- I test tablets for a living and this is the Samsung tablet I recommend the most
- The Cost of Ignoring Patches: How State and Local Governments Can Mitigate Damaging Security Breaches
- I turned this 98-inch TV into an immersive at-home theater system (and it's $1,500 off)
- You can save $30 on the Apple Pencil Pro right now
- I tested this affordable Garmin sports watch, and it shouldn't be this good for the price
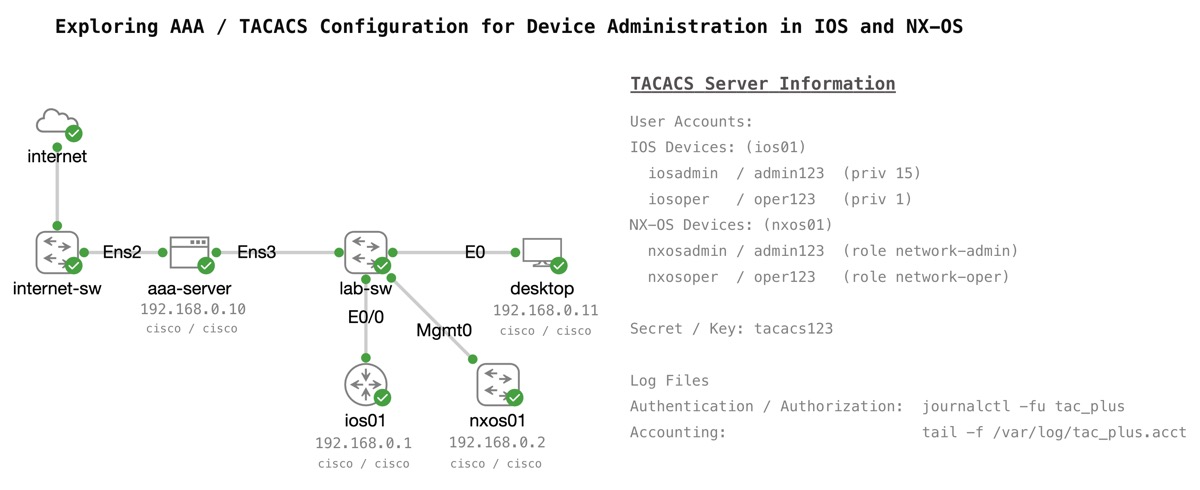
Exploring AAA and TACACS Configuration with Cisco Modeling Labs
I’ll admit to not having done a thorough verification. However, I’d still bet money that AAA/RBAC services are more frequently mentioned on Cisco certification blueprints than any other networking topic. From the CCNA to the Expert level, you’ll find AAA, TACACS+, RADIUS, and RBAC listed on the exam topics. Here is a handful of examples if you’d like to check it out yourself: 200-301 CCNA 2.8 Describe AP and WLC management access connections (Telnet, SSH,…
Read More