- Nvidia aims to bring AI to wireless
- Anthropic's new AI models for classified info are already in use by US gov
- My cat loves this automatic wet food feeder, and it's on sale
- Certified and Unstoppable: Recertify with Rev Up
- Walmart's drone delivery spreads its wings to 100 more stores - is yours one?
Vulnerabilities Targeting InfiRay Thermal Cameras May Result in Industrial Process Hacking
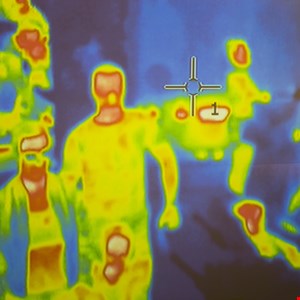
Austrian cybersecurity firm SEC Consult found a series of vulnerabilities affecting Infiray IRAY-A8Z3 thermal cameras in February 2021.
The consulting company disclosed the details of the vulnerabilities in an advisory on Tuesday, saying they were a direct consequence of insecure coding practices, insecure configuration and outdated software components within the embedded firmware
SEC Consult also said it found multiple attack vectors that will result in remote code execution (RCE).
For context, InfiRay is a China-based manufacturer of optical components, particularly infrared and thermal imaging solutions. Its products are currently sold in 89 countries and regions around the world.
Because of the broad reach of its products, the discovered flaws could potentially act as an entry point into industrial control systems (ICS) and supervisory control and data acquisition (SCADA) networks.
In terms of critical vulnerabilities affecting the Infiray IRAY-A8Z3 cameras, SEC Consult mentioned five. The first refers to the hardcoded credentials for the camera’s web application.
“As these accounts cannot be deactivated or change their passwords, they are considered to be backdoor accounts.”
Secondly, the company said the cameras’ web server interface contains an endpoint that can execute arbitrary commands by manipulating the “cmd_string” URL parameter, thus enabling user login using one of the aforementioned backdoor accounts.
The third issue refers to a potential buffer overflow attack that could be executed by calling strcpy() without checking the string length first.
Fourthly, the camera reportedly offers a shell through a telnet connection.
“The root user does not require a password per default. Thus, anyone on the local network can execute arbitrary commands as root on the camera.”
Finally, SEC Consult said the cameras have multiple outdated software components containing vulnerabilities that were found using the IoT Inspector (OneKey) firmware analysis platform.
The security company contacted InfiRay multiple times during its investigation, sending them a draft of the advisory in April 2021, but the vendor never responded to its requests.
Because of this, SEC Consult warned it was unaware whether the vendor had patched the affected systems or not.
“The vendor was unresponsive during the disclosure process. Hence it is unclear whether patches are available. Customers are urged to approach their vendor contact and request security reviews and updates.”

