- This new YouTube Shorts feature lets you circle to search videos more easily
- I changed 10 Samsung phone settings to give it a significant performance boost
- How practical AI prevailed over hype at Red Hat Summit 2025
- Extreme Networks wants your complicated Wi-Fi environments
- Amazon Prime Day 2025 returns this July: What we know so far
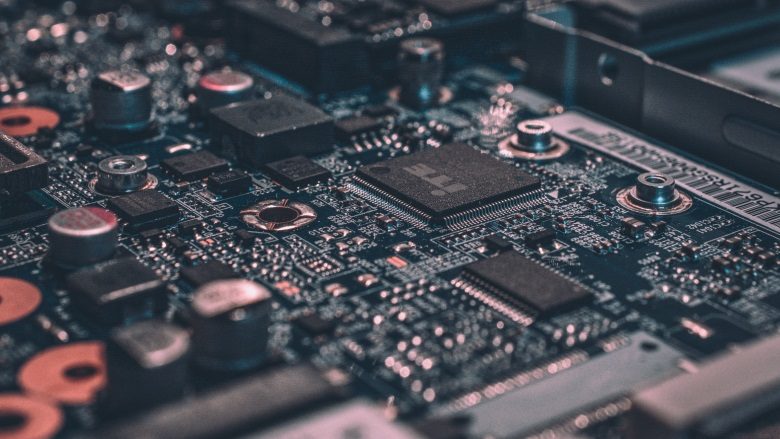
Behind the signal leak: Vulnerabilities in high-security communication
The recent headlines about vulnerabilities in Signal, a messaging app long touted for its end-to-end encryption and privacy-first design, have sent ripples through the cybersecurity and communications worlds. For professionals in communications, marketing, and PR who rely on secure channels to manage sensitive conversations, these revelations are more than just technical footnotes. They raise urgent questions about how secure our “secure” tools really are, and what’s at stake when those tools fall short. The truth…
Read More