — for your bank, your finances, your credit card, and any number of things. The way it requires an extra one-time code in addition to your login and password makes life far tougher for hackers. It’s increasingly common to see nowadays, where…
Read More