Why You Need XDR in Today’s Threat Landscape

Detection and Response
Trend Micro’s VP of Threat Intelligence, Jon Clay, explores the latest trends in today’s threat landscape and why XDR is key to enabling more resilience.
Read time: ( words)
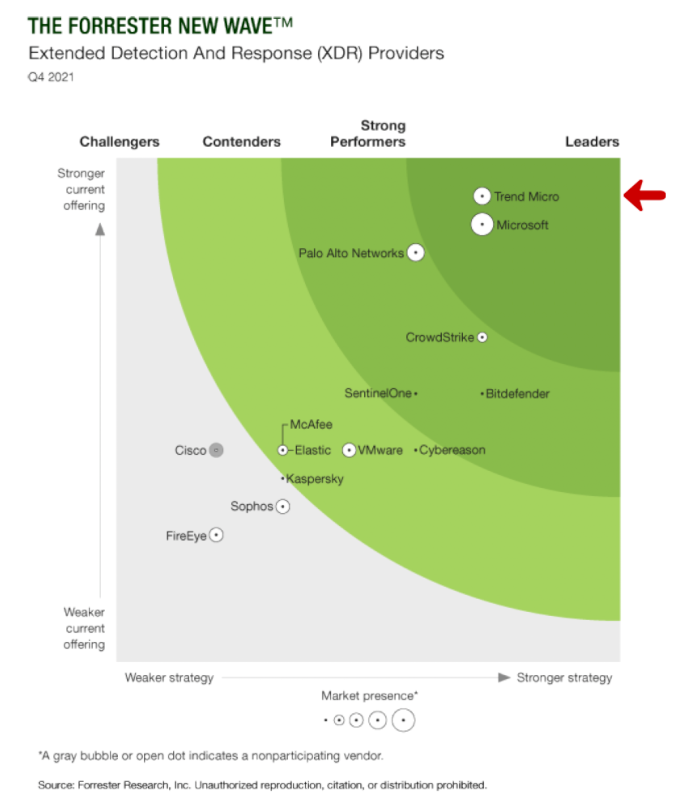
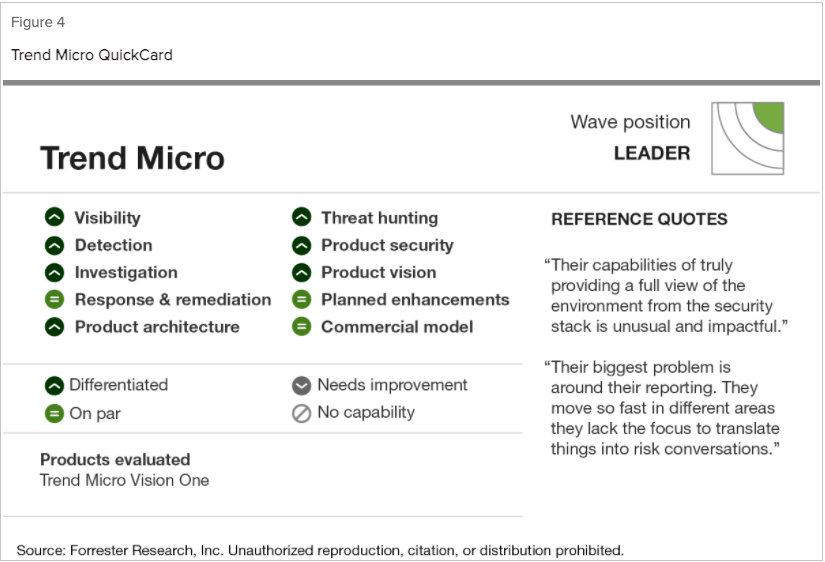
I’m proud to share the Forrester New Wave™: for Extended Detection and Response (XDR) that named Trend Micro a Leader in both current offerings and strength of strategy. I’d like to explore why it’s important for organizations to leverage threat operations platforms with XDR capabilities to protect themselves against evolving threats.
Current threat landscape trends
With the recent rash of ransomware attacks, we’re seeing more effective malicious actors who are successfully targeting their victims. How are they able to do this? Here are some key factors enabling their success:
- There is a lot of up-front intelligence gathering by the malicious actors to determine who they want to target, why the want to target them, and how, where, and when do they want to launch their attacks. All of these will be nailed down prior to the attack occurring, making their attacks smoother and harder to catch.
- In many cases, the attack campaign is being orchestrated through collaboration within different groups: Access as a service teams (initial access brokers) will work with a team that is very good at lateral movement. After the network has been compromised, they sell access to a ransomware as a service affiliate who may initially steal data to extort and then launch their ransomware infection.
- These attacks will cross many areas of the network. They may start at an employee’s system via phishing, or an open IP they compromise, but very quickly after mapping the network, they will laterally move to data centers, cloud infrastructures, OT networks. They will also utilize email, web, exploits, and other attack surfaces.
- Counter incident response will be utilized throughout the attack to ensure their activities are not seen by defenders. Legitimate tools will be used maliciously to hide their tracks in this living off the land tactic.
- Multiple extortion models will be incorporated that could include data stealing, DDoS, ransomware, and even contacting your customers to put pressure on you to pay their extortion fees.
XDR: The missing piece of the security puzzle
Organizations are dealing with adversaries that are well coordinated and their success rate has been growing over the years. Weaknesses in an enterprise’s security strategy and infrastructure also lend a hand to making attacks more successful.
Namely, existing security infrastructure tends to be siloed across their network. Lack of integration and collaboration between independent security solutions causes too many alerts without context, overwhelming defenders and diminishing their visibility across the entire network.
This is where XDR makes a difference—it improves defense and minimizes dwell time of the adversary within their network by integrating security between endpoints, email, web, servers, cloud environments and across network traffic. This integration allows defenders to identify and correlate attacks that are happening in different areas of the network to deliver information about an ongoing attack. Correlated data leads to less, but highly actionable alerts, reducing the time it takes an organization to respond and remediate an ongoing attack.
Leveraging the Forrester New Wave™ report
We invite you to read the latest Forrester report to make an informed decision when choosing an XDR vendor. Trend Micro was evaluated against 10 criteria alongside the most significant XDR providers including Microsoft, McAfee, and Crowdstrike. The report also provides customer references for more insight beyond the analyst evaluations.
Tags
sXpIBdPeKzI9PC2p0SWMpUSM2NSxWzPyXTMLlbXmYa0R20xk

