- I recommend the Pixel 9 to most people looking to upgrade - especially while it's $250 off
- Google's viral research assistant just got its own app - here's how it can help you
- Sony will give you a free 55-inch 4K TV right now - but this is the last day to qualify
- I've used virtually every Linux distro, but this one has a fresh perspective
- The 7 gadgets I never travel without (and why they make such a big difference)
WPA3: Bringing Robust Security for Wi-Fi Networks – Cisco Blogs

Wi-Fi Alliance now requires all new Wi-Fi CERTIFIED devices to support WPA3 security. In 2021 the industry will see greater adoption of WPA3 across more devices, networks, and environments – including sensitive environments like governments and financial institutions. The number of devices connected to the internet, including machines, sensors, and smart home devices is forecast to reach 41.6 billion in the next four years.
With the increase in number of devices and Wi-Fi adoption, there is an implicit need for better security. It is a common practice today to use the personal devices like mobile phones, tablets etc interchangeably between home and office. The security requirements and the associated constraints for enterprise and personal networks are different. Users enter password for accessing home network deployments while in enterprise, they use stronger security methods requiring username and password, or certificates.
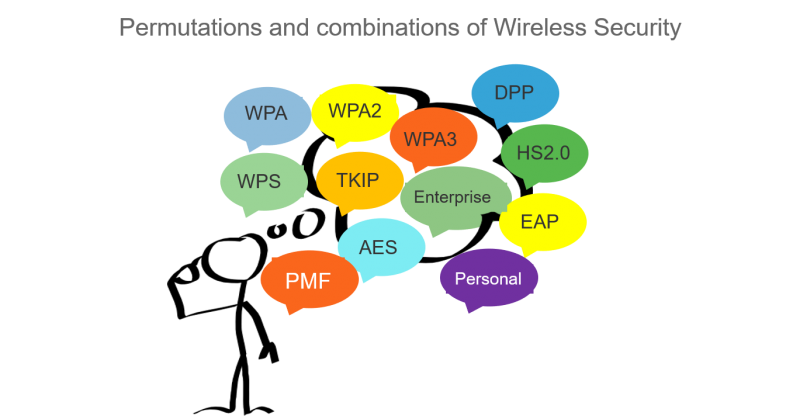
Such constraints and change in usage have led to an evolution of wireless security standards.
WPA3 Evolution
Wi-Fi Protected Access (WPA) has evolved over the course of many years. Wi-Fi Alliance started working upon WPA3 to circumvent the vulnerabilities surfaced in the WPA2 security.
In beginning of 2018 Wi-Fi Alliance announced the new security enhancements for Wi-Fi Protected Access under the umbrella of WPA3. WPA3 security defined new authentication and encryption algorithms for both Personal and Enterprise networks overcoming the shortcomings of WPA2.
WPA3 Technology
Legacy Wi-Fi security methods does have multiple security options to configure and thus can lead for operator to choose non optimal security configurations.
WPA3 security overcomes this limitation and does not allows TKIP and WEP. Additionally, WPA3 personal and enterprise connections requires PMF (Protected Management Frame) negotiation mandatorily. PMF provides an additional layer of protection from de-authentication and disassociation attacks.
Personal Networks–
- For personal networks WPA3 utilizes Simultaneous Authentication Of Equals (SAE) as described in IEEE 802.11 standard.
- SAE provides following key advantages when compared to WPA2 PSK (pre-shared key): –
- Creates shared secret which is different for each SAE authentication.
- Protection against brute force “dictionary” attacks and passive attacks.
- Provides forward secrecy
- In 2019 the Dragonblood paper revealed that certain theoretical vulnerabilities in SAE were feasible to exploit in practice, enabling an active attacker to recover the password using side channel attacks. In response to the Dragonblood paper, IEEE 802.11 updated SAE by defining a new “Hash-to-Element” (H2E) method, as an optional alternative to the existing “Hunting-and-Pecking” method for the secret PWE (Password Element) derivation used in SAE authentication. H2E is significantly more computationally efficient and provides robust resistance to side channel attack.
Enterprise networks –
- WPA3-Enterprise 192-bit mode is well suited for deployments in sensitive enterprise environments to further protect Wi-Fi networks with higher security requirements such as government, defense, and industrial. This level of security provides consistent cryptography and eliminates the “mixing and matching of security protocols” that are defined in the 802.11 standard.
- For WPA3-Enterprise only mode recently Wi-Fi alliance has also added restrictions to avoid usage of authentication key management IEEE 802.1X with SHA-1 and thus driving operators to use at least IEEE 802.1X with SHA-256 for better security.
WPA3 Transition Modes –
- Ease of network upgrade – WPA2 devices has been there for many years in Wi-Fi networks and therefore it was important to have mode of deployment where both WPA2 and WPA3 devices can co-exist. This certainly helps in Wi-Fi networks to migrate gradually from WPA2 towards WPA3 based networks. Wi-Fi alliance has introduced the WPA3 Transition modes for both personal and enterprise networks. With transition mode enabled on SSID both WPA2 and WPA3 supporting devices can connect simultaneously thus paving path for gradual migration of device echo-system from WPA2 to WPA3.
- Transition Disable – With above ease of network upgrade using transition mode comes the security challenge of WPA3 STAs (stations) undergoing downgrade attacks. The attackers can force WPA3 STAs downgrade to use the WPA2 and legacy security vulnerable technologies. To circumvent this problem Wi-Fi alliance has introduced “Transition Disable” indication using which AP and network operator can update WPA3 STAs that the network is fully upgraded to support the most secured algorithm defined in a transition mode. Transition Disable indication is used (in 4-way handshake during association) to disable transition modes for that network on a STA, and therefore provide protection against downgrade attacks. STAs on receiving this indication shall disable use of WEP, TKIP and will disallow association without negotiation of PMF.
Enhanced Open –
- In public places like restaurants and shopping malls Wi-Fi networks are often “Open” —sometimes directly, sometimes based on a simple web signup page. In “Open” networks eavesdropper has visibility to unencrypted Wi-Fi traffic. It will be better if we do have Wi-Fi traffic encrypted though from user perspective the interface or ease of use remains same. For such deployments Wi-Fi alliance has introduced Enhanced Open which uses Opportunistic Wireless Encryption (OWE) for encrypting the traffic based on Diffie Hellman key exchange done as part of Association. Initially OWE was marketed under WPA3 security enhancements however now it has separate Enhanced Open certification.
WPA3 Adoption
WPA3 has become mandatory for Wi-Fi 6E deployments. Users will see worldwide rollout of Wi-Fi 6E devices as multiple vendors embrace 6 GHz. Up to seven super wide 160 MHz channels can be used with this newly available spectrum, triggering development and innovation for higher bandwidth applications including unified communications, AR/VR, and even holographic video. New use cases will emerge to support telemedicine, virtual learning, and telepresence that rely on Wi-Fi 6E’s speed and latency benefits. All these deployments shall be utilizing the WPA3 security enhancements.
Customers have already started migrating their networks to WPA3 security and approximately 60% of Cisco Catalyst and Aironet Access Points Wi-Fi deployments have WPA3 security being used which is a good adoption rate.
Cisco helping customers with WPA3 deployments
Cisco provides complete solution for WPA3 with Cisco Wireless Stack including Cisco Catalyst Access Points , Catalyst Wireless LAN Controllers, Cisco DNA Centre and Cisco Aironet Active Sensors supporting comprehensive set of WPA3 features. This is also supported on previous generation of Access points and controllers namely Cisco Aironet Access Points and Controllers
- Cisco Catalyst and Aironet Access Points, wireless LAN controllers supports WPA3 for Personal, Enterprise networks and supports Enhanced Open (OWE). Customers are already happily migrating to WPA3 security using cisco offering.
- Cisco Aironet Active Sensors also supports WPA3 and will be playing critical role in WPA3 deployments as operators can run on demand and scheduled tests with sensors connecting as WPA3 clients, performing different WPA3 use-cases and isolating upfront any network connectivity issues pertaining to WPA3. These tests are helpful during Cisco Wireless controller and Access Point software upgrades and periodically performing tests in customer network environment.
- Cisco DNA center provides network automation, management and assurance functionality for WPA3 features thus enabling operators for End-to-End network management.
Summary
WPA3 has brought in significant security enhancements and is critical for networks to upgrade using WPA3 security. Wi-Fi 6E and Wi-Fi Alliance mandating WPA3 for all new Wi-Fi certified devices will be critical drivers for the adoption of WPA3.
Cisco Catalyst Access Points and Catalyst Wireless LAN Controllers already supports WPA3, please stay tuned for ongoing additions of new WPA3 enhancements via a software upgrade so that our existing and new customers continue to take advantage of new WPA3 capabilities.
Check out our Cisco Networking video channel
Subscribe to the Cisco Networking blog
Share: