- Extreme Networks wants your complicated Wi-Fi environments
- Amazon Prime Day 2025 returns this July: What we know so far
- This hidden Google Earth slider lets you travel up to 80 years back in time. Here's how to try it
- Revolutionizing the Partner Training Experience with Cisco Xpert
- Mandatory Ransomware Payment Disclosure Begins in Australia
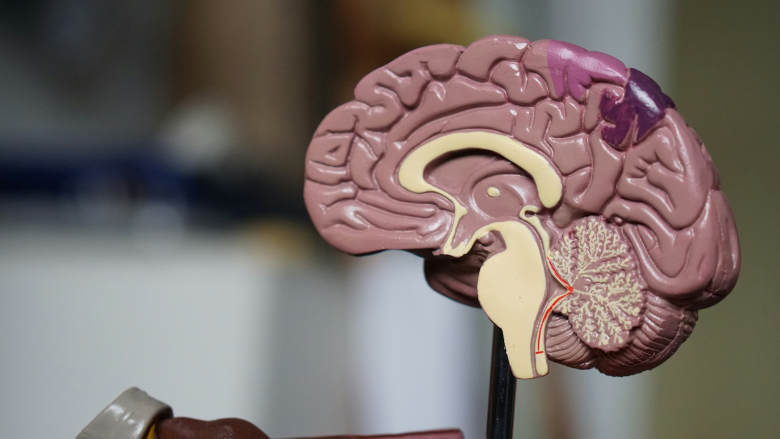
Humans in AI: The necessity for human-in-the-loop (HILT)
A deliberate approach is essential for AI to be net positive, and that human-in-the-loop (HILT), and its natural successor reinforcement learning from human feedback (RLHF), are essential components of this. What is HILT? To understand HILT, we must first understand machine learning. Machine learning is when the computer is able to learn from data. LLM (large language model) chatbots are made possible by machine learning. A concrete and easy to understand example of machine…
Read More