- I tested Hisense's flagship QLED TV and didn't miss my OLED set (especially when it's $700 off)
- Next-gen AI chips will draw 15,000W each, redefining power, cooling, and data center design
- Amazon extends July Prime Day to four day event, confirms 2025 dates
- Edge reality check: What we've learned about scaling secure, smart infrastructure
- Salesforce study warns against rushing LLMs into CRM workflows without guardrails
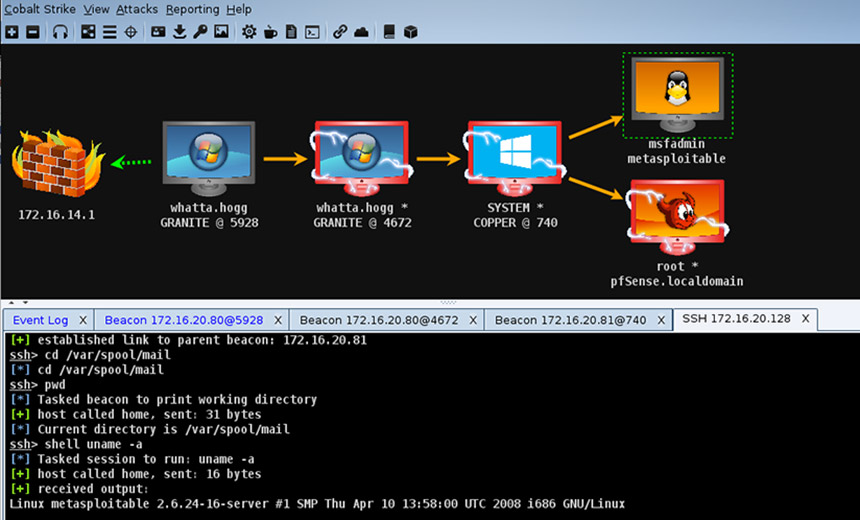
Hackers Using New Malware Packer DTPacker to Avoid Analysis, Detection
A previously undocumented malware packer named DTPacker has been observed distributing multiple remote access trojans (RATs) and information stealers such as Agent Tesla, Ave Maria, AsyncRAT, and FormBook to plunder information and facilitate follow-on attacks. “The malware uses multiple obfuscation techniques to evade antivirus, sandboxing, and analysis,” enterprise security company Proofpoint said in an analysis published Monday. “It is likely distributed on underground forums.” The .NET-based commodity malware has been associated with dozens of campaigns…
Read More

.jpg?height=635&t=1642454744&width=1200)
.jpg?height=635&t=1642437799&width=1200)