- Your iPad is getting a major upgrade for free. 4 top features I can't wait to try in iPadOS 26
- Your MacBook is getting a big upgrade. 5 best features I can't wait to use in MacOS 26
- The Growing Threat of AI-powered Cyberattacks in 2025
- I test tablets for a living and this is the Samsung tablet I recommend the most
- The Cost of Ignoring Patches: How State and Local Governments Can Mitigate Damaging Security Breaches
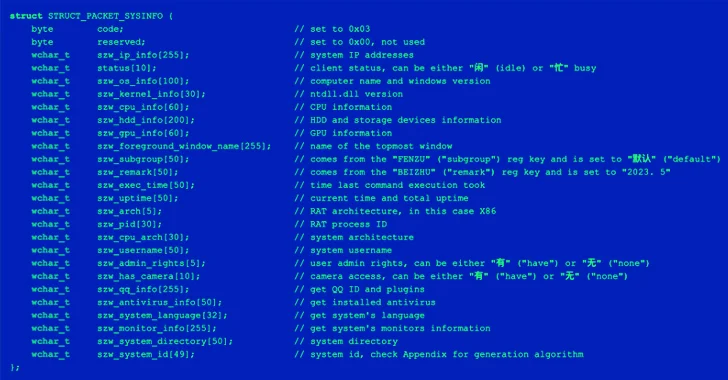
Researchers Detail Bitter APT’s Evolving Tactics as Its Geographic Scope Expands
Jun 05, 2025Ravie LakshmananThreat Intelligence / Network Security The threat actor known as Bitter has been assessed to be a state-backed hacking group that’s tasked with gathering intelligence that aligns with the interests of the Indian government. That’s according to new findings jointly published by Proofpoint and Threatray in an exhaustive two-part analysis. “Their diverse toolset shows consistent coding patterns across malware families, particularly in system information gathering and string obfuscation,” researchers Abdallah Elshinbary, Jonas…
Read More