- How AI coding agents could destroy open source software
- These Bluetooth trackers are louder and more durable than Apple AirTags - and they're on sale
- Why I recommend this budget Lenovo ThinkPad over laptops that cost twice the price
- AI agents make great teammates, but don't let them code alone - here's why
- Java at 30: How a language designed for a failed gadget became a global powerhouse
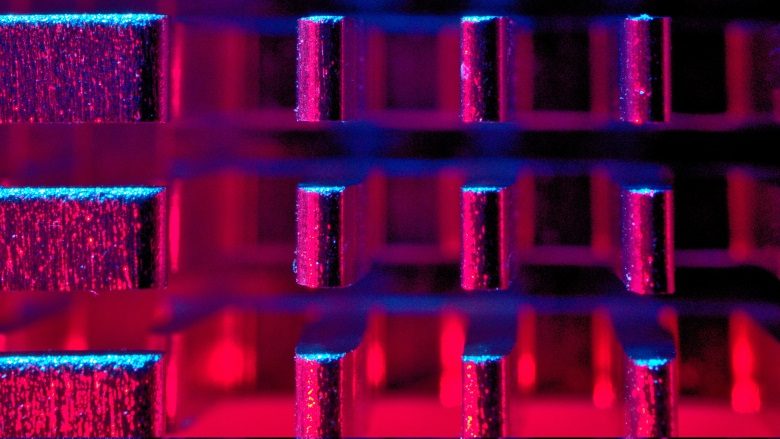
Cyber assets increased by 133% year-over-year
Cyber assets increased by 133% year-over-year | Security Magazine This website requires certain cookies to work and uses other cookies to help you have the best experience. By visiting this website, certain cookies have already been set, which you may delete and block. By closing this message or continuing to use our site, you agree to the use of cookies. Visit our updated privacy and cookie policy to learn more. This Website Uses CookiesBy…
Read More