- 10 must-try Google Photos tips and tricks - including a new AI editor
- AI could erase half of entry-level white collar jobs in 5 years, CEO warns
- Is all this data about our health good for our health?
- Why I prefer this Lenovo tablet over the iPad for multimedia consumption - and it's $130 off
- This Android tablet brings a $1,700 iPad Pro feature to the $400 price range - and it's just as good
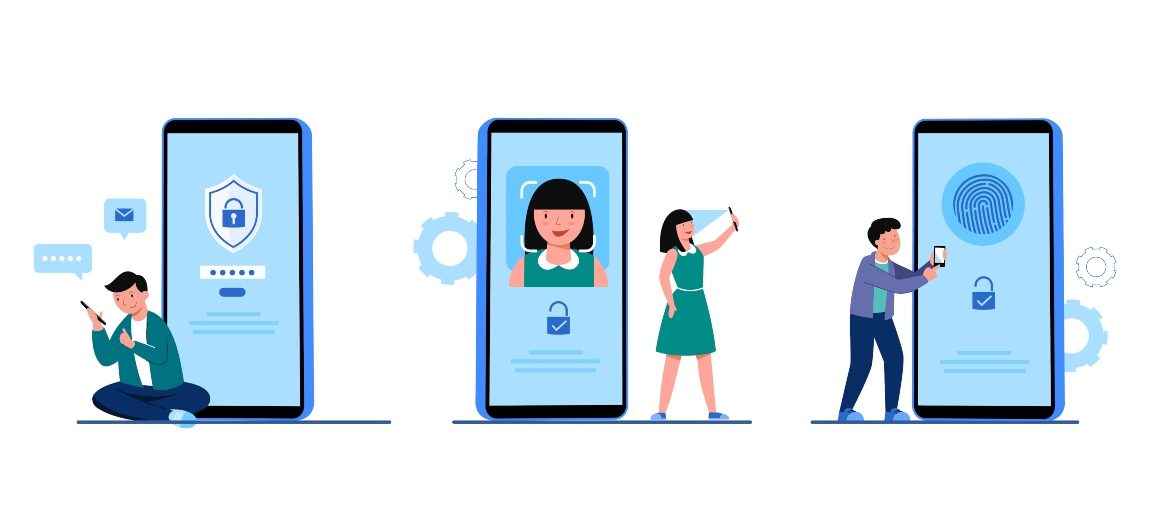
RSA 2025 Product Preview
RSA 2025 takes place from April 28 through May 1 in San Francisco, California, bringing together cybersecurity leaders from all over the country. Security magazine highlights a few products from this year’s RSA exhibitors. 1Password Automatically Generates Passwords 1Password’s built-in password generator creates secure passwords for all online accounts. Users can go passwordless by saving and signing in to compatible websites and apps with passkeys. Save and autofill passwords, two-factor authentication codes, financial addresses, and more in…
Read More