- How to replace your Windows 11 Start menu with a better alternative - including my favorite
- 1분기 벤처 자금 조달 3년 만에 최고··· AI 독식 완화 조짐
- Samsung's new flagship laptop rivals the MacBook Pro in all the right ways
- Samsung's new flagship laptop rivals the MacBook Pro
- CIOs brace for tariff impacts on tech industry and their businesses
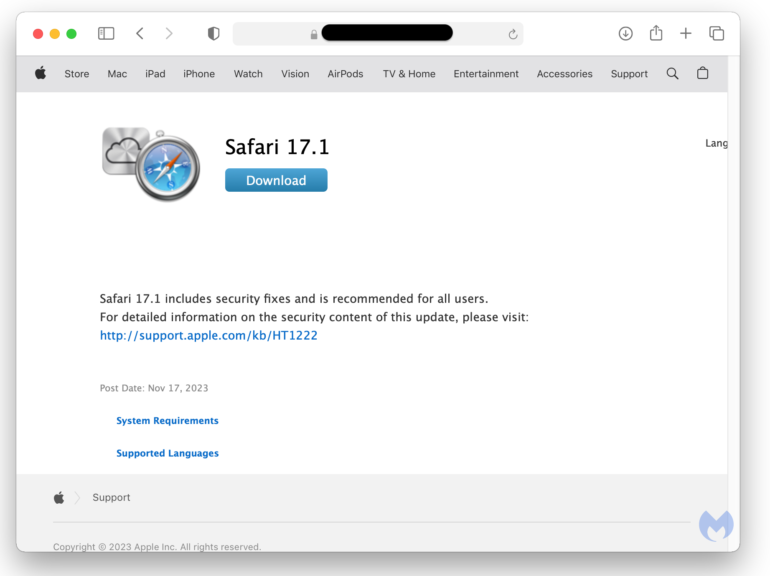
Get Elite Protection from Malware with Award Winning Antivirus – Now $25
Image: StackCommerce TL;DR: Protect your computer from common viruses and other forms of malware, including ransomware and rootkits, with the ESET NOD32 Antivirus 2024 Edition, on sale for just $24.99 through January 14. Cybercrime has long been a problem for businesses. Now that hackers have access to AI and machine learning tech, however, security analysts expect the growth rate to climb exponentially. Are your company’s computers adequately protected for the new year? If not, then…
Read More