- Apple Intelligence hasn't lived up to my expectations, but these 3 upgrades could win me back
- Samsung launches One UI 8 beta - what's new and how to join
- This 230-piece Craftsman toolset is still just $99 at Lowe's
- Grab this 85-inch Samung TV and home audio bundle for $2,500 off
- Standing Together Against Scams: McAfee Joins the Global Anti-Scam Alliance | McAfee Blog
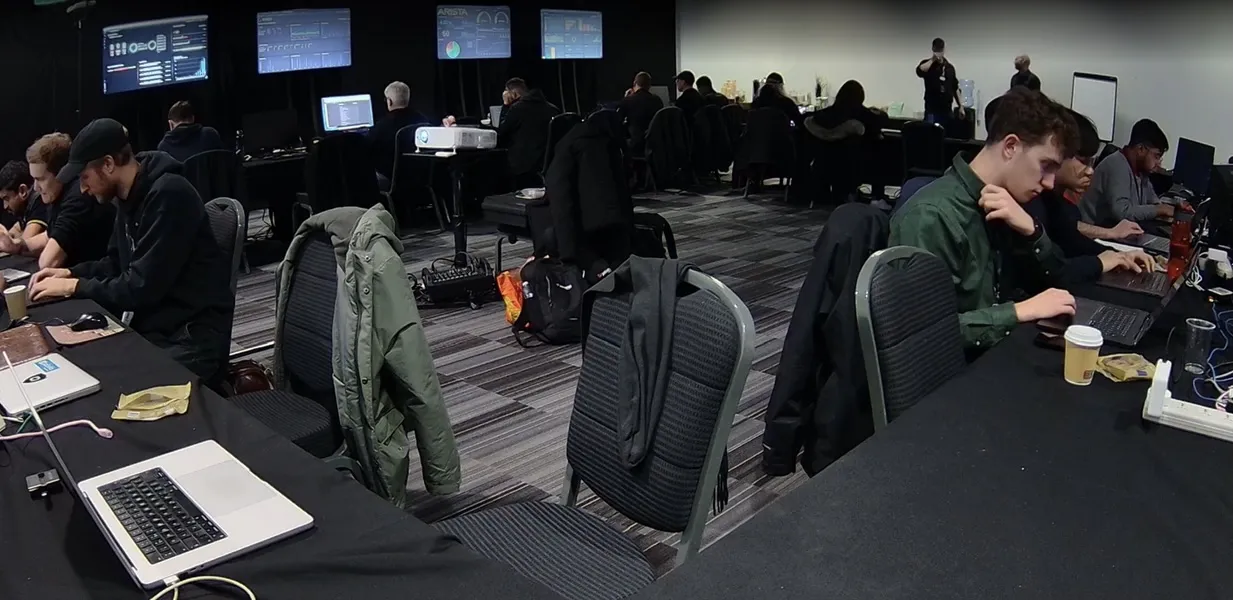
Cisco Live Melbourne SOC Report
Executive Summary Cisco has long provided security services for third party events such as the Black Hat and RSA Conferences, as well as the Super Bowl and the Olympic games. These services come in the form of products (Cisco Security Cloud capabilities, including Umbrella, XDR, Malware Analytics, etc. plus Splunk Enterprise Security); and skilled Security Operations Centre (SOC) analysts, who build and operate the infrastructure and hunt for threats, from both inside and outside the…
Read More