- Your iPad is getting a major upgrade for free. 4 top features I can't wait to try in iPadOS 26
- Your MacBook is getting a big upgrade. 5 best features I can't wait to use in MacOS 26
- The Growing Threat of AI-powered Cyberattacks in 2025
- I test tablets for a living and this is the Samsung tablet I recommend the most
- The Cost of Ignoring Patches: How State and Local Governments Can Mitigate Damaging Security Breaches
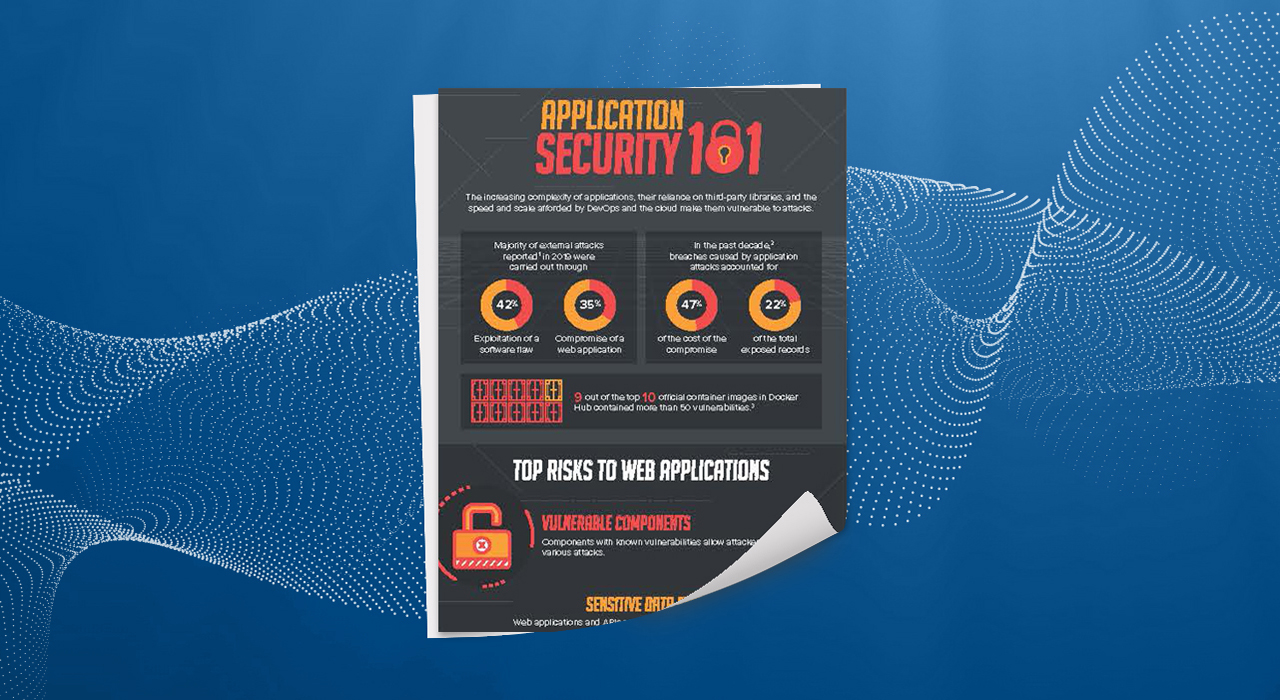
Analyzing How TeamTNT Used Compromised Docker Hub Accounts
Analyzing How TeamTNT Used Compromised Docker Hub Accounts Cloud Following our previous disclosure of compromised Docker hub accounts delivering cryptocurrency miners, we analyze these accounts and discover more malicious actions that you need to be aware of. By: Trend Micro Research December 01, 2021 Read time: ( words) In early November, we disclosed that compromised Docker Hub accounts were being used for cryptocurrency mining and that these activities were tied to the TeamTNT threat actor….
Read More